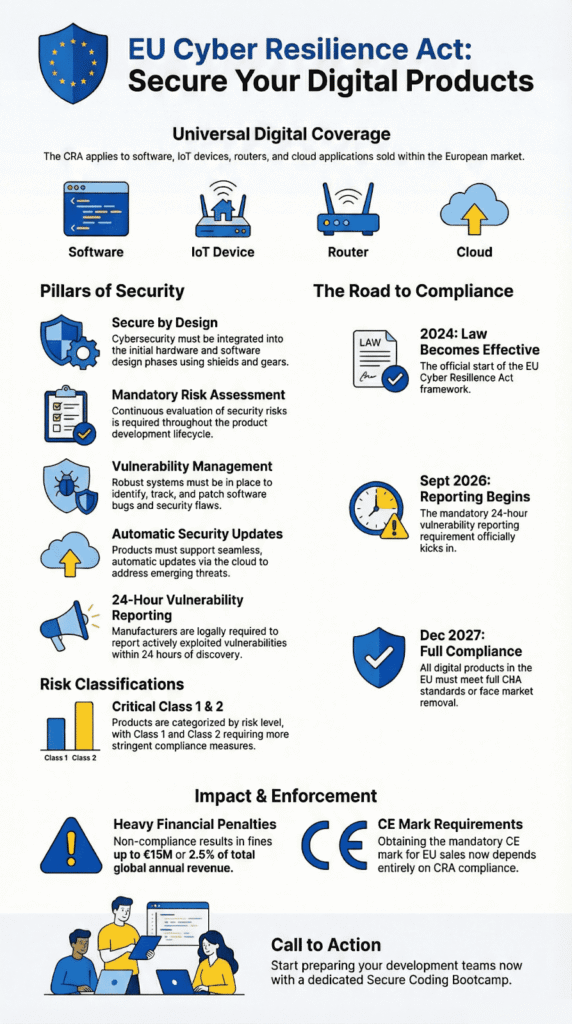
What Is EU Cyber Resilience Act? The EU’s Cyber Resilience Act is now in force. This law, officially Regulation 2024/2847, applies to almost anything with digital parts sold in the EU. The fines for ignoring it are severe, up to €15 million or 2.5% of a company’s total global revenue.
It specifically goes after the weak software, hidden bugs, and flimsy security common in connected devices. The European Commission proposed it after a surge in attacks on infrastructure and consumer tech.
If you make, import, or sell these products in the EU, you have to follow the rules. Here’s what matters most.
EU Cyber Resilience Act: Core Rules and Compliance Deadlines
- Build security in from the start, provide updates for the product’s life, and report serious flaws within 24 hours.
- Full compliance for new products is required by December 11, 2027. The 24-hour reporting starts on September 11, 2026.
- Your product’s CE mark now depends on meeting these cybersecurity standards and passing a formal assessment.
What Is the EU Cyber Resilience Act (CRA)?
The EU’s 2024 Cyber Resilience Act is now law, not a guideline. It sets mandatory security rules for every digital product sold in the EU.
It’s a central part of the EU’s wider product safety rules, working with the Cybersecurity Act and NIS2 Directive. Understanding the CRA overview and purpose makes it clear why the Commission acted: insecure connected devices, smart locks, factory sensors, are a genuine threat to supply chains and infrastructure.
The CRA covers software, hardware, and IoT devices. It forces manufacturers to build security in from the start and keep it up after the sale. Key requirements involve:
- Mandatory cybersecurity risk assessments.
- Ongoing security updates, typically for five years.
- Creating a machine-readable Software Bill of Materials (SBOM).
This is different from past voluntary standards. Now, getting the CE marking for market access across all EU Member States depends directly on complying with these cybersecurity rules.
Why Did the European Union Introduce the CRA?
Why did the EU create this law? The risk simply became too large. Tens of billions of connected devices worldwide created a massive attack surface.
From 2020, threats exploded. DDoS attacks grew massive, supply chain hacks turned routine, and reports from Germany’s BSI showed common firmware flaws in routers and smart devices. Before 2024, the EU’s cybersecurity rules were a scattered patchwork, and enforcement was inconsistent. As stated in the European Parliament News announcement,
“The Cyber Resilience Act will strengthen the cybersecurity of connected products, tackling vulnerabilities in hardware and software alike, making the EU a safer and more resilient continent. Parliament has protected supply chains, ensuring that key products such as routers and antiviruses are a priority for cybersecurity.” – European Parliament News
The CRA establishes one set of harmonized standards for the entire EU market. It complements directives like NIS2, which focus on organizational security, by setting rules for the products themselves.
The regulation uses a risk-based approach. It sorts products into categories like Critical Class 1 and Critical Class 2 (detailed in Annex III and IV), based on their potential impact on essential services and public safety.
What Products and Companies Does the CRA Cover?
If you make, import, or sell a product with digital elements in the EU, the CRA applies to you. This is true even for companies based outside Europe. In our courses, we stress that “products with digital elements” is a broad term. It covers any software or hardware that connects to a network, directly or indirectly.
This includes:
- Internet of Things (IoT) devices and smart home gadgets.
- Routers and other networking equipment.
- Software applications and cloud-based (SaaS) platforms.
- Industrial control systems and connectable hardware.
Some sectors are exempt because they have their own rules. The table below shows the main exceptions.
| Category | Regulatory Framework |
| Medical devices | EU Medical Device Regulation |
| Vehicles | Sector-specific EU law |
| Defense systems | Separate EU frameworks |
The law also touches open-source software, but mainly when it’s sold as part of a commercial product. Groups like the Eclipse Foundation are already talking about how this affects supply chain transparency and SBOM requirements.
What Are the Key Security Requirements Under the CRA?
Credits: hopelabs
The CRA places several core duties on manufacturers. Products must be secure from the start. Firms must conduct cybersecurity risk assessments, establish a vulnerability handling process, and retain all technical records for a decade. As explained by the International Bar Association’s legal analysis
“The CRA requires manufacturers to ensure that products with digital elements are designed, developed, and maintained in a way that guarantees an appropriate level of cybersecurity throughout their entire lifecycle. This obligation marks a significant shift towards embedding security as a fundamental element of product design and operation, rather than treating it as an afterthought. A core component of this requirement is the performance of a comprehensive risk assessment.” – International Bar Association’s legal analysis
The regulation requires specific protections at launch. These include data encryption, strong access controls, and defenses against common attacks like DDoS. According to the European Commission, products must have as few known, exploitable vulnerabilities as possible when they hit the market.
Manufacturers also need to create an EU Declaration of Conformity and prove they meet the rules.
Key technical measures are:
- Secure Boot mechanisms.
- Strong access controls and encryption.
- Automated security updates, separate from feature updates.
- Ongoing vulnerability management and CVE monitoring.
From our bootcamp experience, we know that baking in Secure Coding Practices from the start makes everything easier later. Writing secure code from the first commit simplifies the official conformity assessment.
It also helps avoid costly last-minute testing and delays. Teams that already experiment with conversational programming tools often find it easier to document decisions and track security assumptions early in the lifecycle. The CRA essentially makes these secure development practices a legal requirement.
What Are the CRA Vulnerability Reporting Rules?

Starting September 11, 2026, the rules tighten sharply. If a manufacturer discovers an actively exploited vulnerability, they must report it to national CSIRTs and ENISA within 24 hours.
This tight reporting even applies to certain older “legacy” products under attack. The schedule is fixed:
- Initial alert: Within 24 hours of discovery.
- Technical details: Within 72 hours.
- Final report on the fix: Within 14 days.
The European Commission states that companies must report both exploited vulnerabilities and any severe security incidents. This is different from laws like NIS2. NIS2 mainly affects critical service providers, while the CRA targets the product manufacturers and software developers themselves.
When Does the Cyber Resilience Act Take Effect?
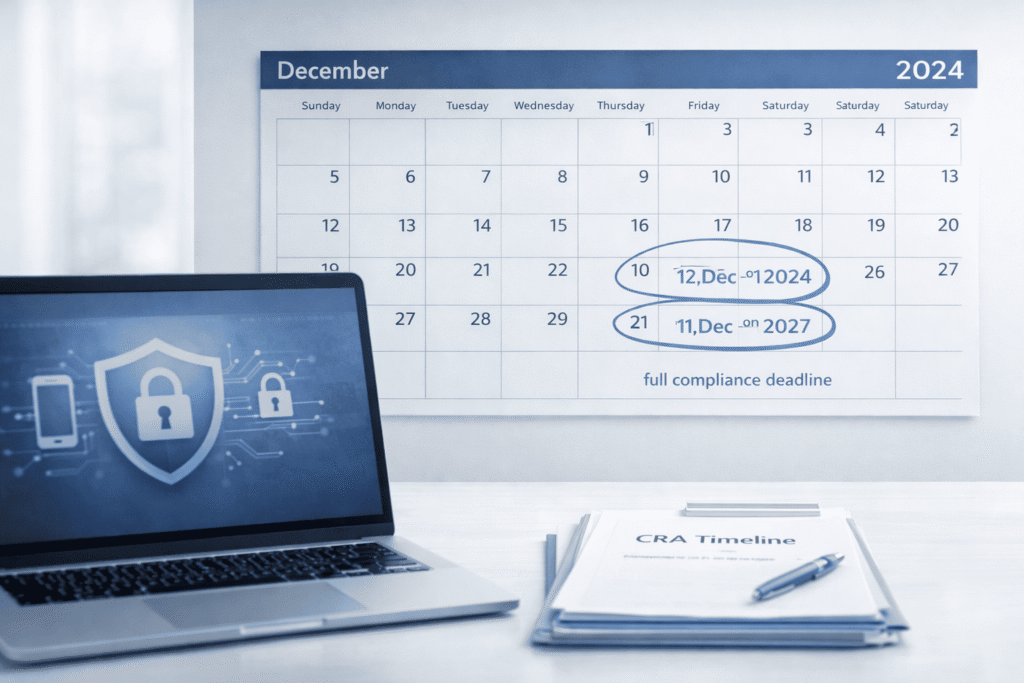
The law took effect on December 10, 2024, but the rules roll out gradually.
The timeline is simple:
- 2024: The law is official.
- September 11, 2026: The 24-hour vulnerability reporting rule begins.
- December 11, 2027: All new products must be fully compliant.
The penalties are severe: fines can be €15 million or 2.5% of a company’s global annual revenue, whichever is higher. Authorities can also pull products from the market or revoke a CE mark.
How Does the CRA Compare to the NIS2 Directive?
Here’s the difference: the CRA secures products. The NIS2 Directive secures organizations, setting rules for essential service providers on governance, risk management, and incident reporting.
The main differences are clear in this table:
| Dimension | Cyber Resilience Act | NIS2 Directive |
| Focus | Product security | Organizational cybersecurity |
| Reporting | 24-hour exploited vulnerability reporting | Incident reporting timelines |
| Enforcement | CE marking and fines | National authority oversight |
| Scope | Products with digital elements | Essential and important entities |
In practice, these laws can overlap. A business making smart sensors, for example, could need to follow both the CRA for its product and NIS2 for its own operations.
How Should Businesses Prepare for the EU Cyber Resilience Act?
Don’t wait. Start preparing now by doing a structured cybersecurity risk assessment and making secure coding a part of your entire development process.
We recommend a phased approach.
Right now, you should:
- Take an inventory of all components in your digital supply chain.
- Start creating a machine-readable Software Bill of Materials (SBOM).
- Begin gathering the technical documentation you’ll need for the CE marking process.
Before 2026, set up your internal workflow for the mandatory 24-hour vulnerability reports. This means defining who finds issues, who reports them to ENISA and national CSIRTs, and testing the entire process.
Before 2027, manufacturers need to finish the formal conformity assessment, especially for higher-risk products in Critical Class 1 or 2, which might require a third-party review.
In our training, we see that early work on secure boot, firmware hardening, and code audits pays off. It cuts down on last-minute panic and cost. As companies rethink how they build secure products, many are evaluating how AI changes software development workflows in areas like threat modeling, code review, and automated testing.
The shift toward the kind of security used in automotive or medical tech is happening, and it’s becoming mandatory.
FAQ
What does the Cyber Resilience Act mean for my digital products?
The Cyber Resilience Act sets clear cybersecurity requirements for products with digital elements sold in the European Union. If you manufacture or distribute digital products, including IoT devices and other connectable hardware, you must comply with CRA requirements.
These rules cover vulnerability management, vulnerability handling processes, regular security updates, and proper documentation, such as a Software Bill of Materials. The goal is to reduce cyber threats throughout the entire product life cycle.
Do small software developers need to follow CRA requirements?
Small software developers must comply with the EU Cyber Resilience Act if they place a product with digital elements on the European Union market. Open source software can also fall within scope when it is part of commercial digital products.
Developers are responsible for vulnerability reporting, fixing security flaws, and maintaining effective vulnerability management. In higher-risk cases, a conformity assessment by a notified body may be required before market access.
How does CE marking work under the EU Cyber Resilience Act?
CE marking confirms that a product with digital elements meets the cybersecurity requirements defined in Regulation 2024/2847. Before applying CE marking, manufacturers must complete a conformity assessment and prepare the EU Declaration of Conformity.
Some products require involvement from Conformity Assessment Bodies, depending on their classification under Annex III. Member States conduct market surveillance to verify compliance. Without proper Product Compliance documentation, digital products cannot be legally sold.
Will the Act affect IoT devices and smart devices already on the market?
The European Cyber Resilience Act applies to Internet of Things devices, smart devices, and other goods with digital elements placed on the European Union market. Manufacturers must provide timely security updates and address firmware vulnerabilities during the product life cycle.
If security flaws are discovered, companies must follow structured vulnerability handling and Vulnerability Reporting procedures. Products classified as Critical Class 1 or Critical Class 2 face stricter cybersecurity standards.
How does the CRA relate to other EU cybersecurity laws?
The EU Cyber Resilience Act works together with the NIS2 Directive and the EU Cybersecurity Act to strengthen cybersecurity standards across Member States. The NIS Directive focuses on essential services and public service infrastructures, while the CRA concentrates on digital products and connectable hardware.
The framework promotes cyber risk assessments, stronger supply chain controls, and alignment with technical standards developed by European Standardization Organizations.
EU Cyber Resilience Act Compliance: Act Before 2027 or Risk Market Access
The EU Cyber Resilience Act draws a clear line. You either build secure products from day one or you scramble later under pressure. Deadlines will arrive. Audits will happen. The only real choice is preparation. Secure coding, lifecycle security, and real accountability now will weigh far less than breaches, fines, and lost trust later.
Take action today. Join the hands-on Secure Coding Practices Bootcamp and train your team to ship safer code: https://securecodingpractices.com/bootcamp/#Join
References
- https://www.europarl.europa.eu/news/en/press-room/20240308IPR18991/cyber-resilience-act-meps-adopt-plans-to-boost-security-of-digital-products
- https://www.ibanet.org/raising-the-bar-on-cybersecurity-European-Cyber-Resilience-Act
