The secure coding requirements cyber Resilience Act is changing how software is built, tested, and maintained. It pushes teams to think about security from the very beginning, not as an afterthought. From our experience, projects that ignore early safeguards often lead to higher risks and costly fixes later.
That’s why secure coding requirements matter more than ever. Understanding them early helps teams stay compliant and build stronger systems. Keep reading to see how these requirements work in real development scenarios.
Secure Coding Requirements Cyber Resilience Act Key Insight
A quick overview before we go deeper:
- Security must be integrated from the start of development
- Secure Coding Practices work best as the first line of defense
- Consistency in coding habits reduces long-term risks
What the Cyber Resilience Act Requires from Developers
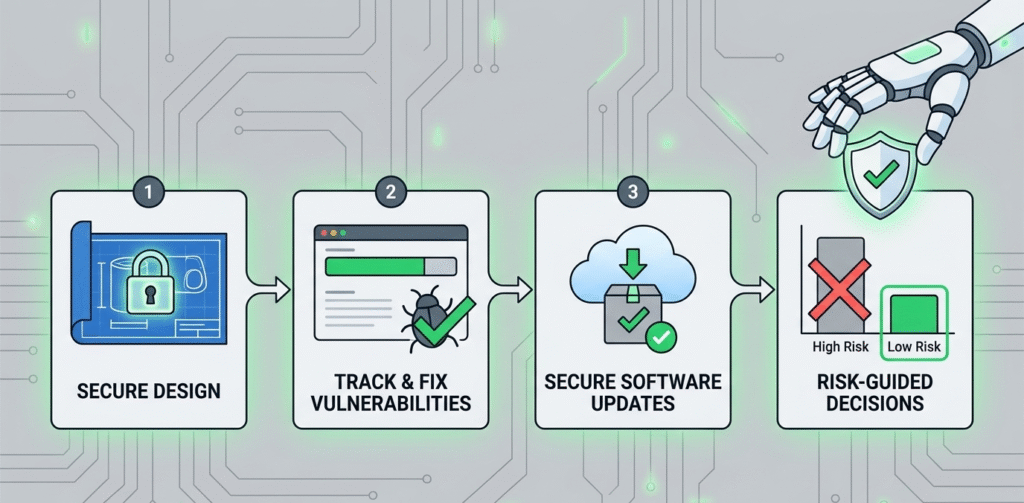
The Cyber Resilience Act sets clear expectations for a secure development lifecycle. It requires organizations to reduce vulnerabilities before products reach users.
“Secure by default principles would impose a duty of care for the lifecycle of products… The new rules would “rebalance responsibility towards manufacturers”.” – Wikipedia
- Security must be built in during design and development
- Known vulnerabilities must be tracked and fixed quickly
- Software updates must remain secure over time
- Risk assessments must guide development decisions
In many teams, this shifts responsibility earlier into development. Instead of relying only on testing, developers must actively prevent issues.
Why Secure Coding Practices Come First
When we implement security early, we reduce risks before they spread across systems. This proactive approach to software risk management CRA makes Secure Coding Practices the natural starting point because they directly influence how code is written.
“The CRA regulates the security properties and lifecycle obligations of products entering those environments… entity-level obligations become easier to operationalize when the products used in the environment carry more traceable evidence about support, conformity, and vulnerability handling.” – ResearchGate
We focus on:
- Input validation and output encoding
- Proper authentication and authorization logic
- Avoiding hardcoded secrets
- Writing clean, reviewable code
From our experience, small habits, like validating inputs, prevent major vulnerabilities later and reduce rework significantly.
Key Secure Coding Requirements Explained
Credits: Somco Software
To meet compliance, teams must align coding habits with specific security expectations.
| Requirement | What It Means in Practice | Impact on Development |
| Input Validation | Check all user inputs before processing | Prevents injection attacks |
| Error Handling | Avoid exposing system details in errors | Reduces information leakage |
| Authentication Security | Use strong, verified authentication methods | Protects user data |
| Dependency Management | Monitor and update third-party libraries | Avoids inherited vulnerabilities |
| Secure Configuration | Disable unnecessary features and services | Limits attack surface |
These are simple individually, but consistency is what makes them effective.
Integrating Secure Coding Cyber Resilience Act into Daily Workflow
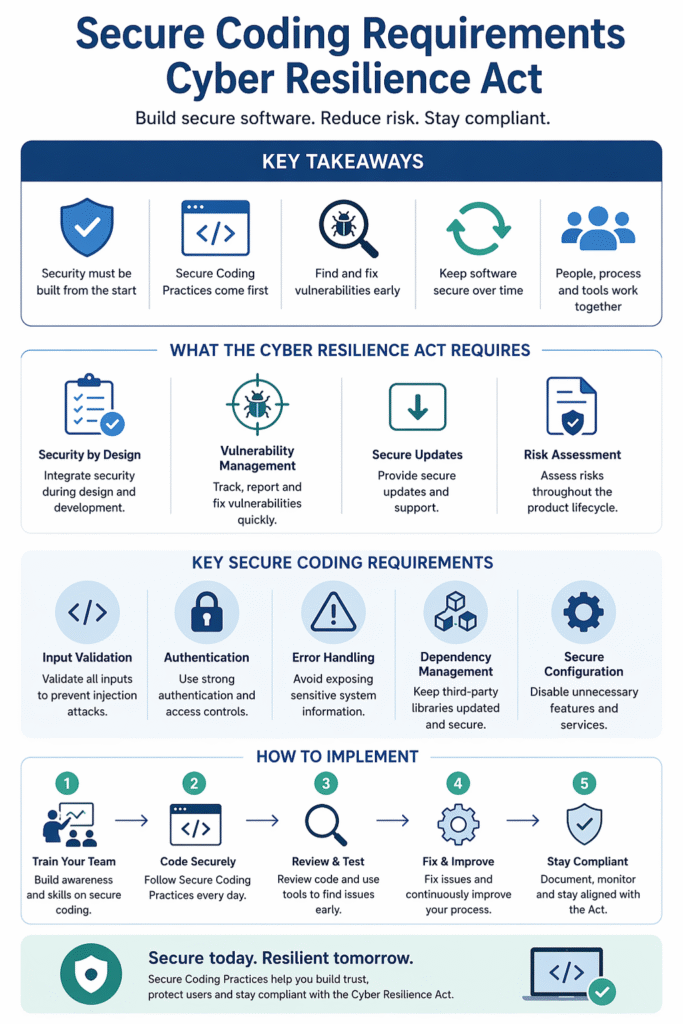
Adopting secure coding is less about tools and more about habits. We’ve found that implementing a Cyber Resilience Act secure development lifecycle works best when it fits naturally into existing workflows.
- Add security checks in code reviews
- Use automated tools to scan vulnerabilities
- Train developers regularly on common risks
- Document secure coding guidelines clearly
Instead of treating security as a final step, embedding it into daily tasks makes compliance easier and more sustainable.
Common Challenges and How Teams Overcome Them
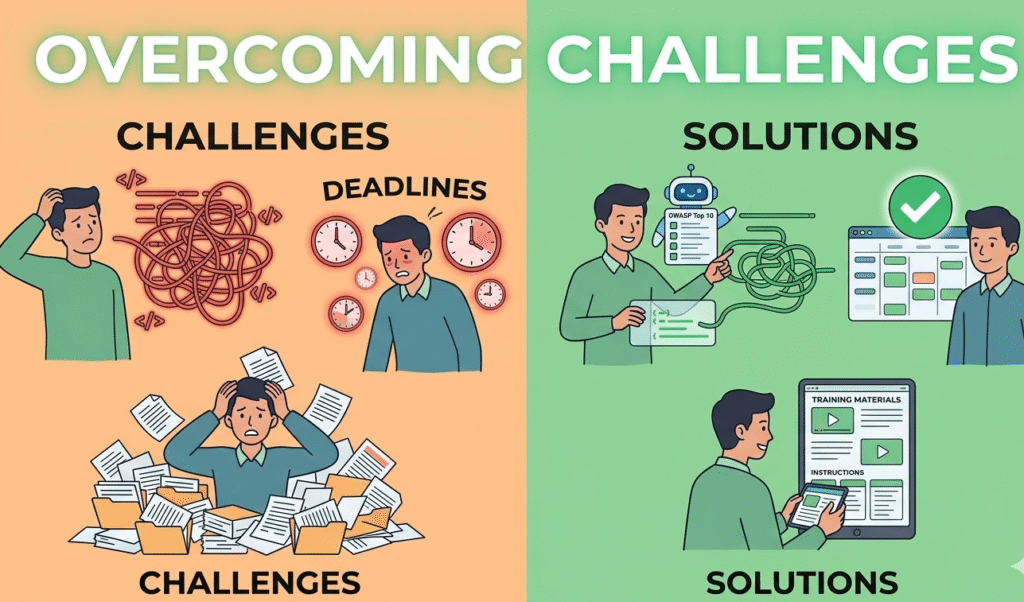
Many teams struggle at first when adapting to these requirements.
Typical challenges include:
- Limited security knowledge among developers
- Time pressure reducing focus on secure coding
- Over-reliance on tools instead of practices
From our experience, the solution is balance. Tools help detect issues, but Secure Coding Practices prevent them. Teams that invest in training and clear guidelines usually adapt faster.
FAQ
What are secure coding requirements under the Cyber Resilience Act?
Secure coding requirements under the Cyber Resilience Act focus on reducing vulnerabilities during development. This means writing code that is safe, tested, and reviewed properly.
Developers are expected to follow Secure Coding Practices, handle risks early, and avoid common issues like weak validation or insecure authentication. The goal is to make software safer before it reaches users.
Why are Secure Coding Practices important for compliance?
Secure Coding Practices help teams meet compliance by preventing security issues from the start. Instead of fixing problems later, developers build secure features from the beginning.
This approach supports Cyber Resilience Act requirements like risk reduction and secure updates. In real work, it also saves time, because fewer bugs and vulnerabilities appear during testing or after release.
How can developers apply secure coding requirements daily?
Developers can apply secure coding requirements by making small, consistent changes in their workflow. For example, validating inputs, reviewing code carefully, and avoiding unsafe shortcuts. Secure Coding Practices become part of daily habits, not extra tasks.
Over time, this makes development smoother and more secure without slowing things down or adding too much complexity.
What risks happen if secure coding is ignored?
Ignoring secure coding requirements can lead to serious problems. Applications may become vulnerable to attacks, data leaks, or system failures. Under the Cyber Resilience Act, this can also create compliance issues.
From experience, fixing these problems later takes more time and resources compared to preventing them early through Secure Coding Practices during development.
Building Security into Every Line of Code
Secure coding requirements under the Cyber Resilience Act are not just about compliance, they reshape how software is built. From our experience, starting with Secure Coding Practices makes everything smoother, from risk management to long-term maintenance. Teams that apply these habits early reduce vulnerabilities and avoid costly rework.
If you want to strengthen real-world skills, the Secure Coding Practices Bootcamp offers hands-on training to help developers build safer, more resilient software from day one.
References
- https://en.wikipedia.org/wiki/Cyber_Resilience_Act
- https://www.researchgate.net/publication/403513884_The_Cyber_Resilience_Act_as_an_Engineering_Decision_Framework_for_IT-OT_Systems

