EU Cyber Resilience Act Summary is a major shift. It’s a 2024 law, Regulation 2024/2847, that covers almost every connected product sold in the EU.
Businesses must now design security in from the start, handle flaws properly, and keep pushing out security updates. The goal is to cut down risk and replace dozens of different national rules with one clear standard.
This changes the game for makers and developers. It’s not about paperwork. It’s a rebuild. Let’s look at what you need to do.
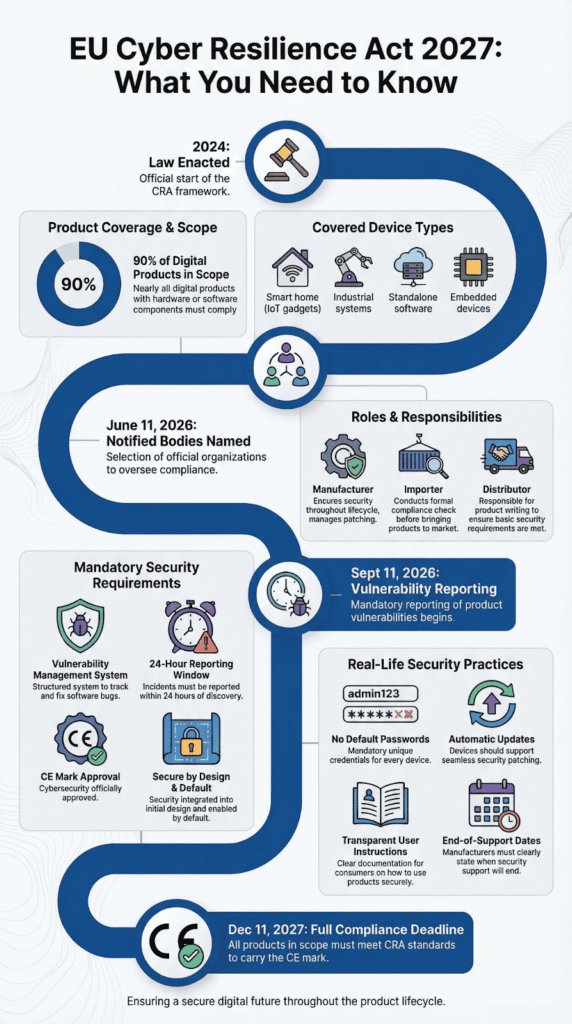
EU Cyber Resilience Act 2027: Requirements at a Glance
Key requirements EU firms must know:
- The law demands full lifecycle security for digital products in the EU. The hard deadline is December 11, 2027.
- Companies must have a formal vulnerability management system. Actively exploited flaws get a 24-hour reporting clock.
- The CE mark now means a product is cybersecure, meeting new rules beyond old safety checks.
What Is the EU Cyber Resilience Act?
The EU Cyber Resilience Act (CRA) is a new law. It creates mandatory cybersecurity rules for connected products, both hardware and software.
It covers everything from IoT gadgets to enterprise software. The goal is to make products “secure by design and by default.” Before the CRA, rules varied across EU countries. Now there’s a single, clear framework, and many teams first understand the regulatory shift when the Cyber Resilience Act is explained in practical product-security terms.
The European Commission says the law fills a gap:
“With the Cyber Resilience Act, we are filling a gap by completing the safety rules so that security by design applies to all products that reach EU consumers and users. The new rules require every interconnected product sold in the EU to be cybersecure.” – European Commission
It was prompted by major supply chain attacks like SolarWinds. The EU’s cybersecurity agency, ENISA, says such threats are growing.
The law aims to:
- Cut down on major cyber threats.
- Harmonize rules across Europe.
- Improve consumer information.
- Strengthen operational resilience.
This treats cybersecurity as a core safety issue, not just a compliance task.
Which Products and Companies Fall Under the CRA?

The CRA affects anyone putting a digital product on the EU market. This includes manufacturers, importers, and distributors, even for free products.
Based on official assessments, it covers about 90% of all digital goods. The term “product with digital elements” means any connected hardware or software. In our workshops, we’ve found that even internal tools that use external APIs can fall under it.
In Scope Products
- Consumer IoT devices, like smart baby monitors
- Industrial control systems
- General-purpose software
- Embedded systems (using platforms like QNX)
- Connectable hardware in public infrastructure
Excluded or Sector Specific Regimes
- Many medical devices (covered by other EU laws)
- Certain automotive and aviation systems
The CRA clearly splits responsibility.
| Actor | Their Job |
| Manufacturer | Handle security for the product’s whole life |
| Importer | Check it’s compliant before it’s sold |
| Distributor | Do their homework on what they’re selling |
Some say it’s like “building codes for digital products.” That’s a good way to put it. It forces security to be built in from the start, not bolted on later.
What Are the Key Cybersecurity Obligations for Manufacturers?
Credits: Cyen – Cybersecurity
Manufacturers face the strictest rules under the CRA. You can’t sell a product if it has known, exploitable security holes; those need to be fixed first. Once it’s on the market, you have to keep managing and patching vulnerabilities for the product’s entire supported lifespan.
The law requires meeting all essential cybersecurity requirements in Annex I. These focus on protecting data’s confidentiality, integrity, availability, and authenticity.
The European Parliament is clear: lifecycle security is now a legal duty. Products cannot have known flaws at launch, and they must get security updates for at least five years in most cases. Analysts at the World Economic Forum note that,
“The Cyber Resilience Act aims to enhance the security of hardware and software products by setting uniform standards across the EU… and obliges manufacturers to take security seriously throughout products’ lifecycles.” – World Economic Forum
From our training programs, we know secure coding is the best first step. When teams use threat modeling and check dependencies early, often supported by a hybrid coding approach that blends automated security tooling with disciplined developer practices, meeting these rules becomes part of the process, not a last-minute panic.
Key Duties Include
- Doing cyber risk assessments during design
- Setting secure defaults
- Using strong authentication and encryption when needed
- Having documented processes for handling vulnerabilities
- Creating a software bill of materials (SBOM)
ENISA says structured vulnerability handling is a core part of the CRA.
What doesThis Look Like in Real Life?
- No default passwords left on devices
- Automatic updates, when possible
- Clear instructions for users
- Announced end-of-support dates
We’ve helped teams build these controls. The biggest change is in mindset. Security has to be part of the initial design, not something you fix later.
What Are the CRA Vulnerability and Incident Reporting Deadlines?

The reporting deadlines are tight. If a manufacturer finds an actively exploited vulnerability, they must report it within 24 hours. A full, detailed notification is due within 72 hours.
All reports go through a central ENISA platform. This system works with the CSIRTs Network to share alerts across all 27 EU countries.
The official timeline is:
- 24 hours for an early warning
- 72 hours for the full notification
- 14 days for a final report after a fix
- 1 month for a final report on severe incidents
These rules start on September 11, 2026.
We run practice drills for these deadlines. The pressure is intense. Without a prepared incident response team and clear workflows, companies can easily miss a critical window.
This fits with requirements from the NIS2 Directive and other ICT third-party risk rules.
The key point is proof. Regulators want to see evidence of how you handle vulnerabilities. Online discussions in 2026 stressed that a policy document isn’t enough. You need to show your work.
That’s the real challenge.
How Does Conformity Assessment and CE Marking Work Under the CRA?
Before you can sell a product in the EU, it must pass a conformity assessment and get the CE mark. This mark shows the product meets all CRA rules.
For most standard-risk products, you can do an internal check yourself. Products with higher risks, listed in Annex III, need a review by an official third-party “notified body.”
Here’s how the two paths compare:
| Product Risk Level | Assessment Type |
| Standard | Internal conformity assessment procedure |
| Important or Critical | Third-party notified body evaluation |
Your technical paperwork must include:
- Records of your risk assessments
- Your procedures for handling vulnerabilities
- Evidence from security testing
- The official EU declaration of conformity
Market watchdogs in EU countries can investigate, demand fixes, and work together on cross-border checks.
We’ve seen that testing products early against EU standards makes the formal assessment much smoother. The most common holdup is missing or poor documentation.
Now, the CE mark tells buyers a product is cybersecure, not just physically safe. This changes how purchasing teams think about digital goods.
What Are the CRA Implementation Timelines?
The CRA is law now, but the final deadline for full compliance is December 11, 2027.
Here are the key dates to know:
- 2024: The law takes effect.
- June 11, 2026: Official “notified bodies” are named.
- September 11, 2026: Strict vulnerability reporting begins.
- December 11, 2027: Everything must be in place.
You have about three years to get ready. This gives businesses about three years to make big changes.
Our advice is to start now. Begin with secure architecture reviews and build secure coding into your process. Setting up systems for vulnerability management and software updates takes a long time to get right.
Teams that wait until 2026 will probably hit major roadblocks.
The CRA is more than a rulebook. It’s a new way of building digital products for the European market, and understanding the broader CRA overview and regulatory purpose helps teams see why security now sits at the center of product design.
FAQ
What products with digital elements must follow the Cyber Resilience Act?
The Cyber Resilience Act applies to most products with digital elements placed on the market in the European Union. This includes digital products such as IoT devices, smart home devices, baby monitors, connectable hardware, and certain medical devices.
Both hardware manufacturers and software developers must comply with the CRA requirements. In some situations, open-source software may also fall within scope. The regulation strengthens cybersecurity features throughout the entire product lifecycle.
How does CE marking work under the EU Cyber Resilience Act?
Under the EU Cyber Resilience Act, manufacturers must complete a conformity assessment procedure before affixing the CE marking to a product with digital elements. This process confirms that the product meets the essential cybersecurity requirements listed in Annex I.
Certain critical products require assessment by a notified body. After a successful evaluation, the manufacturer issues an EU declaration of conformity and prepares detailed technical documentation for market surveillance authorities.
What are the vulnerability handling requirements for software developers?
The CRA requirements establish clear vulnerability handling and vulnerability management obligations. Software developers must identify security flaws, assess cyber threats, and provide timely security updates and software updates.
They are required to report severe incidents to the relevant authorities and cooperate with a security incident response team when necessary. In some cases, a software bill of materials is required to improve supply chain transparency and strengthen operational resilience.
How does the European Commission enforce compliance across Member States?
The European Commission coordinates the enforcement of the European Cyber Resilience Act with Member States and market surveillance authorities. Authorities may review technical documentation, verify CE marking, and examine the conformity assessment procedure used by manufacturers.
Conformity assessment bodies are also subject to oversight. The European Union Agency for Cybersecurity supports implementation by contributing guidance and promoting harmonised European standards across the European Union.
How does the Cyber Resilience Act relate to the NIS2 Directive and DORA?
The Cyber Resilience Act works alongside the NIS2 Directive and the Digital Operational Resilience Act. Directive 2022/2556 and Regulation 2022/2554 focus on ICT third-party risk management and digital operational resilience testing for critical ICT third-party providers.
In contrast, the CRA establishes cybersecurity requirements for products with digital elements. Together, these laws strengthen protection against data breaches and online attacks across public service infrastructures and hospital databases in the European Union.
Preparing for Full EU Cyber Resilience Act Compliance by 2027
This law is not just about rules. It’s about trust. Every product you ship is a promise. A promise that it won’t break, leak data, or harm the people who use it. You may ask, “Can we handle this change?” The real question is, can you handle the cost of doing nothing?
Security starts with how you build. Train your team. Strengthen your code. Take the next step and join the Secure Coding Practices Bootcamp. Your customers are counting on you.
References
- https://ec.europa.eu/commission/presscorner/detail/en/ip_23_6168
- https://www.weforum.org/stories/2026/02/why-cyber-resilience-must-be-built-into-the-value-chain/
