Compliance and enforcement under the Cyber Resilience Act define how organizations must design, build, and maintain secure software products while proving adherence through audits and regulatory oversight. For developers, this means security is no longer optional, it is embedded into every stage of development.
From our experience, teams that integrate compliance early, especially through Secure Coding Practices, avoid last-minute audit stress and reduce enforcement risks significantly. In this guide, we break down the practical side of compliance and enforcement in a structured way. Keep reading.
Compliance and Enforcement in the Cyber Resilience Act
Compliance and enforcement are not separate activities, they are tightly connected throughout the software lifecycle.
- Developers play a direct role in cyber resilience act compliance through secure development practices
- A clear compliance roadmap reduces audit pressure and improves readiness
- Enforcement includes fines, penalties, and market restrictions for non-compliance
Cyber Resilience Act Compliance for Developers
Cyber resilience act compliance for developers focuses on building security directly into software design and implementation. Developers are expected to actively support compliance rather than treat it as a separate governance task.
From our experience, the most effective starting point is Secure Coding Practices, because they reduce vulnerabilities before they reach production.
Key responsibilities include:
- Writing secure and maintainable code
- Managing vulnerabilities early in the development lifecycle
- Supporting documentation with technical accuracy
- Ensuring software update mechanisms are secure
“Security by design and by default is a fundamental principle of modern software development.” – Wikipedia
This principle aligns closely with CRA expectations, where prevention is more important than reaction.
Cyber Resilience Act Compliance Roadmap
Credits: Energy and Mining SA
A cyber resilience act compliance roadmap helps organizations structure their journey toward full regulatory readiness.
A typical roadmap includes:
Planning Phase
- Identify applicable CRA requirements
- Define security and compliance ownership
- Establish development and documentation standards
Implementation Phase
- Integrate Secure Coding Practices into development workflows
- Build threat modeling and risk assessment processes
- Develop technical documentation alongside code
Validation Phase
- Conduct internal compliance checks
- Perform vulnerability assessments
- Prepare evidence for audits
Maintenance Phase
- Continuous monitoring and patch management
- Regular documentation updates
- Ongoing compliance reviews
From our experience, organizations that follow a roadmap avoid reactive compliance efforts and reduce operational disruption.
Cyber Resilience Act Audit Preparation
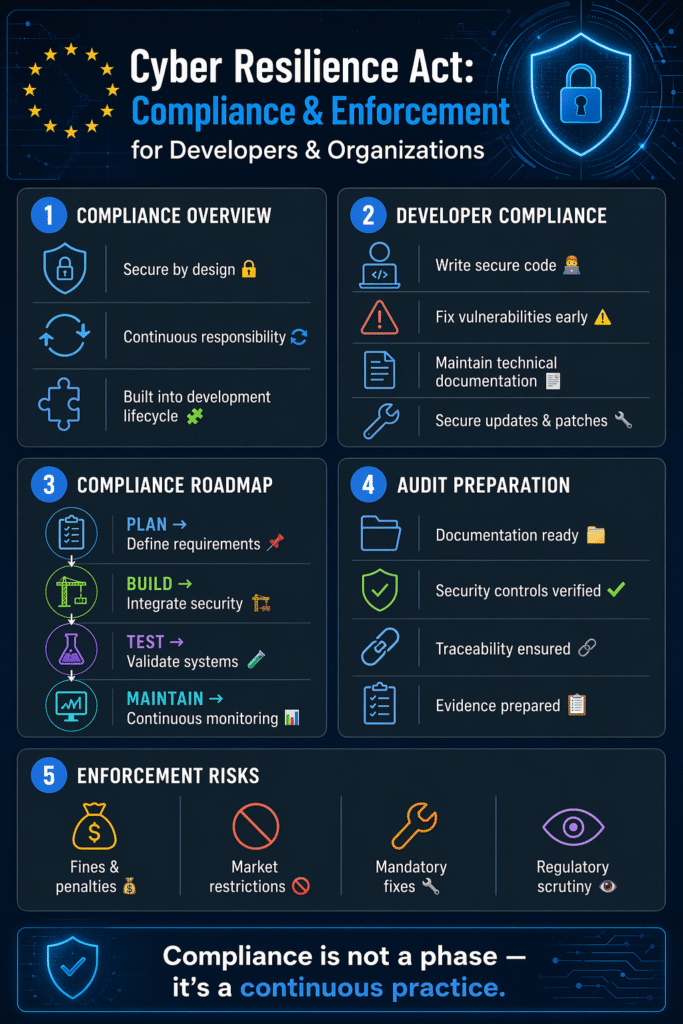
Cyber resilience act audit preparation is a critical step where organizations demonstrate that their products meet regulatory requirements.
Audit preparation typically involves:
- Reviewing technical documentation completeness
- Verifying security controls and implementations
- Ensuring traceability between code, risks, and mitigations
- Preparing evidence for incident response and update processes
“An audit is a systematic and independent examination of records, statements, and processes.” – Wikipedia
We’ve seen that audit success depends less on last-minute preparation and more on continuous compliance practices embedded throughout development.
Fines and Penalties under the Cyber Resilience Act Software
Fines and penalties under the Cyber Resilience Act are designed to enforce accountability and ensure organizations take cybersecurity seriously.
Non-compliance may result in:
- Financial penalties based on severity of violation
- Restrictions on product market access
- Mandatory corrective actions or recalls
- Increased regulatory scrutiny
From a practical standpoint, enforcement is not just punitive, it is intended to drive better security behavior across the software industry.
The key takeaway is simple: prevention is far less costly than enforcement actions.
Cyber Resilience Act Certification Process
The cyber resilience act certification process ensures that products meet defined cybersecurity standards before entering the market.
Typical steps include:
Self or Third-Party Assessment
Depending on product risk classification, organizations may perform internal checks or involve external assessors.
Technical Documentation Review
Authorities evaluate whether documentation accurately reflects product security.
Security Verification
Testing and validation of implemented security controls.
Final Certification Decision
Approval or rejection based on compliance evidence.
From our experience, certification is much smoother when Secure Coding Practices and documentation are aligned from the beginning of development.
Common Challenges in Compliance and Enforcement
Organizations often face similar challenges:
- Compliance treated too late in development
- Poor alignment between documentation and implementation
- Lack of clear ownership between teams
- Reactive rather than continuous compliance processes
These challenges are usually process-related rather than technical.
FAQ
What is the main goal of Cyber Resilience Act compliance?
The main goal is to ensure that software and digital products are secure by design, reducing vulnerabilities before products reach users and maintaining security throughout the product lifecycle.
Who is responsible for Cyber Resilience Act compliance?
Responsibility is shared, but developers, product teams, and organizations all play a role. Developers focus on secure implementation, while organizations ensure governance, documentation, and audit readiness.
When should compliance activities start in development?
Compliance should start at the earliest stage of development. Integrating Secure Coding Practices and documentation from the beginning significantly reduces risks during audits and certification.
What happens if an organization fails to comply with the Cyber Resilience Act?
Non-compliance can lead to financial penalties, mandatory corrective actions, restricted market access, and increased regulatory scrutiny depending on the severity of the violation.
Strengthening Compliance and Enforcement in Cybersecurity
Compliance and enforcement under the Cyber Resilience Act require more than just meeting requirements, they demand continuous accountability across development, documentation, and operational processes. From our experience, starting with Secure Coding Practices creates a strong foundation that simplifies audits, certification, and enforcement readiness.
When compliance is embedded into everyday workflows, organizations reduce risk and improve resilience naturally. To stay ahead, build security into your code, maintain continuous readiness, and treat compliance as an ongoing practice, not a final step.
References
- https://en.wikipedia.org/wiki/Security_by_design
- https://en.wikipedia.org/wiki/Audit
Related Articles
- https://securecodingpractices.com/cyber-resilience-act-compliance-for-developers/
- https://securecodingpractices.com/cyber-resilience-act-compliance-roadmap/
- https://securecodingpractices.com/cyber-resilience-act-audit-preparation/
- https://securecodingpractices.com/fines-penalties-cyber-resilience-act-software/
- https://securecodingpractices.com/cyber-resilience-act-certification-process/
