Blind SQL injection techniques tutorials happens when attackers test database behavior without seeing direct error messages. Instead of visible errors, they observe timing changes or page differences to confirm whether a system is vulnerable.
Many organizations think hiding SQL errors is enough protection. In practice, attackers often use indirect clues to extract sensitive information quietly. Keep reading to understand common blind SQL injection methods and how secure coding reduces these risks.
Key Blind SQL Injection Insights
Blind attacks often stay unnoticed longer than standard SQL injection because they mimic normal traffic.
- Blind SQL injection works without visible database errors
- Attackers use behavior-based testing
- Timing delays reveal hidden database responses
What Is Blind SQL Injection?
Blind SQL injection happens when an application processes unsafe SQL queries but does not display database errors.
“insecure coding practices, lack of proper input validation, and insufficient use of parameterized queries” – Sikorskyi & Harasymchuk, 2026
Attackers collect information by observing:
- Page content changes
- Response delays
- Status code differences
- Login success or failure
The attacker sends small test conditions to reveal database behavior over time.
Boolean-Based Blind SQL Injection
Boolean-based attacks compare true and false responses.
Examples:
- ‘ AND 1=1 —
- ‘ AND 1=2 —
If the webpage reacts differently, the attacker confirms vulnerability.
Common signs:
- Missing page content
- Different messages
- Redirect behavior changes
This method is common in login systems and product search pages.
Time-Based Blind SQL Injection
Credits: Meta4sec
Time-based attacks force the database to delay responses.
Example payloads may trigger sleep functions when conditions are true.
Attackers watch for:
- Delayed page loading
- Consistent response pauses
- Server timing differences
This works even when applications show identical page content.
Time-based attacks often target APIs and backend filters.
Common Attack Targets
Blind SQL injection often affects database-driven features.
Frequent targets include:
- Login forms
- Search bars
- URL parameters
- Customer portals
- API endpoints
Older applications often carry higher risk because they rely on unsafe query construction.
Business Risks
Blind SQL injection can create serious damage.
Potential impacts:
- Customer data leaks
- Compliance penalties
- Downtime
- Reputation loss
- Financial costs
Even small vulnerabilities can become large breaches if ignored.
Why Hidden Errors Are Not Enough
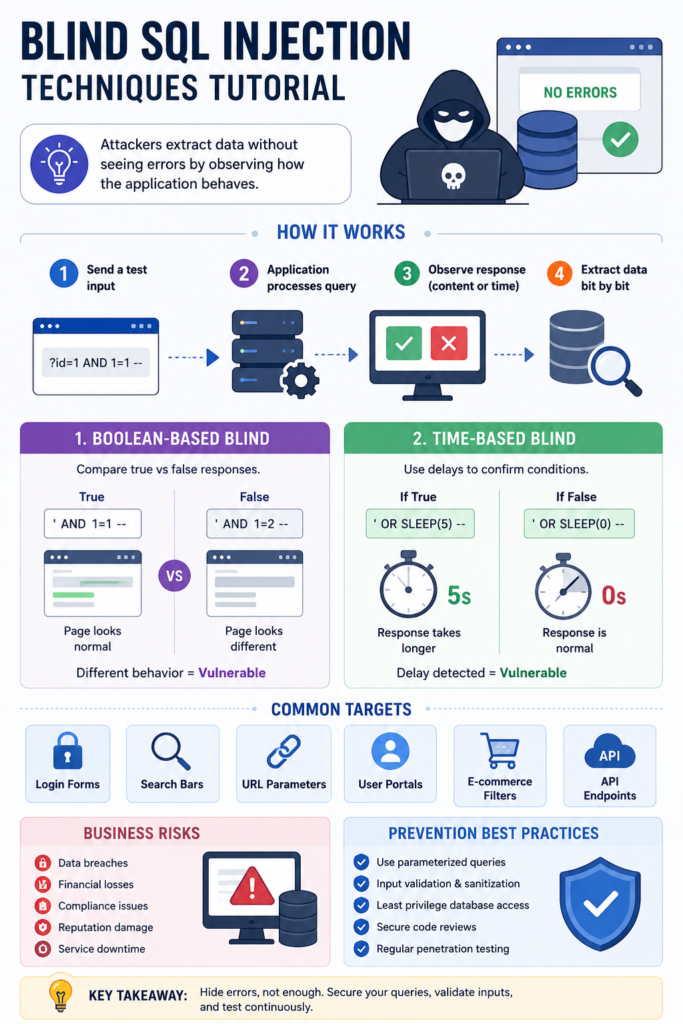
Some developers disable SQL error messages for safety.
“the main, basic and essential prevention of SQL injection is by writing secured source code” – Dorai et al., 2010
This helps, but does not stop blind SQL injection.
Attackers still detect vulnerabilities using:
- Timing analysis
- Page comparisons
- Response patterns
Secure query handling and a deep understanding of sql injection mechanisms matter more than simply hiding database messages.
Preventing Blind SQL Injection
Organizations reduce risks by prioritizing preventing sql injection through stronger development practices and robust input handling.
Key protections:
- Parameterized queries
- Prepared statements
- Input validation
- Secure code reviews
- Regular penetration testing
Businesses that secure applications early usually lower remediation costs.
Secure Coding Best Practices

Strong defenses include:
- Avoid dynamic SQL queries
- Restrict database permissions
- Update frameworks regularly
- Monitor unusual request patterns
- Test APIs continuously
Studying real-world sql injection attack examples helps teams build proactive security, creating stronger resilience than reactive fixes.
FAQ
What makes blind SQL injection different?
It works through indirect application behavior instead of visible database errors.
Can APIs be vulnerable?
Yes. Unsafe backend database queries can expose APIs.
Is blind SQL injection hard to detect?
Yes. Requests often look like normal traffic.
What is the best defense?
Parameterized queries combined with secure testing.
Stronger Security Starts With Better Query Protection
Blind SQL injection proves attackers can silently exploit hidden database gaps. To defend, organizations must prioritize robust input validation and secure coding. Strengthening these defenses builds faster resilience and secures critical data against evolving threats.
The Secure Coding Practices Bootcamp offers hands-on, jargon-free training. Developers master the OWASP Top 10, encryption, and authentication through practical labs and live sessions, ensuring they ship safer code immediately. Ready to secure your code? Join the Bootcamp.
References
- https://ceur-ws.org/Vol-4146/paper16.pdf
- https://doi.org/10.3850/978-981-08-7300-4_0006
