
Vulnerability And Risk Management under the Cyber Resilience Act is not just about compliance, it is about building systems that can withstand real threats. We have seen organizations succeed when structured processes meet real execution.
From identifying vulnerabilities to fixing them quickly, every step matters. This guide explains how to align with requirements while staying effective in practice. Keep reading to understand how vulnerability & risk management works in real scenarios.
Key Insights on Vulnerability And Risk Management
Before exploring the details, these points highlight what matters most in vulnerability and risk management:
- Strong processes outperform complex tools
- Secure Coding Practices reduce risks early
- Continuous monitoring ensures resilience
Understanding Vulnerability Handling Cyber Resilience Act
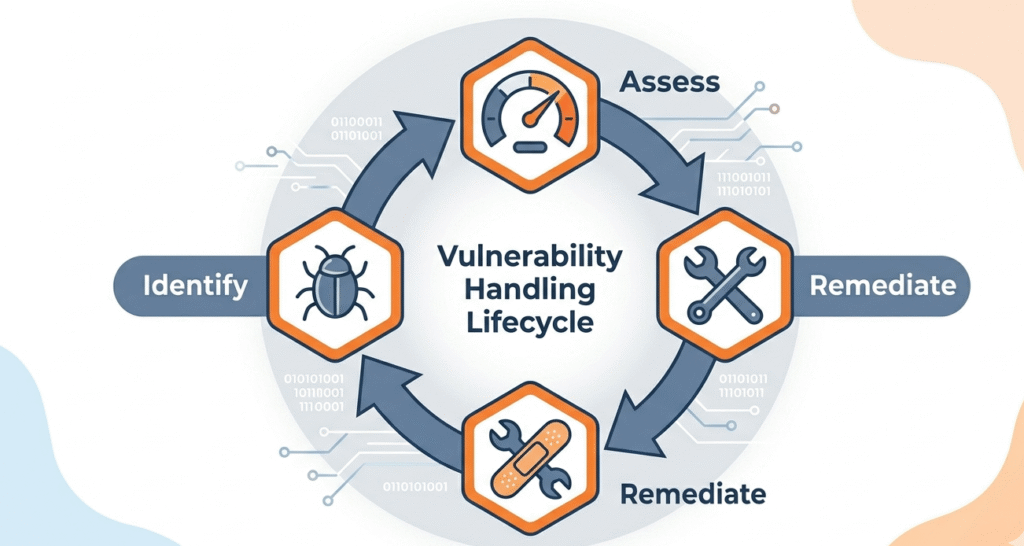
Vulnerability handling cyber resilience act requires structured processes to identify, assess, and remediate risks. Many teams rely too heavily on tools, but execution is what truly matters.
“A vulnerability is a weakness which can be exploited by a threat actor.” – Wikipedia
From our experience, organizations improve faster when ownership is clearly defined.
Key elements include:
- Continuous vulnerability scanning
- Risk-based prioritization
- Defined remediation timelines
- Post-fix verification
Cyber Resilience Act Vulnerability Disclosure
Cyber resilience act vulnerability disclosure ensures transparency between organizations, users, and authorities. A clear disclosure process reduces the chance of risk escalation.
We have seen that simpler systems are used more consistently than complex ones.
Best practices:
- Public disclosure policy
- Defined response timelines
- Secure reporting channels
- Collaboration with researchers
Patch Management Requirements Cyber Resilience Act
Credits: PurpleSec Clips
Patch management requirements cyber resilience act focus on maintaining system security through timely updates. Delayed patching remains a major vulnerability factor.
We emphasize Secure Coding Practices early because preventing issues reduces patch dependency later.
Patch management steps:
- Maintain asset inventory
- Prioritize critical patches
- Test before deployment
- Monitor compliance
Cyber Resilience Act Incident Reporting
Cyber resilience act incident reporting requires fast and accurate reporting of significant incidents. This strengthens overall cybersecurity coordination.
In practice, delays often come from unclear escalation paths.
Essential components:
- Defined severity levels
- Clear reporting timelines
- Internal escalation procedures
- Accurate documentation
Software Supply Chain Security EU
Software supply chain security eu addresses risks from third-party components and vendors. Many vulnerabilities originate outside internal systems.
“Supply chain attacks exploit trust relationships between organizations and their suppliers.” – ResearchGate
We have seen organizations overlook this until incidents occur.
Security measures include:
- Vendor risk assessments
- Dependency tracking
- Software bill of materials (SBOM)
- Continuous monitoring
Role of Secure Coding Practices in Vulnerability And Risk Management
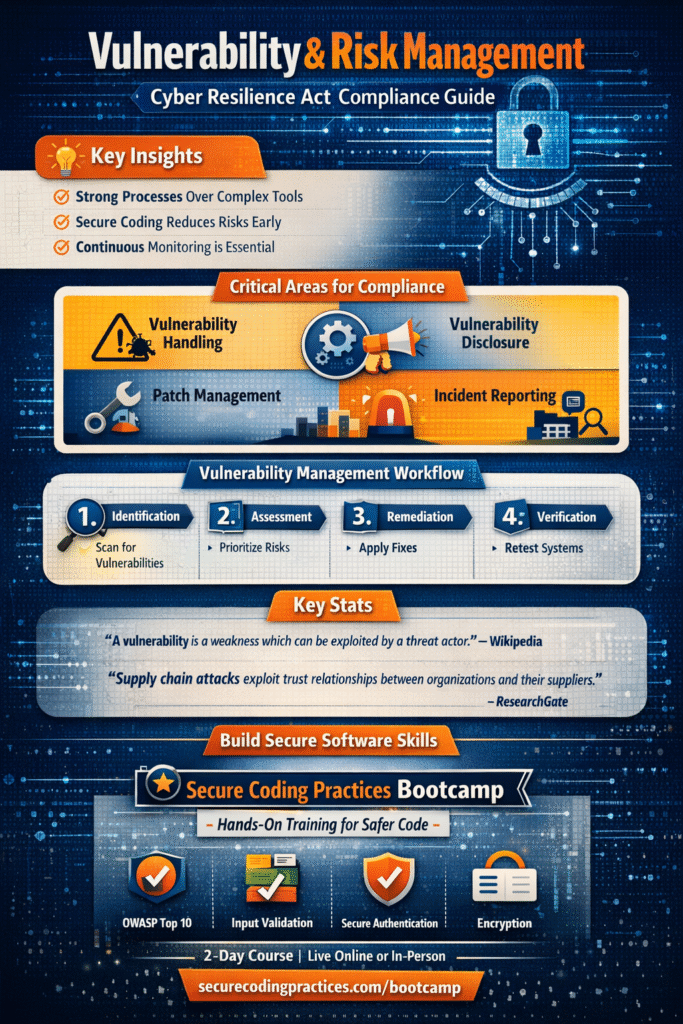
We position Secure Coding Practices as the first step in vulnerability and risk management. Building secure code reduces the number of vulnerabilities from the start.
This approach is not about perfection but consistent improvement across development cycles.
Core practices:
- Input validation
- Secure authentication
- Data protection
- Regular code reviews
Vulnerability And Risk Management Workflow
| Stage | Action | Result |
| Identification | Scan systems | Detect vulnerabilities |
| Assessment | Prioritize risks | Focus on critical issues |
| Remediation | Apply fixes | Reduce exposure |
| Verification | Retest systems | Ensure effectiveness |
| Reporting | Document outcomes | Maintain compliance |
Common Challenges in Vulnerability & Risk Management
In our experience, challenges often come from coordination gaps rather than lack of tools.
Common issues and solutions:
- Unclear ownership → Assign clear roles
- Slow patching → Automate workflows
- Limited visibility → Centralize monitoring
- Weak communication → Standardize reporting
FAQ
What is vulnerability handling cyber resilience act?
It refers to structured processes for identifying, assessing, and fixing vulnerabilities under the Cyber Resilience Act. Organizations must ensure continuous monitoring, proper prioritization, and timely remediation to reduce risks and maintain secure systems in real conditions.
How does cyber resilience act vulnerability disclosure work?
Cyber resilience act vulnerability disclosure requires organizations to report vulnerabilities responsibly. This includes clear policies, communication channels, and response timelines. It ensures transparency and allows faster action to prevent exploitation.
What are patch management requirements cyber resilience act?
Patch management requirements cyber resilience act focus on timely updates and system maintenance. Organizations must track assets, prioritize patches, test updates, and ensure deployment to reduce exposure to known vulnerabilities.
What is cyber resilience act incident reporting?
Cyber resilience act incident reporting involves notifying authorities about significant cybersecurity incidents within defined timelines. It includes classification, documentation, and escalation procedures to improve response coordination.
Final Thought on Vulnerability & Risk Management
The Secure Coding Practices Bootcamp offers hands-on, two-day training focused on practical skills like input validation, encryption, and the OWASP Top 10. Designed for developers, the course skips the jargon, providing real-world labs, cheatsheets, and certification to help you ship safer code immediately.
Whether you’re an individual or part of a corporate team, this expert-led program builds essential security habits through live, interactive sessions. Ready to master secure coding? Join the Bootcamp today!
References
- https://en.wikipedia.org/wiki/Vulnerability_(computing)
- https://www.researchgate.net/publication/Supply_Chain_Attacks
Related Articles
- https://securecodingpractices.com/vulnerability-handling-cyber-resilience-act/
- https://securecodingpractices.com/cyber-resilience-act-vulnerability-disclosure/
- https://securecodingpractices.com/patch-management-requirements-cyber-resilience-act/
- https://securecodingpractices.com/cyber-resilience-act-incident-reporting/
- https://securecodingpractices.com/software-supply-chain-security-eu/

