Understanding SQL Injection SQLi is important for businesses that manage websites, applications, and databases. SQL injection attacks happen when attackers manipulate insecure database queries through unsafe user input. From our experience, many organizations still face SQLi risks because of weak validation and outdated coding practices.
Strong prevention methods like parameterized queries, secure coding, and continuous testing help reduce exposure significantly. Keep reading to explore how Understanding SQL Injection SQLi improves application security and database protection.
Key SQL Injection Insights
Understanding SQL Injection SQLi helps organizations improve database security before attackers exploit vulnerabilities.
- SQL injection attacks target insecure database queries.
- Parameterized queries greatly reduce SQLi risks.
- Continuous testing improves long-term application security.
What Causes SQL Injection Attacks
Understanding SQL Injection SQLi starts with understanding how insecure user input interacts with database queries. SQL injection attacks happen when applications trust input without proper validation or parameterization.
“Application-level vulnerabilities, which are believed to account for 70% to 90% of overall flaws, are now the main focus of attackers and researchers” – Sivakorn et al., 2023.
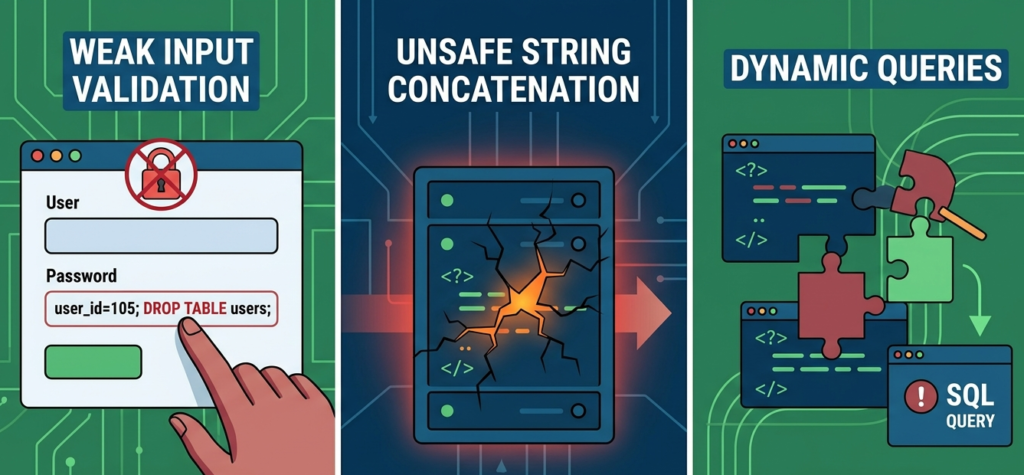
Common causes include:
- Dynamic SQL queries
- Weak input validation
- Unsafe string concatenation
- Excessive database permissions
- Outdated development practices
We often see SQL injection vulnerabilities appear inside older applications where secure coding standards were not consistently implemented.
Applications handling forms, authentication pages, and URL parameters are especially common targets.
Preventing SQL Injection PHP Java
Preventing SQL injection in PHP and Java requires secure database interaction methods and stronger development practices.
“While ORM libraries can significantly reduce the surface area for SQL injection, they do not provide a silver bullet; developers must still be cautious of ‘leaky abstractions’ where raw SQL is used for complex queries” – ResearchGate
Common prevention approaches include:
- Prepared statements
- Parameterized queries
- Input validation
- ORM frameworks
- Database access restrictions
In PHP, developers commonly use PDO prepared statements. In Java, PreparedStatement APIs help separate SQL logic from user input securely. From our experience, organizations improve resilience faster when secure coding becomes part of daily development workflows.
SQL Injection Attack Examples Websites
Understanding SQL Injection SQLi also involves recognizing how attackers target vulnerable websites and applications.
Common attack targets include:
- Login portals
- Search bars
- Admin dashboards
- Customer portals
- API endpoints
Many organizations only detect vulnerabilities after suspicious database activity or breach investigations begin.
Blind SQL Injection Techniques Tutorial
Credits: Network Chuck
Blind SQL injection happens when applications hide database errors but still respond differently to manipulated queries.
Common blind SQLi techniques include:
- Boolean-based injections
- Time-based injections
- Conditional query testing
- Response inference analysis
Attackers usually analyze:
- Response delays
- Content changes
- HTTP status differences
- Application behavior patterns
We often see blind SQL injection remain undetected longer because attacks may resemble normal application traffic.
Testing for SQL Injection Vulnerabilities
Testing helps organizations identify SQL injection weaknesses before attackers exploit them.
Common testing methods include:
- Vulnerability scanning
- Manual query testing
- Input fuzzing
- Penetration testing
- Secure code reviews
Organizations frequently improve testing accuracy by combining automated tools with manual validation techniques. Continuous testing also strengthens development security visibility across application lifecycles.
SQL Injection Mitigation Strategies Code

SQL injection mitigation strategies focus on reducing attack opportunities through secure coding and database protections.
Important mitigation approaches include:
- Parameterized queries
- Strict validation
- Error handling restrictions
- Database segmentation
- Principle of least privilege
We often recommend minimizing direct database exposure whenever possible. Applications should also limit unnecessary database permissions to reduce attack impact during exploitation attempts.
Parameterized Queries Prevent SQL Injection
Parameterized queries are one of the strongest defenses in Understanding SQL Injection SQLi. These queries separate SQL commands from user input safely.
Benefits include:
- Safer query execution
- Reduced injection exposure
- Improved security consistency
- Stronger database integrity
| Query Type | Risk Level |
| Dynamic Queries | High risk |
| Concatenated Input | Very high risk |
| Prepared Statements | Low risk |
| Parameterized Queries | Strong protection |
From our perspective, parameterized queries should become a standard practice across all modern applications.
ORM SQL Injection Protection Guide
ORM frameworks help developers interact with databases more securely by reducing direct SQL query construction.
Common ORM protections include:
- Automatic parameter binding
- Query abstraction
- Safer database interaction
- Reduced raw SQL exposure
However, developers still need secure coding awareness because unsafe custom queries may still introduce vulnerabilities. We often see organizations assume ORM tools automatically eliminate all SQL injection risks, which is not always true.
Escaping User Input SQL Correctly
Escaping user input helps applications process special characters safely inside database queries. However, escaping alone should not replace parameterized queries.
Important escaping considerations include:
- Database-specific syntax
- Character encoding consistency
- Context-aware query handling
- Special symbol management
We frequently recommend using escaping only as an additional protection layer rather than the primary defense method. Prepared statements generally provide stronger long-term protection.
Impact Assessment SQL Injection
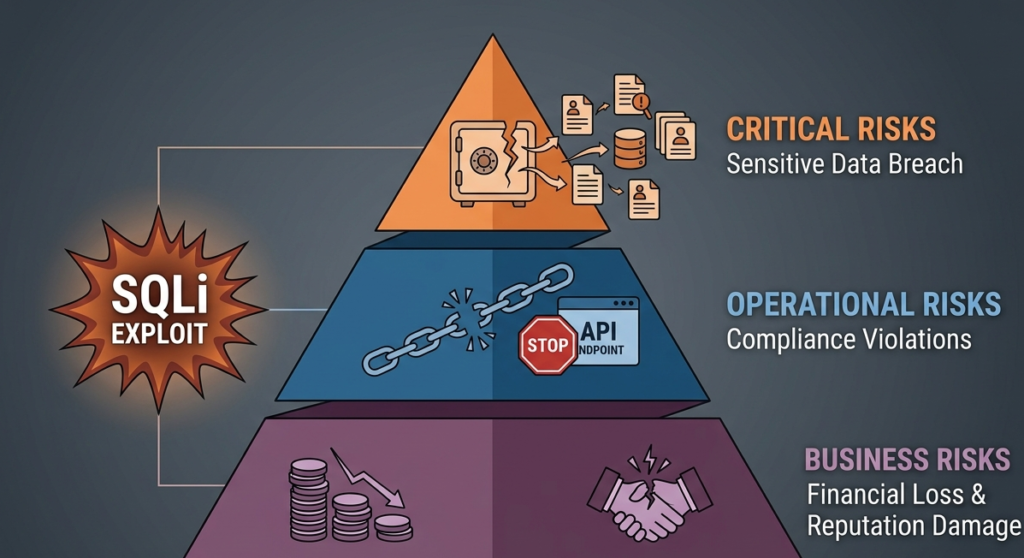
Understanding SQL Injection SQLi also means understanding its operational and business impact.
Common impacts include:
- Sensitive data breaches
- Credential theft
- Compliance violations
- Financial losses
- Reputation damage
Organizations handling customer, healthcare, or financial information often face higher risks during SQL injection incidents. Strong impact assessments help businesses prioritize secure development and database protection efforts more effectively.
FAQ
What is Understanding SQL Injection SQLi?
It refers to learning how SQL injection attacks work, how attackers exploit databases, and how organizations can prevent these vulnerabilities.
Why are parameterized queries important?
Parameterized queries separate user input from SQL commands, reducing SQL injection exposure significantly.
Can ORM frameworks prevent SQL injection completely?
ORM frameworks improve protection, but insecure custom queries may still create vulnerabilities.
How do organizations test for SQL injection?
Organizations use penetration testing, code reviews, vulnerability scanners, and manual query analysis.
Understanding SQL Injection SQLi Builds Stronger Application Security
Understanding SQL injection is vital for building resilient applications. By prioritizing parameterized queries and proactive input handling, organizations can neutralize threats before they escalate. Secure coding practices not only reduce operational risk but also foster long-term customer trust.
Empower your development team to write safer code with the Secure Coding Practices Bootcamp. This hands-on, two-day training focuses on practical skills like input validation and encryption without the jargon. Join the Bootcamp.
References
- https://map.researchcommons.org/cgi/viewcontent.cgi?article=1018&context=mjcs
- https://www.researchgate.net/publication/269245585_Simulation_of_High-Level_Web_Applications_for_SQL_Injection_Detection
