Secure Development Lifecycle (SDL) helps us build software with security in mind from the very beginning. In our experience, ignoring security early often leads to higher risks, costly fixes, and compliance challenges later. With regulations like the Cyber Resilience Act, organizations must now integrate security into every stage of development.
Starting with Secure Coding Practices makes this process more manageable and effective. It creates a strong foundation without adding unnecessary complexity. If you want to understand how SDL aligns with compliance and practical workflows, keep reading.
Secure Development Lifecycle Key Insights
Before diving deeper, here are the most important points we’ve learned from applying Secure Development Lifecycle in real scenarios:
- SDL integrates security into every phase of development
- Secure Coding Practices help reduce vulnerabilities early
- Cyber Resilience Act requires continuous risk assessment and secure updates
What is Secure Development Lifecycle?
Secure Development Lifecycle is a structured approach to building secure software from planning to maintenance.
“The S-SDLC model focuses on the incorporation of security in any type of SDLC… which entails a series of benefits, among which can be mentioned: early detection of faults, coding errors, design weaknesses, [and] cost reduction derived from an early detection and resolution.” – MDPI
Instead of adding security at the end, we integrate it into:
- Planning and requirements
- System design
- Development and coding
- Testing and validation
- Deployment and maintenance
Many teams align SDL with software risk management cra to meet both technical and regulatory expectations. From our experience, this reduces last-minute fixes and improves overall software quality.
Cyber Resilience Act Secure Development Lifecycle
The cyber resilience act secure development lifecycle requires organizations to ensure security throughout the product lifecycle.
“Secure by default principles would impose a duty of care for the lifecycle of products, instead of e.g. relying on consumers and volunteers to establish a basic level of security. The new rules would “rebalance responsibility towards manufacturers”.” – Wikipedia
This includes:
- Designing systems with security in mind
- Maintaining proper documentation
- Monitoring and addressing vulnerabilities continuously
Teams that already apply SDL usually adapt faster. Others often struggle because they treat compliance as a separate process rather than integrating it into development workflows.
Secure Coding Requirements Cyber Resilience Act
Credits: Whiteboard Security
The secure coding requirements cyber resilience act focus on minimizing vulnerabilities during development.
We usually begin with Secure Coding Practices because they are practical and effective:
- Strong input validation
- Proper authentication and authorization
- Avoiding insecure dependencies
In our experience, improving coding habits early significantly reduces risks. It also simplifies testing and compliance later in the lifecycle.
Risk Assessment Requirements Cyber Resilience Act
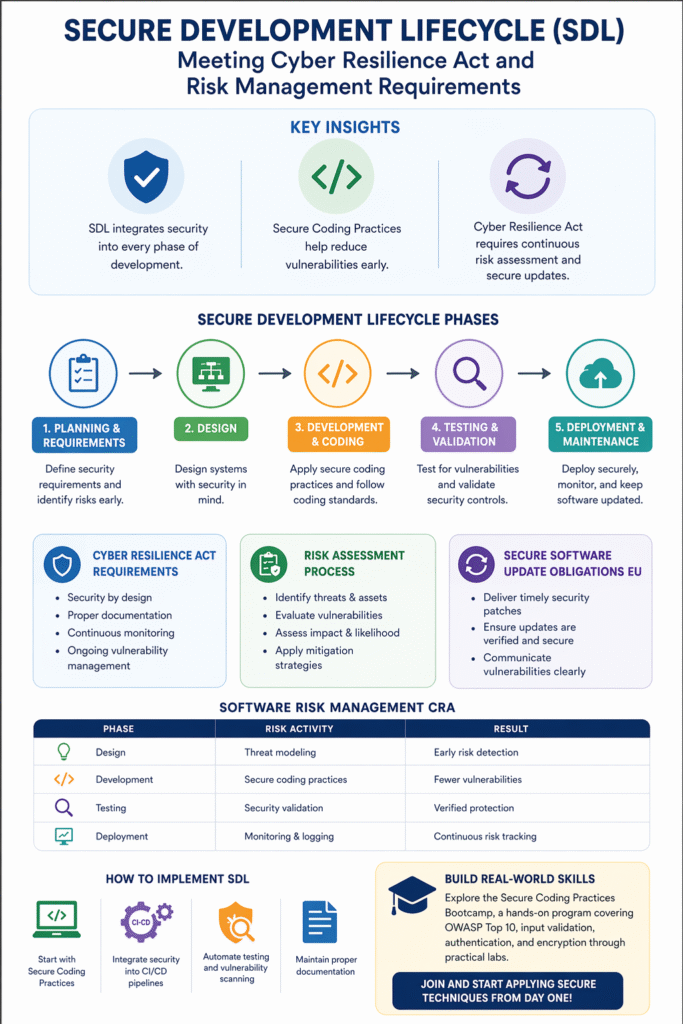
The risk assessment requirements cyber resilience act require continuous evaluation of software risks.
A typical process includes:
- Identifying threats and assets
- Evaluating vulnerabilities
- Assessing impact and likelihood
- Applying mitigation strategies
We’ve found that risk assessment works best when treated as an ongoing activity, not a one-time task. This approach helps teams stay aligned with both security and compliance goals.
Software Risk Management CRA
Software risk management cra ensures that risks are handled systematically across the lifecycle.
| Phase | Risk Activity | Result |
| Design | Threat modeling | Early risk detection |
| Development | Secure coding practices | Fewer vulnerabilities |
| Testing | Security validation | Verified protection |
| Deployment | Monitoring & logging | Continuous risk tracking |
This structured approach allows teams to prevent issues instead of reacting to them later.
Secure Software Update Obligations EU
The secure software update obligations eu ensure software remains secure after release.
Key responsibilities include:
- Delivering timely security patches
- Ensing updates are verified and secure
- Communicating vulnerabilities clearly
From our experience, teams that automate updates and use secure delivery methods reduce risks significantly while maintaining user trust.
How to Implement Secure Development Lifecycle
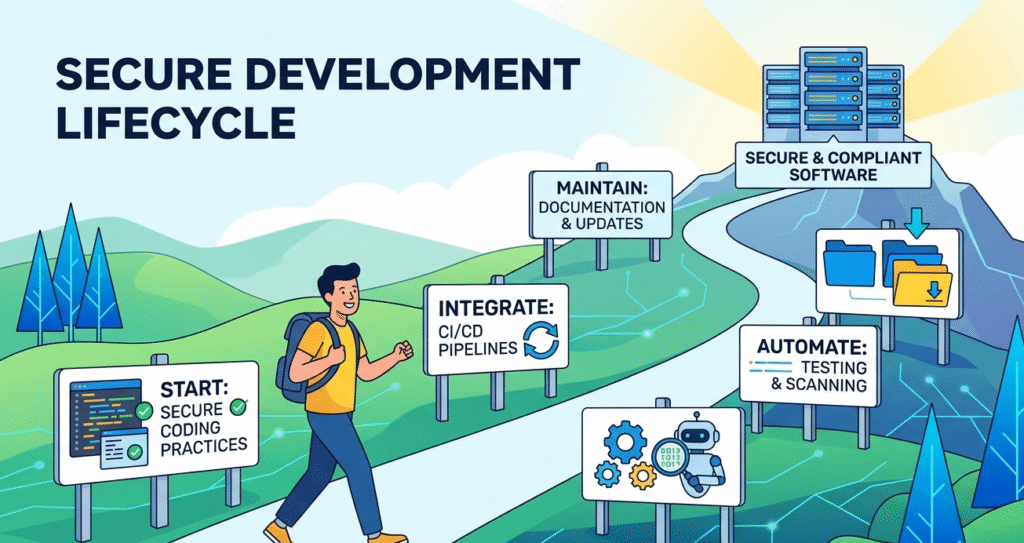
Implementing SDL can be done gradually without overwhelming the team.
We recommend:
- Start with Secure Coding Practices
- Integrate security into CI/CD pipelines
- Automate testing and vulnerability scanning
- Maintain proper documentation
Teams that take a step-by-step approach usually achieve better long-term results.
FAQ
How does secure development lifecycle support cyber resilience act compliance?
Secure development lifecycle helps align development processes with cyber resilience act secure development lifecycle requirements. It ensures security is considered from planning to maintenance.
By integrating risk assessment, secure coding, and continuous monitoring, teams can meet compliance expectations more easily. This approach also reduces vulnerabilities early, making it easier to handle audits and maintain long-term software security.
What are the key risk assessment requirements in the cyber resilience act?
The risk assessment requirements cyber resilience act focus on identifying, evaluating, and managing risks continuously. Teams need to analyze threats, assess vulnerabilities, and estimate impact regularly.
It is not a one-time task. Instead, risk assessment evolves as the software changes. This ongoing process helps organizations stay compliant while improving overall security and reducing unexpected issues.
Why are secure coding requirements important in software development?
The secure coding requirements cyber resilience act aim to reduce vulnerabilities during development. Using secure coding practices, developers can prevent common issues like injection attacks or weak authentication.
This makes software more stable and secure from the start. It also reduces the need for major fixes later, saving time and effort while supporting compliance with security regulations.
How does software risk management cra improve security outcomes?
Software risk management cra helps teams identify and handle risks throughout the development lifecycle. Instead of reacting to problems after release, teams can address them early. This includes threat modeling, testing, and monitoring.
From a practical perspective, this structured approach improves decision-making, reduces security gaps, and ensures that risks are properly documented and controlled.
Final Thoughts on Secure Development Lifecycle
Secure Development Lifecycle helps teams build secure, compliant software without unnecessary complexity. From our experience, starting with Secure Coding Practices makes adoption smoother and more effective.
To build real-world skills, explore the Secure Coding Practices Bootcamp, a hands-on program covering OWASP Top 10, input validation, authentication, and encryption through practical labs. Join and start applying secure techniques from day one
References
- https://www.mdpi.com/2079-9292/8/11/1218
- https://en.wikipedia.org/wiki/Cyber_Resilience_Act
Related Articles
- https://securecodingpractices.com/secure-coding-requirements-cyber-resilience-act/
- https://securecodingpractices.com/cyber-resilience-act-secure-development-lifecycle/
- https://securecodingpractices.com/software-risk-management-cra/
- https://securecodingpractices.com/risk-assessment-requirements-cyber-resilience-act/
- https://securecodingpractices.com/secure-software-update-obligations-eu/