Why Cyber Resilience Act Matters? The Cyber Resilience Act covers any product with a chip or some code sold in Europe, think smart fridges, apps, and industrial software. Starting in 2026, you have to report security issues.
By 2027, your products must be fully compliant. This isn’t optional anymore; it’s mandatory for manufacturers and developers. If you’re in tech, this changes your game. The deadline seems far off, but preparation takes time. Let’s get into the details of what you need to do next.
Why the Cyber Resilience Act Matters for EU Firms at a Glance
Key reasons CRA impacts EU firms:
- The CRA makes cybersecurity rules for digital products legally binding across the EU.
- Fines for breaking the rules can reach €15 million or 2.5% of your worldwide revenue.
- Getting ahead with secure coding and managing your software bill of materials (SBOM) cuts your risk, cost, and audit headaches later.
What Is the Cyber Resilience Act?
The Cyber Resilience Act (CRA) is the EU’s response to weak security in connected products. It mandates that any digital product sold in Europe, from baby monitors to industrial software, must be secure by design. Many teams still ask what the EU Cyber Resilience Act actually requires when they first begin preparing their compliance plans.
As the European Cyber Resilience Act Information Portal states:
“Digital hardware and software products constitute one of the main avenues for successful cyberattacks. In a connected environment, a cybersecurity incident in one product can affect an entire organisation or a whole supply chain, often propagating across the borders of the internal market within a matter of minutes.” – European Cyber Resilience Act
We’ve seen how a single unsafe product can break a whole system. The CRA fixes three core problems:
- Security isn’t built in from the start.
- Products don’t get critical updates.
- Companies are slow to report and fix holes.
The CRA works with other EU rules, like NIS2, to build a safer market. Its goal is simple: make strong security mandatory, not optional.
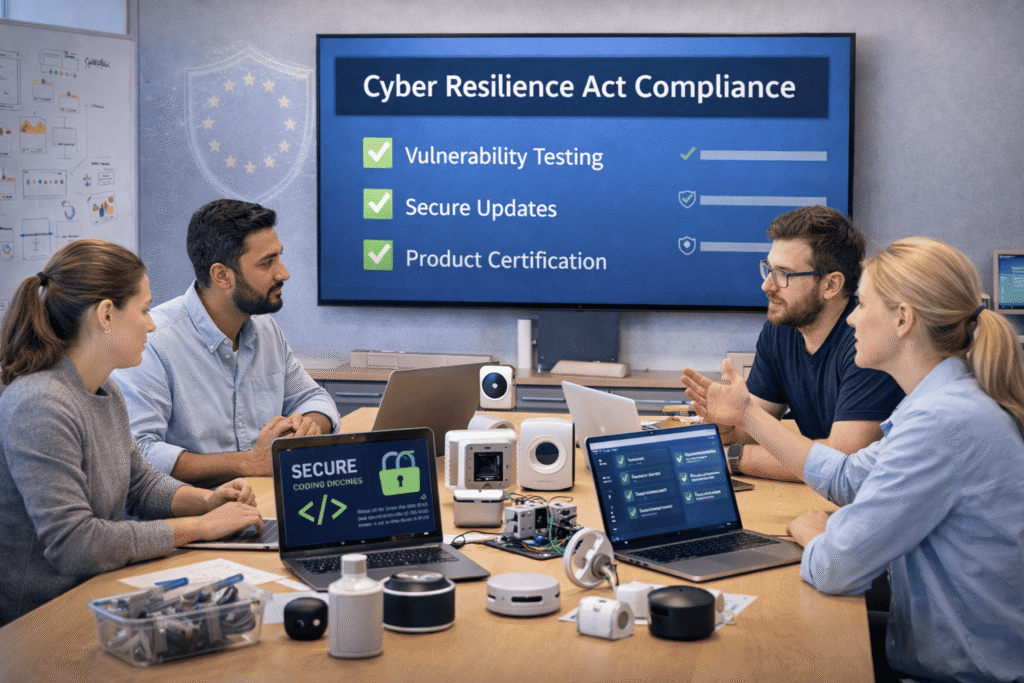
How the CRA Makes Cybersecurity Mandatory
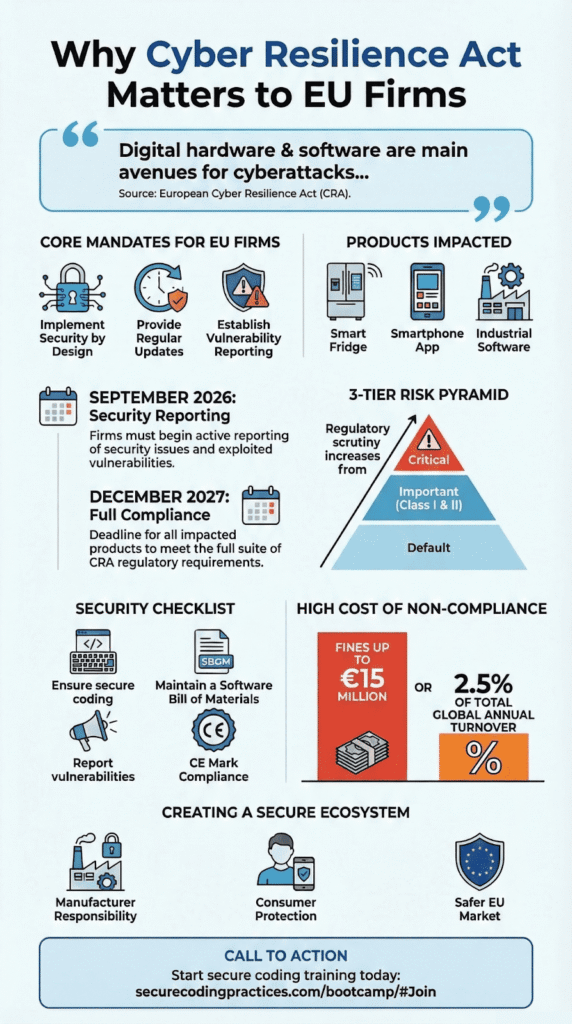
For years, the CE mark on a product just meant it was physically safe. The CRA changes that. Now, to get that CE mark and sell in Europe, a product must also meet strict cybersecurity rules. This turns what was often a voluntary best practice into a legal duty.
Manufacturers have to prove they are building security in. Many teams now rely on secure coding practices to ensure vulnerabilities are reduced early in development. They must also provide automatic updates and have a clear plan for finding and reporting bugs.
Actively exploited vulnerabilities must be reported starting September 2026. Actively exploited vulnerabilities must be reported starting September 2026.
| Area | Before CRA | After CRA |
| Security updates | Often optional | Mandatory lifecycle support |
| Vulnerability reporting | Inconsistent | Required and time-bound |
| CE mark | Safety focused | Includes cybersecurity compliance |
In our training, we stress that adding security later is hard. It’s much easier to build it in from day one, even if it feels slower. The CRA now makes that early work a legal requirement.
CRA Product Classifications and Risk Tiers
Credits: Codific
The CRA groups products by risk. A smart light bulb won’t face the same rules as a password manager. The more critical the function or connection, the stricter the requirements. Products handling sensitive data or key network functions get the toughest third-party checks.
The groups are:
- Default: Companies can check their own work.
- Important (Class I & II): Need stricter paperwork and checks.
- Critical: Must be reviewed and approved by an official outside body.
Products in the higher groups need a stamp of approval from these official bodies before they can get a CE mark. This rule starts for new products in December 2027.
We tell our teams to figure out their product’s risk level early. If your device manages logins or backups, it will likely be in a higher tier. Doing Threat modelling upfront saves huge headaches later.
Why the Cyber Resilience Act Matters for Businesses and Startups
This law makes cybersecurity a top business concern. The fines are serious: up to €15 million or 2.5 percent of a company’s worldwide yearly sales. Products can also be banned from the EU market.
Businesses now have new jobs, like:
- Making a list of all the software parts they use (an SBOM).
- Checking the security of parts from other companies.
- Having a plan for security incidents.
We’ve worked with startups that built a cool device but forgot to plan for five years of security updates. Under the CRA, that’s a major problem. The device could be recalled.
But following the rules isn’t just about avoiding fines. It builds trust. Big companies now ask for proof of security tests and recovery plans before they buy. Getting compliant can actually help you win business.
Open Source, Developers, and Supply Chain Reality
Most software today is built with open source code. That’s a strength, but it’s also a risk. The CRA now asks companies to know and document every part they use, including these free libraries. Developers worry about getting blamed for a bug in someone else’s code.
The main headaches are:
- Creating and managing a complete software parts list (an SBOM).
- Checking old, inherited code for problems.
- Unclear rules on how fast to fix reported bugs.
From our bootcamp work, we know that starting with Secure Coding Practices makes this easier. Teams also reduce maintenance overhead when they automate tedious refactoring tasks with AI, especially when large legacy codebases need security improvements before CRA compliance checks.
Using tools like CycloneDX to build an SBOM from the beginning turns a future audit from a panic into a simple check. Automated scanning and clear response plans protect developers and make the whole software supply chain safer to use.
Consumer and Societal Impact of the Cyber Resilience Act
For buyers, this law means the smart products you buy should be safer. Your new smartwatch or thermostat now comes with a legal duty to fix security flaws and provide updates. This matters because many big ransomware attacks start by hacking a single weak gadget. Stronger security protects everything connected to these devices, from hospitals to local shops.
The European Commission’s digital strategy guidance states:
“With the Cyber Resilience Act, the Commission supports the effective application of the Act. From baby monitors to smart watches, digital elements are part of our daily lives, and we will make sure all digital products on the EU market are safe from cyber threats.” – European Commission
The benefits are clear:
- Clear information on product support periods.
- Fewer preventable data leaks from gadgets.
- Required security updates.
The law’s effect is wider. It sets a new global standard. Any company wanting to sell digital products in Europe must build to these stricter rules. This pushes everyone to make better products.
How to Prepare for CRA Compliance Before December 2027
Don’t wait for the deadline. Start your preparation now. Based on our work with developers, here are the four steps that actually work.
First, classify your product. Figure out if it’s Default, Important, or Critical under the CRA rules. This decides how tough the checks will be.
Second, build your software bill of materials (SBOM). List every piece of software and library inside your product. Keep this list updated with every new release.
Third, build security in from the start. Do threat modeling early. Make sure you can send secure updates to devices already in customers’ hands.
Fourth, set up your reporting engine. Have a clear, fast plan for when a serious bug is found. Who gets told internally in 24 hours? Who talks to the authorities?
A simple checklist helps:
- Know your CE marking path.
- Your SBOM is ready.
- Vulnerability management is documented.
- Security updates work.
- Your EU Declaration of Conformity is drafted.
In our experience, the biggest delays come from missing paperwork, not technical flaws. Starting early turns a scramble into a manageable plan.
FAQ
What does the Cyber Resilience Act require from businesses?
The Cyber Resilience Act sets mandatory cybersecurity requirements for products with digital elements sold in the European Union. Businesses must conduct risk assessments, perform vulnerability analysis, and implement structured vulnerability management.
They must complete conformity assessment procedures and prepare technical documentation for CE marking and the EU Declaration of Conformity. The regulation also requires secure by design practices throughout the entire Product Lifecycle.
How will CRA requirements affect my connected devices?
CRA requirements apply to connected devices such as IoT devices, smart home devices, baby monitors, and industrial machines. Manufacturers must ensure security by design, implement security mechanisms, and provide timely security updates.
They must also assess Supply chain security, manage third-party components, and document Software Bill of Materials information. These steps reduce data breaches and protect digital products against evolving cyber threats.
Do open source software and third-party components fall under the CRA?
Open source software and third-party components fall under the EU Cyber Resilience Act when integrated into a product with digital elements. Companies must track these components through SBOM Management and conduct proper vulnerability handling.
The European Commission requires clear reporting obligations and strong information security controls. If open source software affects overall product security, it must meet the same cybersecurity requirements.
What steps help ensure CE marking under the EU Cyber Resilience Act?
To obtain the CE mark, companies must complete a conformity assessment based on Class I or Class II classification under Annex I. In certain cases, Notified Conformity Assessment Bodies must review the product.
Organizations may need to align with security standards such as ISO/IEC 27001, ETSI EN 303 645, IEC 62443, or Common Criteria. Proper documentation supports the EU Declaration of Conformity and market entry regulation compliance.
How does the Cyber Resilience Act improve incident response and data security?
The EU Cyber Resilience Act strengthens Incident Response, Disaster Recovery, and Business Continuity obligations. Companies must establish a security incident response team and meet formal incident reporting timelines aligned with the NIS2 Directive.
They must implement Data Security controls, including Multi-Factor Authentication and regular security updates. These cybersecurity requirements reduce cyber threats and improve protection across the Supply chain.
Why the Cyber Resilience Act Matters for EU Firms Right Now
The Cyber Resilience Act is not just a set of rules on paper. It is a clear line. Every device you build can make Europe safer, or riskier. December 2027 sounds far away, but it is not. Waiting will cost more than starting. So ask yourself: will your product just work, or will it protect?
If you’re ready to act, start here. Learn the skills and practice them. Build safer code from day one. Europe’s digital future depends on what you choose to do next.
References
- https://www.european-cyber-resilience-act.com/
- https://digital-strategy.ec.europa.eu/en/news/commission-publishes-feedback-draft-guidance-assist-companies-applying-cyber-resilience-act
