What causes SQL injection attacks is important for businesses that manage websites and applications. SQL injection happens when attackers exploit unsafe database queries using user input. Many vulnerabilities appear because of weak validation and insecure coding practices.
From our experience, understanding these causes helps organizations improve security and reduce database risks. Keep reading to learn the common causes of SQL injection attacks and how businesses strengthen protection against them.
Key SQL Injection Insights
Understanding what causes SQL injection attacks helps organizations strengthen database security earlier.
- Unsafe database queries create major SQL injection risks.
- Weak input validation increases attack opportunities.
- Secure coding reduces long-term application exposure.
Understanding How SQL Injection Works
SQL injection attacks happen when applications trust user input without securing database queries properly. Attackers manipulate inputs to alter query behavior and access unauthorized information.
“SQL injection attacks are possible because of the lack of proper input validation and security measures in web applications” – Abdullayev & Chauhan, 2023
Common attack goals include:
- Stealing sensitive data
- Bypassing authentication
- Modifying database records
- Escalating privileges
- Disrupting services
We often see SQL injection vulnerabilities appear in applications where developers directly combine user input with SQL commands. Applications connected to customer databases and login systems are especially common targets.
Unsafe Dynamic SQL Queries
Credits: Hacksplaining
One major factor behind these vulnerabilities is the use of dynamic SQL. Reviewing sql injection attack examples on websites shows how dynamic queries built through string concatenation are easily exploited.
Common examples include:
- Login forms
- Search bars
- URL parameters
- API requests
- Customer portals
| Unsafe Practice | Security Risk |
| String Concatenation | Query manipulation |
| Raw SQL Input | Database compromise |
| Unfiltered Parameters | Unauthorized access |
| Dynamic Queries | Sensitive data exposure |
Organizations usually reduce risks significantly by using parameterized queries instead of dynamic query construction.
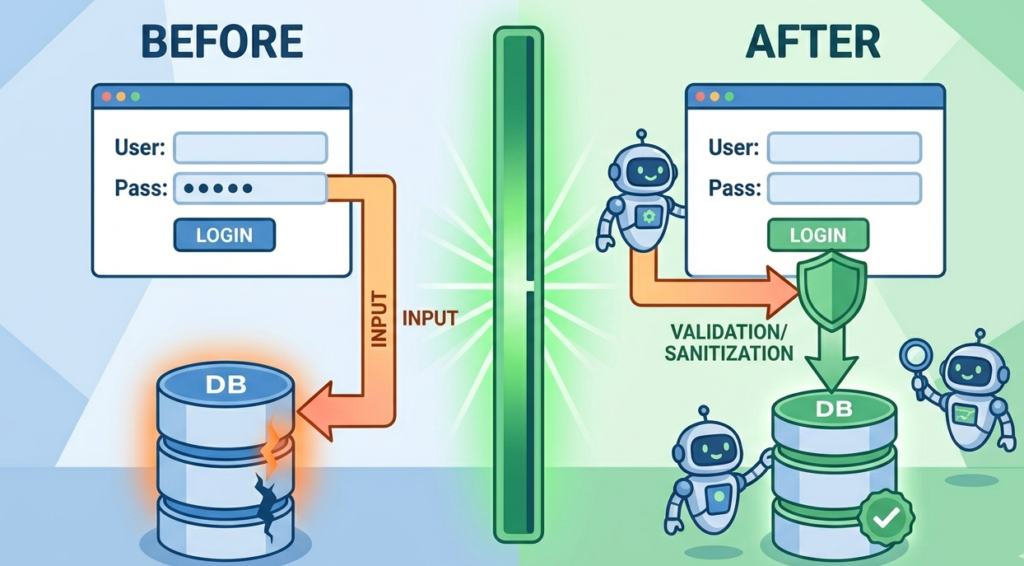
Weak Input Validation
Weak validation allows malicious input to pass into backend systems without proper filtering or restrictions.
“the most common and serious mistake developers make is using inputs in SQL statements without any checks” – Shar & Tan, 2013
Common validation weaknesses include:
- Missing character filtering
- No input length restrictions
- Trusting frontend validation only
- Poor sanitization logic
- Unsafe special character handling
From our experience, businesses often assume frontend validation alone is enough protection, but attackers can bypass browser-level controls easily. Strong server-side validation remains critical for reducing SQL injection exposure.
Poor Authentication and Access Controls
Weak authentication systems frequently increase SQL injection risks because attackers target login workflows aggressively.
Common weaknesses include:
- Insecure login forms
- Excessive database permissions
- Weak session handling
- Missing MFA protections
Applications that allow direct database interaction with high-level privileges usually face greater security exposure during SQL injection attacks. Limiting database access permissions helps reduce damage even if vulnerabilities exist.
Outdated Development Practices

Many SQL injection vulnerabilities remain active because organizations still rely on outdated coding methods or unsupported frameworks.
Common outdated practices include:
- Legacy PHP applications
- Deprecated libraries
- Hardcoded SQL queries
- Weak security testing processes
We often see older applications contain insecure database handling that was never reviewed after deployment. Continuous modernization and secure coding reviews usually improve resilience significantly.
Lack of Parameterized Queries
Standardizing prepared statements is the most effective method for preventing SQL injection and ensuring consistent application security.
Benefits of parameterized queries include:
- Safe query execution
- Separated user input handling
- Reduced injection opportunities
- Improved security consistency
Organizations that standardize prepared statements usually reduce SQL injection exposure substantially.
Excessive Database Permissions
Databases with excessive permissions create larger attack surfaces during SQL injection incidents.
Common permission problems include:
- Administrative database access
- Full table modification rights
- Unrestricted query execution
- Shared privileged accounts
From our perspective, limiting database privileges is one of the most overlooked security improvements. Least-privilege access controls help minimize operational damage during exploitation attempts.
Insecure Error Handling
Detailed database errors can accidentally help attackers understand backend systems during SQL injection attempts.
Common risks include:
- Exposed SQL syntax errors
- Database structure disclosure
- Debug information leaks
- Stack trace exposure
Attackers frequently use exposed error messages to refine injection payloads and identify vulnerable query structures. Organizations usually improve security by restricting verbose database error visibility in production environments.
Lack of Security Testing
Applications without regular security testing often contain hidden SQL injection vulnerabilities for long periods.
Important testing methods include:
- Vulnerability scanning
- Penetration testing
- Secure code reviews
- Input fuzzing
- Manual query analysis
We often recommend combining automated testing with manual validation for stronger coverage. Continuous testing helps organizations detect vulnerabilities earlier across development lifecycles.
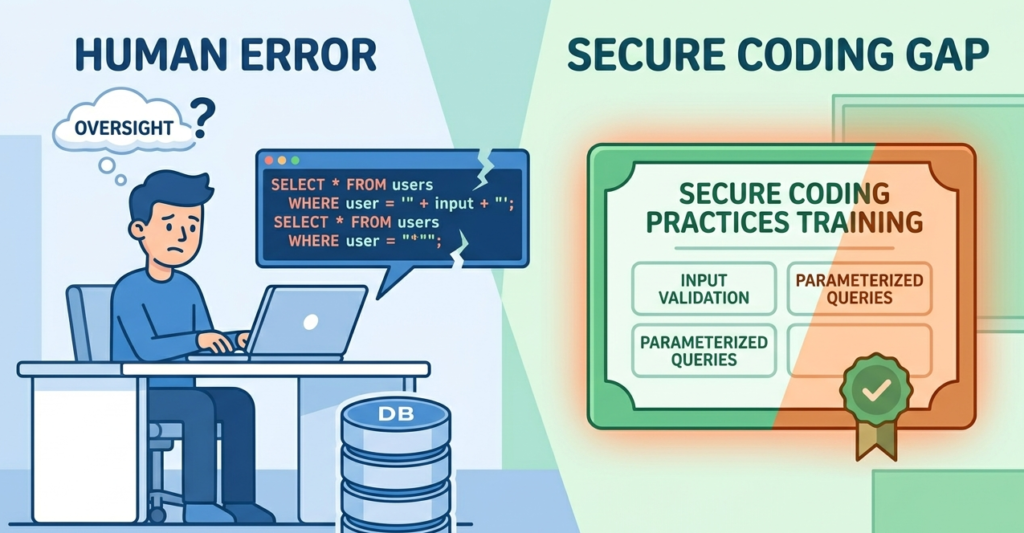
Human Error and Secure Coding Gaps
Human mistakes remain a leading factor, but understanding SQL injection and its underlying causes helps developers avoid common coding gaps.
Common development mistakes include:
- Unsafe query construction
- Poor validation logic
- Insecure framework usage
- Missing security reviews
- Weak development standards
Organizations that prioritize secure coding education usually improve long-term application resilience faster. Consistent developer awareness reduces repeated security mistakes across projects.
FAQ
What causes SQL injection attacks most often?
Unsafe SQL query construction and weak input validation are among the most common causes.
Why are parameterized queries important?
Parameterized queries separate user input from SQL commands, reducing injection opportunities significantly.
Can old applications increase SQL injection risks?
Yes. Legacy applications often contain outdated coding practices and unsupported libraries that increase exposure.
How do organizations reduce SQL injection risks?
Organizations improve protection through secure coding, parameterized queries, testing, validation, and proper access controls.
Stronger Security Starts With Understanding the Causes
Understanding SQL injection causes helps organizations strengthen application security before vulnerabilities become serious incidents. Prioritizing secure coding, input validation, and parameterized queries significantly reduces operational risks. Proactive development security creates stronger resilience than reactive remediation.
To master these skills, join the Secure Coding Practices Bootcamp. This 2-day, hands-on course covers the OWASP Top 10, encryption, and safe dependency use through practical labs. Equipping developers to ship safer code from day one. Join the Bootcamp.
References
- https://doi.org/10.58496/mjcs/2023/006
- https://doi.org/10.1109/mc.2012.283
