
The secure coding EU regulatory context is shaping how modern software is built across industries. Security is no longer treated as a technical add-on but as a legal and operational requirement. From our experience, teams that understand this context early can adapt faster and avoid costly compliance issues.
By aligning development practices with EU expectations, organizations can build safer products while maintaining efficiency. Keep reading to understand how regulations influence secure coding in the EU.
EU Secure Coding Context: Key Insights to Remember
Understanding the secure coding EU regulatory context becomes easier when focusing on the essentials.
- Regulations require security across the full lifecycle
- Developers play a central role in compliance
- Continuous improvement is more effective than one-time fixes
Why the EU Regulatory Context Matters
The EU has taken a strong position on cybersecurity, making secure coding part of a broader legal and regulatory context that affects all digital products. From what we’ve seen, this shift affects not only large organizations but also small development teams.
“embedding compliance early into the software development lifecycle not only supports regulatory alignment but also improves system resilience and trustworthiness” – Sciencedirect
Key reasons why this matters:
- Software is treated as a regulated product
- Security failures can lead to legal consequences
- User safety and data protection are prioritized
This context pushes developers to think beyond functionality and focus on long-term security and reliability.
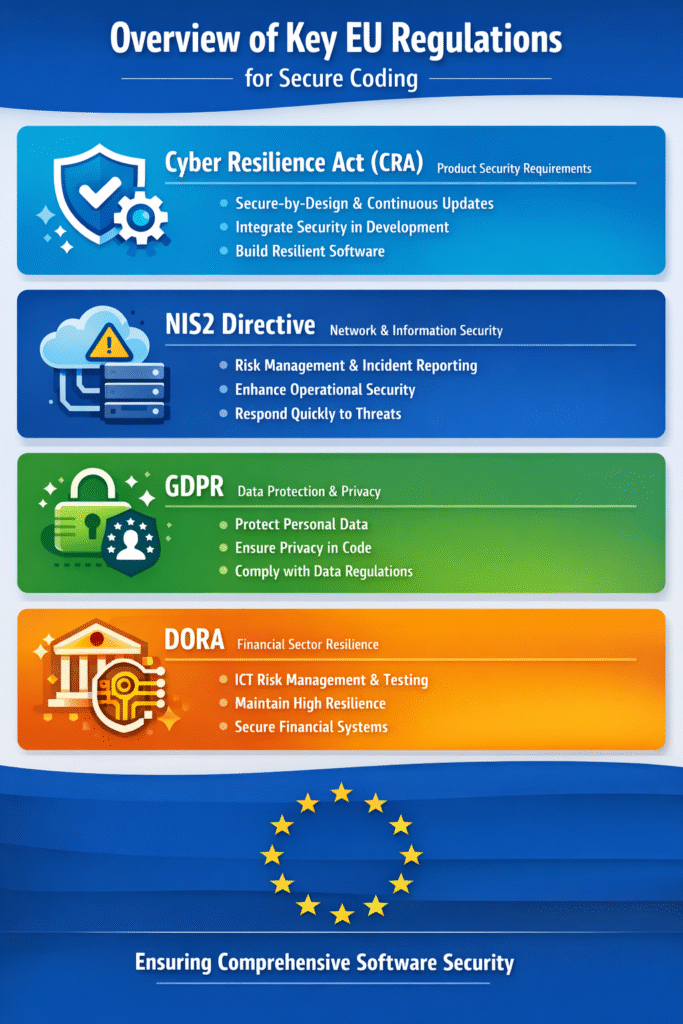
Key Regulations Shaping the EU Context
Several major regulations define the secure coding regulatory expectations in the EU.
| Regulation | Main Focus | Key Security Requirement | Impact on Developers |
| Cyber Resilience Act (CRA) | Product software security | Secure-by-design and continuous updates | Developers must build security into every stage of development |
| NIS2 Directive | Network and information security | Risk management and incident reporting | Requires stronger operational security and faster response to threats |
| GDPR | Personal data protection | Secure handling of user data | Developers must ensure privacy and data protection in code design |
| DORA | Digital resilience in finance | ICT risk management and testing | Demands high resilience and regular security testing in financial systems |
Together, these regulations establish a high bar for secure software development under EU law, ensuring software remains resilient throughout its lifecycle.
Core Principles Behind EU Secure Coding Expectations
Credits: IT Encyclopedia
Despite different regulations, the underlying principles are similar.
From our experience at Secure Coding Practices, these principles guide most compliance efforts:
- Security by design and by default
- Continuous risk assessment
- Transparency and documentation
- Accountability across teams
- Rapid response to vulnerabilities
These principles help teams move from reactive fixes to proactive security strategies.
How the Regulatory Context Affects Developers
The secure coding EU regulatory context directly impacts daily development work.
“security in network and information systems acquisition, development and maintenance,” – Wikipedia
Developers are now expected to:
- Write code with security in mind from the start
- Follow secure coding standards and guidelines
- Participate in security testing and reviews
- Understand basic regulatory requirements
We’ve noticed that developers who embrace this shift often produce cleaner, more maintainable code, not just more secure systems.
Practical Steps to Align with EU Expectations
Adapting to the regulatory context doesn’t require major disruption. It requires structured changes.
Common steps teams take include:
- Embedding security into CI/CD pipelines
- Using automated vulnerability scanning tools
- Training developers regularly
- Managing third-party risks carefully
- Keeping clear documentation for compliance
Consistency is key. Small improvements, applied regularly, lead to strong compliance over time.
Common Challenges in the EU Regulatory Environment
Even with clear frameworks, teams often face challenges.
Some of the most common include:
- Keeping up with evolving regulations
- Limited internal security expertise
- Balancing speed and security
- Managing complex supply chains
From our experience, the biggest improvement comes when teams treat security as part of development culture, not an external requirement.
How We Approach This Context
At Secure Coding Practices, we view the EU regulatory context as an opportunity rather than a barrier.
We focus on:
- Making security practical for developers
- Translating regulations into actionable steps
- Supporting teams with real-world training
By simplifying complex requirements, we help teams align with regulations while maintaining development speed and quality.
FAQ
What does secure coding mean under EU Cyber Resilience Act compliance?
Secure coding under EU Cyber Resilience Act compliance means building software with security in mind from the start. Developers must reduce vulnerabilities during design, coding, testing, and maintenance stages.
It focuses on preventing risks like data breaches and unauthorized access. The goal is to ensure software placed in the EU market is secure, resilient, and continuously maintained against emerging cyber threats.
How does NIS2 affect secure software development for EU developers?
NIS2 affects software development by requiring stronger cybersecurity practices for essential and important services. Developers must follow stricter risk management, incident reporting, and security controls.
It pushes organizations to integrate security into development processes, not treat it as optional. This includes secure coding practices, regular updates, and proper vulnerability handling to reduce operational risks across digital infrastructure.
What are key secure coding requirements in EU cybersecurity regulations?
EU cybersecurity regulations require developers to follow secure coding principles like input validation, proper authentication, encryption, and error handling. Code must be written to minimize vulnerabilities and prevent exploitation.
Regular security testing and patch management are also expected. These requirements aim to reduce software weaknesses and ensure products meet baseline security standards before deployment in the EU market.
How to implement secure software development lifecycle in EU compliance context?
To implement a secure software development lifecycle in EU compliance, security must be included at every stage. This starts from planning and design, followed by secure coding, testing, deployment, and maintenance.
Developers should use threat modeling, code reviews, and vulnerability scanning. Continuous monitoring and timely updates are also necessary to meet evolving EU cybersecurity expectations effectively.
Secure Coding in the EU Regulatory Context: Final Insights
The secure coding EU regulatory context continues to evolve, but its direction is clear: security must be proactive, continuous, and built into development. Teams that understand this early are better prepared for compliance and long-term success.
From our experience, practical learning delivers real results. The Secure Coding Practices Bootcamp equips developers with hands-on skills to build secure software.
References
- https://www.sciencedirect.com/science/article/pii/S0950584926000224?via%3Dihub
- https://en.wikipedia.org/wiki/Secure_coding

