The EU Cyber Resilience Act for Secure Coding Practices requires all products with digital components, software, connected devices, and embedded systems, to meet strict cybersecurity standards. Starting in 2026, manufacturers must build security into every stage, from design to end-of-support, ensuring vulnerabilities are minimized and users are protected.
Implementing secure coding practices is central to meeting these obligations, maintaining trust, and avoiding regulatory penalties. For developers, product teams, and compliance officers, understanding the CRA’s requirements is essential to entering EU markets confidently. Keep reading to explore practical steps and strategies for integrating secure coding under the CRA.
Quick Wins for CRA Compliance
To stay compliant and secure under the CRA, focus on these essential practices:
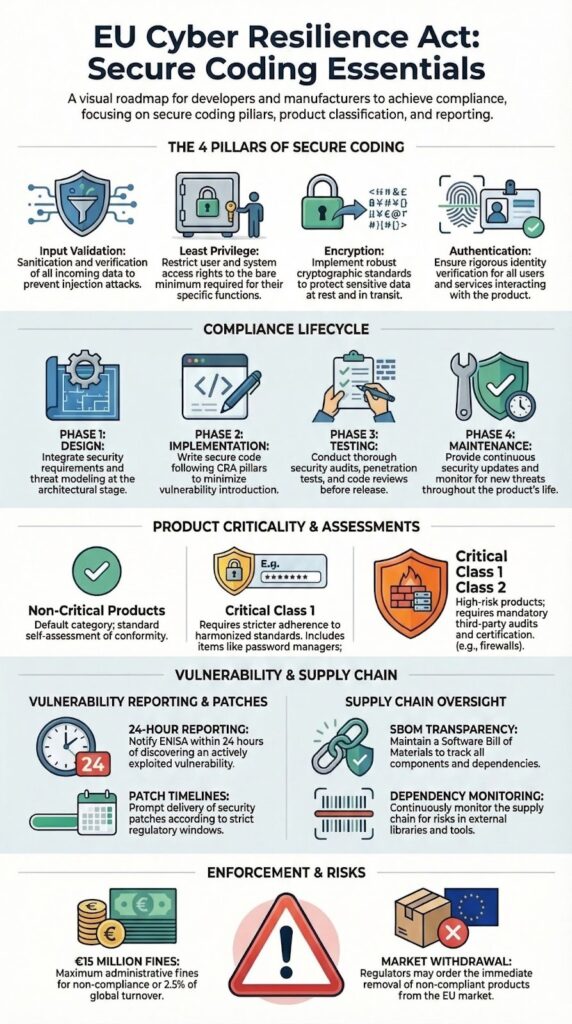
- Secure coding practices: input validation, least privilege, encryption, and strong authentication.
- Full secure development lifecycle: vulnerability management and supply chain transparency.
- Compliance measures: conformity assessments, CE marking, and post-market surveillance to avoid penalties.
CRA overview & purpose
The CRA establishes a unified approach to cybersecurity for all products with digital elements sold in the EU. Its goal is to reduce systemic risks by enforcing secure-by-design and secure-by-default principles.
As highlighted by Linux Foundation
“The Act shifts much of the security burden onto those who develop software, as opposed to the users of software.” – Linux Foundation
We’ve observed that focusing on reducing attack surfaces, implementing strong authentication, and applying encryption at rest and in transit directly supports CRA expectations. Teaching developers these methods in real-world scenarios allows them to understand not just the rules, but the reasoning behind them, which strengthens long-term security habits.
Key elements of the CRA include:
- Essential cybersecurity requirements for all products with digital elements (PDEs)
- Obligations for manufacturers, importers, and distributors
- Procedures for handling vulnerabilities and deploying timely patches
- Conformity assessment and CE marking
For us, these are more than regulatory mandates, they are actionable steps that make products safer and more resilient.
Scope & applicability

The CRA applies to software and hardware that can connect to networks, ranging from small IoT devices to enterprise operating systems.
In our bootcamp, we stress that understanding product classification early helps developers adopt the right security measures and align with CRA expectations from the start, especially when teams begin with a clear EU Cyber Resilience Act summary to understand how product categories affect compliance obligations.
Products are categorized by criticality:
| Product class | Examples | CRA obligation level |
| Non-critical | Consumer apps, small IoT devices | Internal production control (self-assessment) |
| Critical class 1 | Browsers, firewalls | Third-party assessment by a notified body |
| Critical class 2 | Operating systems, PKI infrastructure | Enhanced third-party assessment with CE marking |
We’ve seen that even non-critical products benefit from strong secure coding practices. Key areas we focus on include:
- Input validation to prevent common vulnerabilities
- Encryption for data at rest and in transit
- Enforcing least-privilege access controls
Certain products are excluded if they fall under sector-specific regulations, such as medical devices or motor vehicles. Still, we encourage treating every project as a security-first effort.
Legal & regulatory context
The EU positions the CRA as a regulation that applies directly across all Member States, which becomes easier to understand when developers review what the EU Cyber Resilience Act is and how it functions within the broader EU cybersecurity framework.
It works alongside the NIS2 Directive, the Radio Equipment Directive, and existing product safety frameworks to create a consistent cybersecurity baseline.
For non-EU manufacturers, we’ve observed that engaging with EU representatives and following conformity assessment procedures early prevents delays and reduces the risk of non-compliance.
Market surveillance authorities oversee enforcement, while notified bodies assess critical products for conformity. In our training sessions, we’ve seen teams benefit when CRA obligations are integrated into standard development workflows.
Doing this early reduces friction, improves audit readiness, and ensures that secure coding practices become a natural part of product development rather than an afterthought.
Key points of the CRA’s legal framework include:
- Direct applicability across the EU without national transposition
- Harmonization of essential cybersecurity requirements
- Reporting obligations for actively exploited vulnerabilities within 24 hours
Through our hands-on experience, it’s clear that secure coding practices aren’t just technical best practices, they are a regulatory requirement.
Secure coding principles

Alt Text: A developer typing colorful code on a laptop at night applying EU Cyber Resilience Act for Secure Coding Practices standards
Secure coding forms the backbone of CRA compliance, particularly when teams understand the broader cyber resilience act software impact on how modern applications, devices, and connected systems must be designed and maintained.
In our bootcamp, we teach developers standards that address the most common vulnerabilities while preparing products to meet regulatory requirements. Our approach covers:
- Input validation to prevent injection attacks
- Applying the least-privilege principle for all user and system operations
- Encryption at rest and in transit, with proper key management
- Avoiding hardcoded credentials and outdated algorithms
- Implementing robust authentication and authorization controls
This includes records from static and dynamic code analysis, fuzzing tests, and thorough security reviews. In our experience, teams that track these processes consistently find audits and assessments far less stressful.
Practical measures we follow include:
- Conducting threat modeling for every product feature
- Performing penetration testing before each release
- Maintaining a secure-by-design architecture aligned with CRA essential requirements
Through hands-on training, we’ve seen that integrating these practices early not only ensures compliance but also significantly improves real-world security.
Secure development lifecycle
The CRA stresses the need to integrate security at every stage of the software lifecycle. From our experience running a secure development bootcamp, aligning each phase with CRA expectations helps teams embed secure coding habits naturally, rather than treating compliance as an afterthought.
Insights from EU Digital Strategy indicate
“The CRA introduces mandatory cybersecurity requirements for manufacturers, covering the planning, design, development and maintenance of such products.” – EU Digital Strategy
We structure our secure development lifecycle (SDL) around four main phases:
- Requirements & design – Conduct cybersecurity risk assessments, analyze misuse and abuse cases, and design a security-focused architecture. Addressing risks early prevents costly vulnerabilities later.
- Implementation – Apply secure coding practices, manage dependencies carefully, and perform static and dynamic code analysis. Teams that adopt these measures early catch most issues before testing.
- Testing – Use fuzzing, penetration testing, and automated security checks to identify weaknesses and improve overall security posture.
- Release & maintenance – Ensure timely patching, vulnerability remediation, and clear end-of-support disclosures to maintain long-term security compliance.
We’ve seen firsthand that embedding secure coding practices at each stage not only reduces downstream vulnerabilities but also simplifies conformity assessments.
Vulnerability & risk management
The CRA requires manufacturers to handle vulnerabilities in a systematic way. In our secure development bootcamp, we emphasize that understanding and managing risk isn’t just a regulatory requirement, it’s central to building resilient software.
Key practices we teach include:
- Conducting cybersecurity risk assessments that cover confidentiality, integrity, and availability
- Implementing coordinated vulnerability disclosure policies
- Performing continuous vulnerability scanning and monitoring dependencies
- Delivering security updates within defined timelines, with special attention to actively exploited vulnerabilities
From our experience, tracking threats using SBOMs and automated scanning tools helps teams prioritize patches effectively and reduce exposure, reinforcing why the Cyber Resilience Act matters for maintaining secure products throughout their lifecycle.
We’ve observed that teams who adopt these practices early handle incidents more efficiently and prevent minor issues from escalating.
CRA also mandates prompt reporting of security incidents to authorities, often within 24 hours. We train developers to integrate reporting processes into standard workflows so transparency and rapid mitigation become part of the product lifecycle rather than an afterthought. This approach strengthens both compliance and real-world security readiness.
Open source & supply chain
Open source and third-party components play a critical role in CRA compliance. In our secure development bootcamp, we stress that supply chain security is as important as the code your team writes in-house. Overlooking external dependencies can create vulnerabilities that impact the entire product.
We guide teams to follow best practices such as:
- Generating and maintaining Software Bills of Materials (SBOMs)
- Monitoring upstream projects for vulnerabilities
- Ensuring open source compliance and governance
- Documenting risk assessments for all third-party components
While non-commercial OSS projects are generally exempt, we emphasize that once they are integrated into commercial products, CRA obligations extend to every component, a concept that becomes clearer when reviewing how the EU Cyber Resilience Act is explained across modern software supply chains.
From our experience, teams that actively track dependencies and monitor upstream projects can detect issues before they become systemic problems. Proactive supply chain management not only reduces risk but also simplifies audits and conformity assessments.
Compliance & enforcement
Demonstrating CRA compliance requires more than secure code, it involves clear documentation and ongoing oversight.
From our experience training secure development teams, integrating compliance practices into daily workflows reduces stress during audits and ensures readiness for inspections, particularly when developers understand a structured cyber resilience act overview for developers and how it translates into operational requirements.
Key steps include:
- Applying CE marking to indicate conformity
- Maintaining technical cybersecurity documentation for 10+ years
- Performing internal production control for non-critical products and third-party assessments for critical products
- Cooperating with market surveillance authorities during inspections, corrective actions, and potential penalties
Penalties for non-compliance can be severe, reaching up to €15 million or 2.5% of global turnover, with the possibility of market restrictions or product withdrawals.
We’ve seen firsthand that teams who embed compliance processes, covering documentation, vulnerability management, and secure development lifecycle adherence, are better prepared to meet regulatory demands without disrupting engineering schedules.
By treating compliance as part of standard workflows rather than a separate task, developers and product teams gain confidence that their products remain both secure and aligned with CRA requirements throughout the lifecycle.
Practical implementation
Credits : hopelabs
Preparing for CRA compliance works best as a stepwise process, and teams often benefit from starting with a structured CRA overview and purpose to clearly understand how regulatory requirements translate into practical development workflows.
In our bootcamp, we guide teams to approach readiness methodically, ensuring secure coding and SDL practices are integrated from the start rather than added later.
We recommend beginning with a full inventory of all products containing digital elements and classifying them by criticality. From there, align your secure development lifecycle and coding standards with CRA essential requirements. Implementing SBOM generation, automated vulnerability scanning, and patch management early helps teams stay ahead of potential risks.
Key steps we emphasize include:
- Appointing or maturing a Product Security Incident Response Team (PSIRT)
- Engaging with notified bodies early for critical product assessments
- Training developers on CRA-aligned secure coding and engineering security practices
- Establishing a vulnerability disclosure policy with timely patching workflows
Selecting tools for SBOM generation, static analysis, and dependency monitoring ensures reproducibility and audit readiness. From our experience, a phased rollout provides flexibility for both SMEs and large enterprises while maintaining rigorous compliance standards.
FAQ
What is the Cyber Resilience Act and how does it affect secure coding practices?
The Cyber Resilience Act (CRA regulation) is an EU cybersecurity law that defines essential cybersecurity requirements for all products with digital elements.
For developers, it emphasizes following secure coding standards, implementing input validation, and designing systems that are secure by design. These practices reduce vulnerabilities, ensure compliance with conformity assessment obligations, and support continuous security updates throughout the product lifecycle.
How should developers handle vulnerabilities under CRA regulations?
Under the CRA, developers must follow a structured coordinated vulnerability disclosure process and perform timely vulnerability remediation.
Companies should establish a dedicated Product Security Incident Response Team (PSIRT) to monitor, report, and patch actively exploited vulnerabilities. Critical issues require 24-hour notification to relevant authorities, while thorough technical documentation for cybersecurity supports effective incident response and post-market surveillance.
What are the key compliance steps for products with digital elements?
Compliance requires meeting essential cybersecurity requirements, performing cybersecurity risk assessments and threat modeling, and generating a software bill of materials (SBOM).
Manufacturers must maintain accurate cybersecurity documentation, implement secure coding standards, and provide clear security updates and support period declarations. For higher-risk products, engagement with a notified body is necessary, along with submitting a conformity declaration and obtaining CE marking for cybersecurity.
How can open source components be safely integrated under CRA?
Integrating open source components safely requires robust dependency management, upstream monitoring, and responsible open source stewardship.
Commercial open source software must meet commercial OSS obligations, while non-commercial OSS exemption may apply. Regular vulnerability scanning, automated security testing, and proper third-party component documentation reduce risks in critical products cybersecurity and ensure compliance with software lifecycle security and lifecycle support declaration requirements.
What ongoing developer practices support CRA compliance and product security?
Developers should undergo regular cybersecurity training, implement secure by default principles, and maintain strong engineering security practices.
Using static code analysis, dynamic analysis, fuzzing testing, and penetration testing identifies vulnerabilities early. Consistent patch management, security maintenance updates, and documenting misuse cases or abuse cases strengthen product security incident response and ensure alignment with a structured compliance roadmap under the CRA.
Strengthen Your Software Security Now
Struggling to meet the EU Cyber Resilience Act requirements can feel overwhelming, especially when product vulnerabilities risk your users and reputation. Reality check: ignoring secure coding now only makes issues bigger later.
Secure Coding Practices makes it simple to build safer software from the start. Their bootcamp gives hands-on, real-world guidance to implement SDL and security standards without the guesswork, helping your team reduce risks, stay compliant, and ship confident, secure products quickly.
References
- https://www.linuxfoundation.org/blog/understanding-the-cyber-resilience-act
- https://digital-strategy.ec.europa.eu/en/policies/cyber-resilience-act
Related Articles
- https://securecodingpractices.com/cra-overview-purpose/
- https://securecodingpractices.com/what-is-eu-cyber-resilience-act/
- https://securecodingpractices.com/eu-cyber-resilience-act-explained/
- https://securecodingpractices.com/eu-cyber-resilience-act-summary/
- https://securecodingpractices.com/why-cyber-resilience-act-matters/
- https://securecodingpractices.com/cyber-resilience-act-software-impact/
- https://securecodingpractices.com/cyber-resilience-act-overview-developers/
