
In the EU, software security is no longer something added at the end. It must be included from the beginning of design and development. This is called security by design. In our experience at Secure Coding Practices, this approach helps developers reduce vulnerabilities early and build more reliable systems.
It also aligns development work with strict EU regulations. This article explains how it works in real projects, what rules influence it, and how teams can apply it in practice. Keep Reading
Key Insight Software Security by Design EU
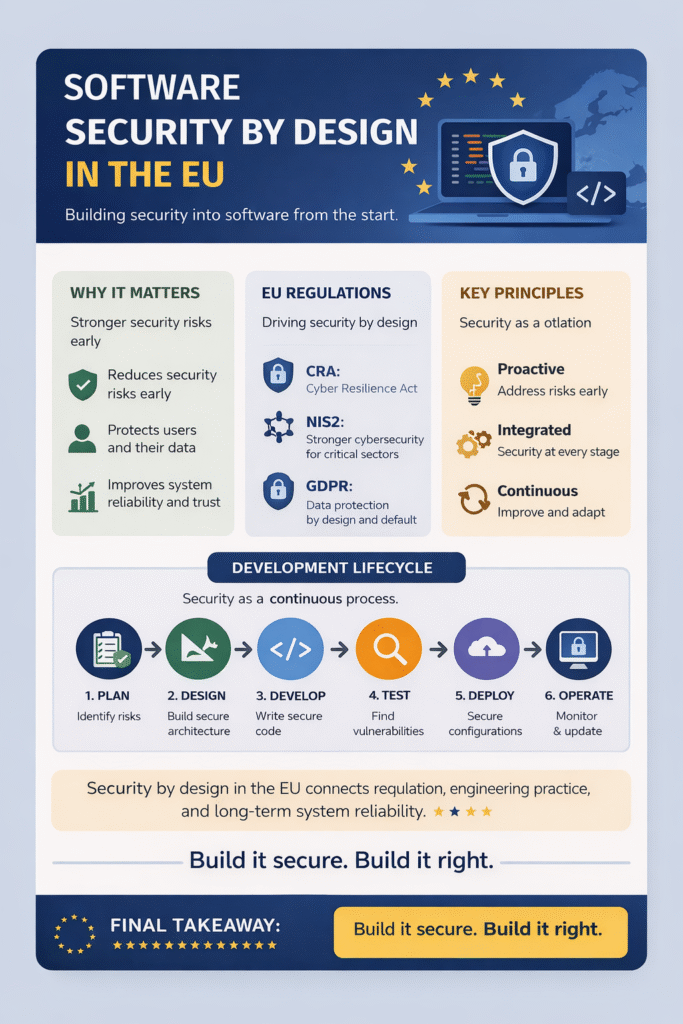
Security by design is now a core expectation in EU software development, and these are the key takeaways to understand:
- Security must be built into software from the start
- EU regulations like CRA, NIS2, and GDPR enforce secure design
- Real development requires continuous security practices
What Security by Design Means in Practice
Security by design means we build systems to prevent vulnerabilities, not just fix them later. Instead of asking how to patch issues after release, we ask how to design systems so issues are less likely to happen at all.
“Secure by design … mandates that security be incorporated into systems from the outset rather than as an afterthought.” – Wikipedia
In real development work, this includes secure architecture, input validation, strong authentication, and careful API design. We also integrate security into coding standards and deployment workflows. From our hands-on experience, early design decisions have the biggest impact on long-term security and maintenance cost.
Why the EU Pushes This Approach
Credits: Product Security Podcast
The EU focuses on security by design to meet modern secure coding regulatory expectations in the EU, especially as digital systems now support critical infrastructure like healthcare, finance, and transportation. A single vulnerability can have wide real-world impact.
In practice, we often see teams underestimate how strict this shift is until they work with compliance requirements directly. The main goal is not just preventing attacks, but ensuring resilience and accountability across the entire software lifecycle.
Key EU Regulations Supporting Security by Design
| Regulation | Focus | Key Security Requirement |
| Cyber Resilience Act | Product security lifecycle | Built-in security, vulnerability handling, updates |
| NIS2 Directive | Critical infrastructure security | Risk management, incident reporting, supply chain security |
| GDPR | Data protection | Privacy by design, encryption, access control |
These frameworks collectively push organizations toward integrating security from the start, not as an afterthought.
Core Principles We Apply in Real Development Work
In our development and training experience at Secure Coding Practices, we consistently apply a few core principles. We reduce attack surface by keeping systems minimal and focused. We enforce secure defaults so systems are protected immediately after deployment.
We apply least privilege access to limit unnecessary permissions. Security testing is continuous, not a one-time step. We also monitor dependencies closely because third-party libraries often introduce hidden risks. Finally, we design systems assuming incidents can happen, so detection and response are always built in.
- Reduce attack surface through minimal system design
- Enforce secure defaults from deployment
- Apply least privilege access control
- Run continuous security testing (not one-time)
- Monitor third-party dependencies regularly
- Design with incident detection and response in mind
How Security by Design Feels in Real Teams
In real teams, navigating the legal and regulatory context initially feels like it slows development because more thinking is required at the start. Developers need to consider threats, permissions, and validation earlier than usual. However, after a few iterations, teams usually notice fewer critical bugs later in the cycle and less rework.
Systems become more predictable and easier to maintain. In our experience, security stops being a separate task and becomes part of normal engineering thinking.
- Early stage feels slower due to added security considerations
- More focus on threats, permissions, and validation
- Fewer critical bugs appear later in development
- Less rework during testing and deployment
- Systems become more stable and predictable
- Security becomes part of daily engineering mindset
Where Secure Coding Practices Fits In
Many developers understand security concepts but struggle to apply them in real code. This is where structured, hands-on practice becomes important.
“We posit that security considerations must take center-stage with the safety considerations to realize secure-by-construction systems.” – ARXIV
At Secure Coding Practices, we focus on applying secure coding principles directly in realistic scenarios. Developers learn how input validation, authentication design, and API security work in practice, not just theory.
Over time, this helps teams navigate the secure coding EU regulatory context naturally, meeting requirements like CRA and NIS2 without treating compliance as a separate burden.
Common Challenges Teams Face
Teams often struggle with legacy systems that were not designed securely from the start. Tight deadlines also make it difficult to prioritize security during early development stages. Another common issue is lack of security expertise within development teams.
From experience, the biggest challenge is consistency. Security by design is not a single task but a continuous habit across design, coding, and deployment. Without consistency, even good practices lose their impact over time.
The Direction of Software Security in the EU
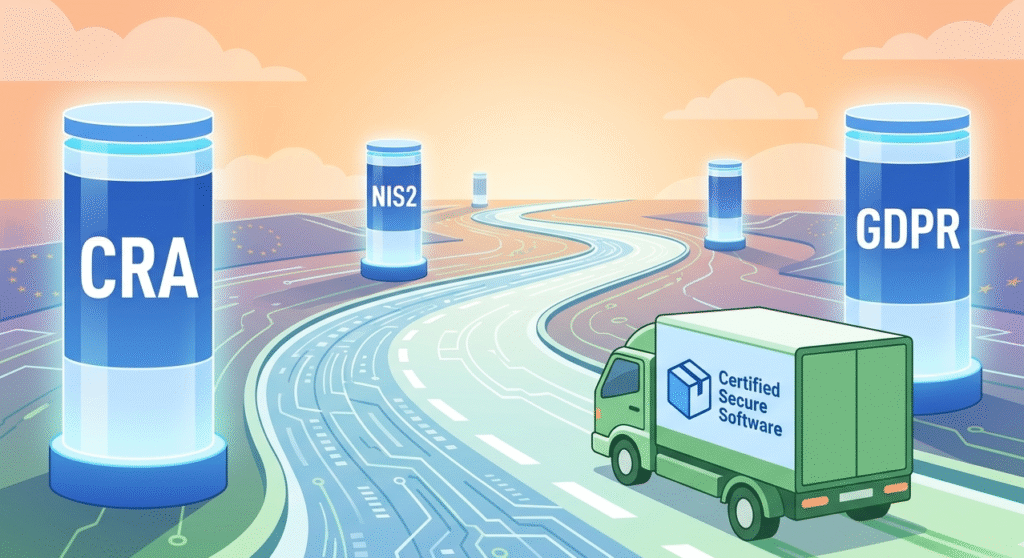
The EU is moving toward stricter enforcement of secure development practices across all software products. Security is becoming a baseline requirement rather than a competitive advantage.
We expect stronger focus on secure supply chains, continuous vulnerability management, and formal security validation in development pipelines. This means security decisions will increasingly shape system design from the very beginning of projects.
FAQ
What does software security by design EU mean in real development?
Software security by design in the EU means building security into software from the start of development. It is not treated as an extra feature added later. Developers must consider risks during planning, coding, and deployment. This approach helps reduce vulnerabilities early and ensures systems meet EU expectations for safer, more reliable digital products.
How do EU regulations affect software security by design?
EU regulations like CRA, NIS2, and GDPR push organizations to include security in every stage of software development. They require risk management, data protection, and secure system design.
This means developers must think about security during architecture and coding, not just testing. It also increases responsibility for maintaining secure systems after release.
What skills are needed for secure software design in EU projects?
Developers need practical skills like secure coding, input validation, authentication design, and understanding system architecture. They also need awareness of common vulnerabilities and how to prevent them. In EU projects, it is important to think about security early and continuously, not just fix issues after deployment or during final testing stages.
Why is security by design difficult for development teams?
It is often difficult because teams face tight deadlines, legacy systems, and limited security expertise. Many developers are trained to focus on features first, not risks. Changing this mindset takes time. Consistency is also a challenge since security must be applied across every stage of development, not just once during testing.
Final Thoughts on Software Security by Design in the EU
Security by design in the EU is a fundamental shift in how software is built. It connects regulation, engineering practice, and long-term system reliability. From our experience at Secure Coding Practices, the most effective teams treat security as part of everyday development rather than an external requirement.
To strengthen these skills in real-world development, explore our Secure Coding Practices Bootcamp.
References
- https://en.wikipedia.org/wiki/Secure_by_design
- https://arxiv.org/abs/2202.06677

