If you build software for the European market, cybersecurity is no longer optional, it is part of a strict legal and regulatory context. The EU has introduced layered security legislation that directly impacts how digital products are designed, developed, and maintained.
Frameworks like the Cyber Resilience Act and NIS2 Directive turn security into a formal legal compliance obligation. From our experience at Secure Coding Practices, aligning early helps reduce regulatory risk, improve efficiency, and avoid costly compliance failures. Keep reading to understand what this means in practice.
Key Insight on Legal & Regulatory Context
Here are the most important points you should understand before diving deeper:
- EU cybersecurity law for software combines multiple legal and regulatory instruments, not a single rule
- Understanding cyber resilience act vs nis2 is essential to manage both product and organizational obligations
- Aligning with secure software development eu law and lifecycle requirements ensures compliance and market access
EU Cybersecurity Law for Software
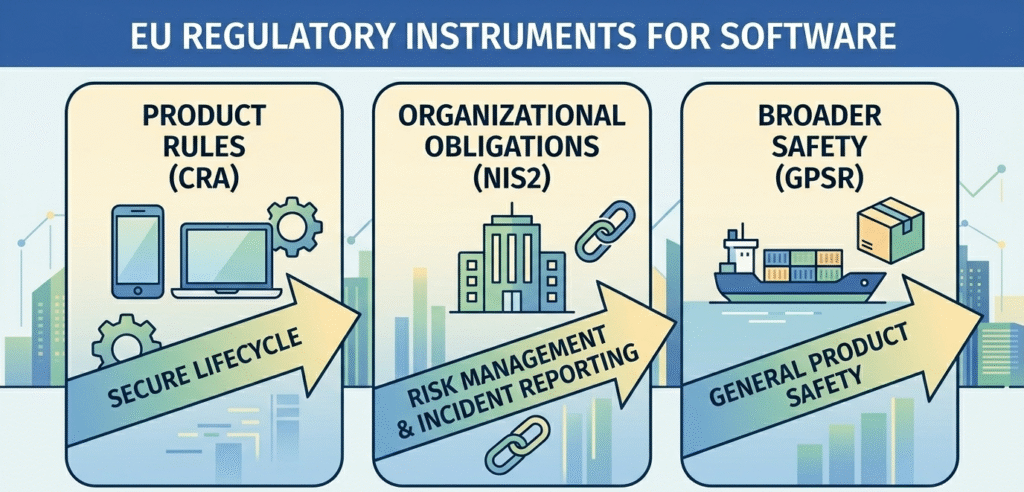
The eu cybersecurity law for software is shaped by multiple regulatory instruments that define how organizations approach regulation and compliance.
“Cybersecurity has become a fundamental component of product safety and market trust in the digital economy.” – European Union Agency for Cybersecurity (ENISA)
It includes:
- Product-level rules under the Cyber Resilience Act
- Organizational obligations under the NIS2 Directive
- Broader safety coverage via the General Product Safety Regulation
This creates a complex regulatory environment where engineering, senior management, and governance structures must align. Without this, companies risk civil liability, regulatory disciplinary actions, and reduced access to markets.
Cyber Resilience Act vs NIS2
Credits: LawMint
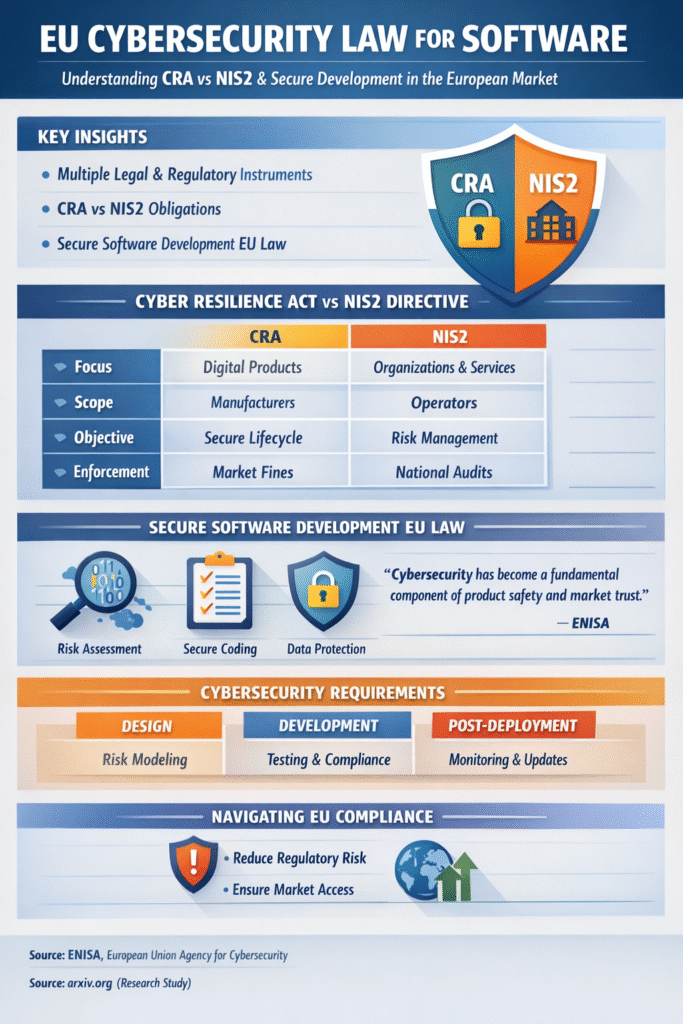
Understanding the Cyber Resilience Act vs NIS2 helps clarify responsibilities across product and organizational levels, ensuring both technical and administrative domains are covered.
| Aspect | Cyber Resilience Act | NIS2 Directive |
| Focus | Digital products & software | Organizations & services |
| Scope | Manufacturers, developers | Operators, providers |
| Objective | Secure product lifecycle | Risk & incident management |
| Enforcement | Market restrictions, fines | National audits, penalties |
From what we’ve seen:
- CRA impacts requirements engineering and product design
- NIS2 drives internal policies, reporting, and board level accountability
Together, they form a complete legal and regulatory system.
EU Product Security Legislation Overview
A clear EU product security legislation overview shows how cybersecurity fits into broader legal and regulatory instruments, helping firms navigate secure coding regulatory expectations within the single market.
Key elements:
- Cybersecurity obligations under CRA
- Product safety under the General Product Safety Regulation
- Policy direction from the European Commission
These frameworks also connect with data privacy, international trade laws, and Environmental & ESG Regulation. Organizations that align early benefit from smoother implementation of regulations and reduced exposure to legislative change.
Secure Software Development EU Law
Under secure software development EU law, development practices must align with enforceable legal requirements to ensure software security by design is maintained throughout the product lifecycle.
Teams should:
- Conduct cyber security impact assessment early
- Establish secure operating procedures
- Prepare for personal data breach scenarios
- Protect intellectual property rights
This also includes strong identity management systems and documentation for compliance checking. In practice, secure development is now directly tied to legal authority, not just technical quality.
Cybersecurity Requirements for Software EU
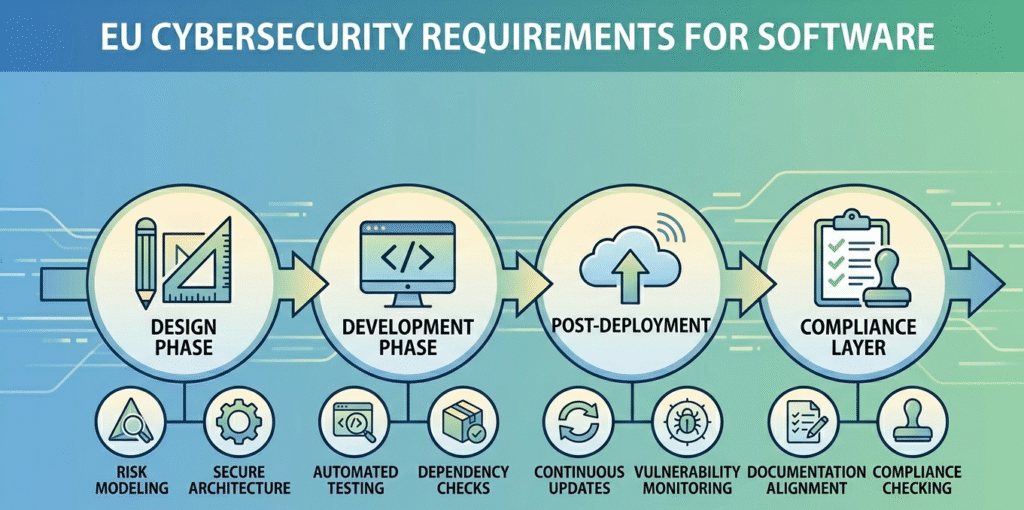
The cybersecurity requirements for software EU apply across the full lifecycle, mandating that teams adopt security by design CRA requirements to mitigate vulnerabilities before they reach production.
“Secure software development requires integrating security throughout the entire lifecycle, from design to deployment and maintenance.” – ARXIV
Design Phase
- Risk modeling and constraint categories
- Secure architecture planning
Development Phase
- Automated testing and dependency checks
- Software supply chain visibility
Post-Deployment
- Continuous updates and vulnerability management
- Monitoring using identifiers like IP Address
Compliance Layer
- Documentation aligned with compliance criteria
- Alignment with frameworks like FATF recommendations and Basel III
Integrating these requirements into development workflows strengthens both security and corporate reputation.
FAQ
How does the legal and regulatory framework affect software development decisions?
The legal and regulatory framework shapes how teams handle data privacy, security, and risk from the start. It defines legal requirements, compliance criteria, and internal policies. Ignoring it can lead to compliance failures or regulatory disciplinary actions.
By aligning development with regulatory compliance early, teams improve operational efficiency and reduce regulatory risk across the entire software lifecycle and business environment.
What are common compliance failures companies face under EU cybersecurity regulations?
Common compliance failures include weak data privacy controls, missing documentation, and poor compliance checking processes. Many teams ignore regulatory impact assessment or fail to update internal policies after legislative change.
This increases regulatory risk, civil liability, and damage to corporate reputation. Strong compliance strategies and clear governance structures help organizations meet legal requirements and avoid costly penalties or enforcement actions.
Why is data protection impact assessment important for regulatory compliance?
A data protection impact assessment helps identify risks related to personal data breach, identity management systems, and data privacy. It ensures compliance with legal and regulatory instruments while supporting secure operating procedures.
Organizations use it to meet compliance criteria, reduce regulatory risk, and prepare for external authorities. It also strengthens trust, improves corporate reputation, and supports long-term regulation and compliance efforts.
How do international trade laws impact cybersecurity requirements for software?
International trade laws influence how companies meet cybersecurity requirements across different markets. They affect patent policy, intellectual property rights, and access to markets. Businesses must align with multiple regulatory instruments and legal requirements to stay compliant.
This also impacts the business environment, requiring strong compliance strategies and governance structures to manage regulatory risk and maintain smooth cross-border operations.
Navigating the EU Legal & Regulatory Context
The EU’s cybersecurity rules make security a required part of software development. By understanding eu cybersecurity law for software, cyber resilience act vs nis2, and applying secure software development eu law, teams can meet cybersecurity requirements for software eu more easily.
From our experience at Secure Coding Practices, starting early and integrating compliance into development helps avoid risks and keeps your product ready for the EU market.
References
- https://industrialcyber.co/secure-by-design/enisa-playbook-calls-for-security-by-design-across-product-lifecycle-urges-shift-to-continuous-cybersecurity/
- https://arxiv.org/abs/2211.16987
Related Articles
- https://securecodingpractices.com/eu-cybersecurity-law-for-software/
- https://securecodingpractices.com/cyber-resilience-act-vs-nis2/
- https://securecodingpractices.com/eu-product-security-legislation-overview/
- https://securecodingpractices.com/secure-software-development-eu-law/
- https://securecodingpractices.com/cybersecurity-requirements-for-software-eu/
- https://securecodingpractices.com/secure-coding-regulatory-expectations-eu/
- https://securecodingpractices.com/secure-coding-eu-regulatory-context/
- https://securecodingpractices.com/software-security-by-design-eu/
- https://securecodingpractices.com/security-by-design-cra-requirements/

