
Secure coding regulatory expectations EU are changing how software is designed, built, and maintained. Developers are now expected to think about security from the very beginning, not as a final step. From our experience, teams that understand these expectations early can avoid compliance issues and reduce long-term risks.
By aligning development practices with EU regulations, organizations can build more secure and reliable products while staying competitive in the market. Keep reading to learn how to stay compliant and strengthen your secure development practices.
Secure Coding in the EU: Key Insights to Remember
Understanding secure coding regulatory expectations in the EU can feel overwhelming at first. However, the core ideas are consistent across all regulations and easy to apply when simplified.
- Security must be integrated from the start, not added later
- Continuous monitoring and updates are essential for compliance
- Developer awareness and training are key to long-term success
Why Secure Coding Matters in the EU
Secure coding is no longer optional in Europe, it’s expected. Regulations now require teams to integrate security from the start, not patch it later. From our experience at Secure Coding Practices, teams that embed security early avoid delays, reduce vulnerabilities, and pass audits more easily.
“Security must be considered throughout the entire lifecycle of ICT products, services and processes.” – ENISA
Organizations across the EU are expected to:
- Prevent vulnerabilities during development
- Maintain security throughout the product lifecycle
- Respond quickly to risks and incidents
This shift reflects a broader mindset: software is considered a product, and like any product, it must be safe by design.
Key EU Regulations Driving Secure Coding
Credits: IT Encyclopedia
Several EU regulations define what secure coding should look like in practice. Navigating the cyber resilience act vs nis2 and other mandates adds a layer of responsibility for developers and organizations.
- Cyber Resilience Act (CRA)
Focuses on secure-by-design and lifecycle security for digital products - NIS2 Directive
Requires strong cybersecurity risk management and reporting - General Product Safety Regulation (GPSR)
Expands safety expectations to digital products - GDPR (security aspect)
Requires protection of personal data through secure systems
Together, these frameworks push teams to treat secure coding as a compliance requirement, not just a technical best practice.
Core Secure Coding Expectations
Across these regulations, common expectations appear consistently. Adopting secure software development eu law requires organizations to integrate security into the lifecycle to reduce vulnerabilities.
“Organizations should integrate security into the software development life cycle to reduce vulnerabilities.” – NIST
From what we’ve seen working with development teams, the most critical requirements include:
- Secure-by-design architecture
- Regular vulnerability testing (SAST/DAST)
- Dependency and supply chain security
- Secure authentication and access control
- Timely patching and updates
- Logging, monitoring, and incident response
Teams that follow these principles naturally align with EU expectations. It’s less about memorizing rules and more about building security into everyday workflows.
Practical Implementation in Development Teams
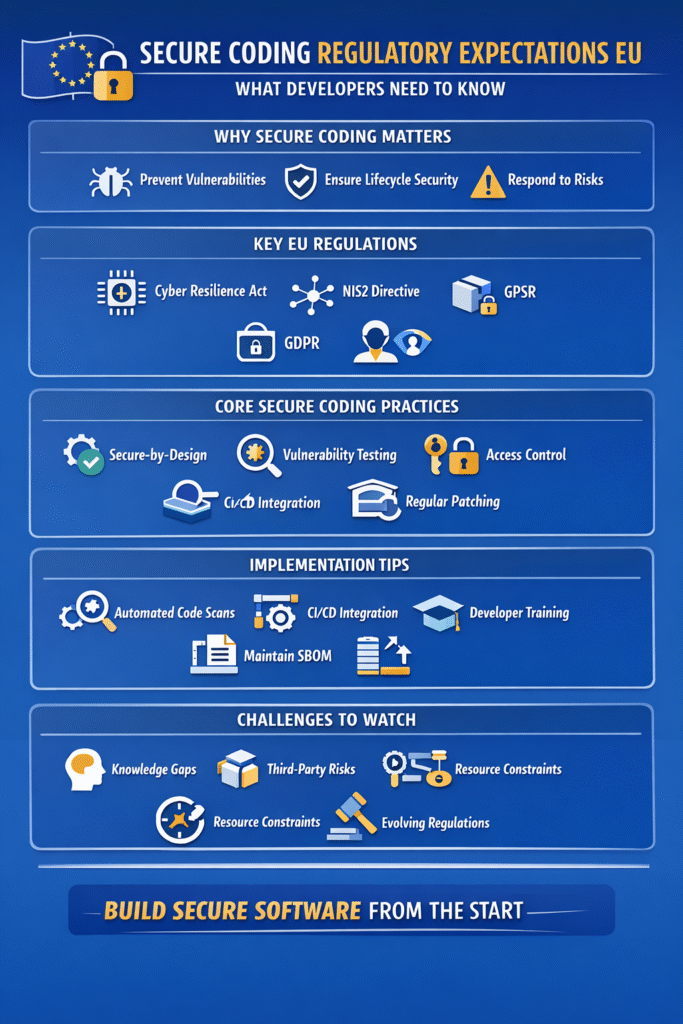
Meeting regulatory expectations doesn’t require complex transformations, it requires consistency.
Here’s how many teams successfully apply secure coding in practice:
- Integrate security checks into CI/CD pipelines
- Use automated tools for code scanning
- Train developers on secure coding standards
- Maintain a software bill of materials (SBOM)
- Conduct regular security reviews
We’ve learned that small, consistent actions outperform large, one-time efforts. Teams that adopt this mindset often find compliance becomes a byproduct of good engineering.
Comparison of Key Regulations
| Regulation | Focus Area | Key Requirement | Who It Affects |
| Cyber Resilience Act | Product security | Secure-by-design, updates | Software vendors |
| NIS2 Directive | Cyber risk management | Incident reporting, risk controls | Critical sectors |
| GPSR | Product safety | Safe consumer products | Manufacturers |
| GDPR | Data protection | Secure data handling | All organizations |
This table shows how different rules overlap but ultimately reinforce the same goal: secure, reliable software.
Challenges Teams Commonly Face
Even with clear expectations, implementation can be difficult.
Common challenges include:
- Lack of security knowledge regarding the legal and regulatory context, limited resources, or time constraints during the implementation phase.
- Limited resources or time constraints
- Managing third-party dependencies
- Keeping up with evolving regulations
From our experience, the biggest gap is not tools, it’s awareness. Once teams understand why secure coding matters, adoption becomes much easier.
How We Approach Secure Coding
At Secure Coding Practices, we approach compliance as part of development, not a separate task.
We focus on:
- Embedding security into developer workflows
- Providing practical, real-world guidance
- Supporting teams through training and tools
Instead of treating regulations as obstacles, we see them as a framework for building better software. This perspective helps teams stay compliant while improving overall product quality.
FAQ
What are secure coding regulatory expectations EU developers must follow today?
Secure coding regulatory expectations EU developers must follow focus on building security into every stage of development. This includes secure-by-design principles, regular testing, and fast vulnerability fixes.
Teams are also expected to manage risks in dependencies and maintain documentation. These expectations are shaped by EU cybersecurity regulations and aim to ensure software remains safe, reliable, and compliant over time.
How do secure coding requirements EU impact daily development workflows?
Secure coding requirements EU impact daily workflows by adding security checks into regular tasks. Developers must include code reviews, automated scanning, and secure configuration practices.
It also means thinking about threats earlier in the process. While it may seem like extra work at first, many teams find it improves code quality and reduces future issues significantly.
Why is secure software development EU compliance important for small teams?
Secure software development EU compliance is important for small teams because regulations apply regardless of company size. Even smaller teams must ensure their software is safe and meets legal standards.
Ignoring compliance can lead to risks, penalties, or loss of trust. Starting early helps small teams manage security better without overwhelming resources or disrupting development speed.
What challenges exist in meeting EU secure coding standards?
Meeting EU secure coding standards can be challenging due to limited knowledge, time constraints, and evolving regulations. Many teams struggle with integrating security into fast-paced development cycles.
Managing third-party components also adds complexity. However, with consistent practices and gradual improvements, teams can overcome these challenges and align with secure coding regulatory expectations EU more effectively.
Final Thoughts
Secure coding regulatory expectations in the EU require a proactive and practical approach to security. Teams that integrate secure-by-design principles and continuous practices are better prepared for compliance and risk reduction. From our experience, hands-on learning makes the biggest difference.
The Secure Coding Practices Bootcamp helps developers build real-world skills through practical sessions and guided labs.
References
- https://www.enisa.europa.eu/publications
- https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-218.pdf

