
The Cyber Resilience Act (CRA) is changing how software is built in the EU. Security is no longer something added at the end, but something that must be planned from the beginning. From our work with development teams at Secure Coding Practices, we often see that early security thinking reduces bugs and rework later.
This article explains what security by design CRA requirements means and how developers can apply it in real projects. Keep reading to understand the key requirements and practical steps.
Key Insight: CRA Security by Design in Practice
Security by design under CRA is now a baseline expectation in EU software development.
- CRA requires security to be built into software from the design stage
- Developers must apply security across the full development lifecycle
- Stronger early design decisions reduce vulnerabilities and long-term cost
What Security by Design Means Under CRA
Security by design under CRA means we design systems to prevent security issues instead of reacting to them. In real projects, we see developers shift from feature-first thinking to risk-aware design, ensuring that software security by design EU standards are met from the very first line of code.
“Security must be incorporated into systems from the outset rather than as an afterthought.” – Wikipedia
- Security is planned during architecture, not after deployment
- Systems are designed to reduce attack surfaces
- Secure defaults are required by design
From a development perspective, this approach feels slower initially but becomes more stable over time.
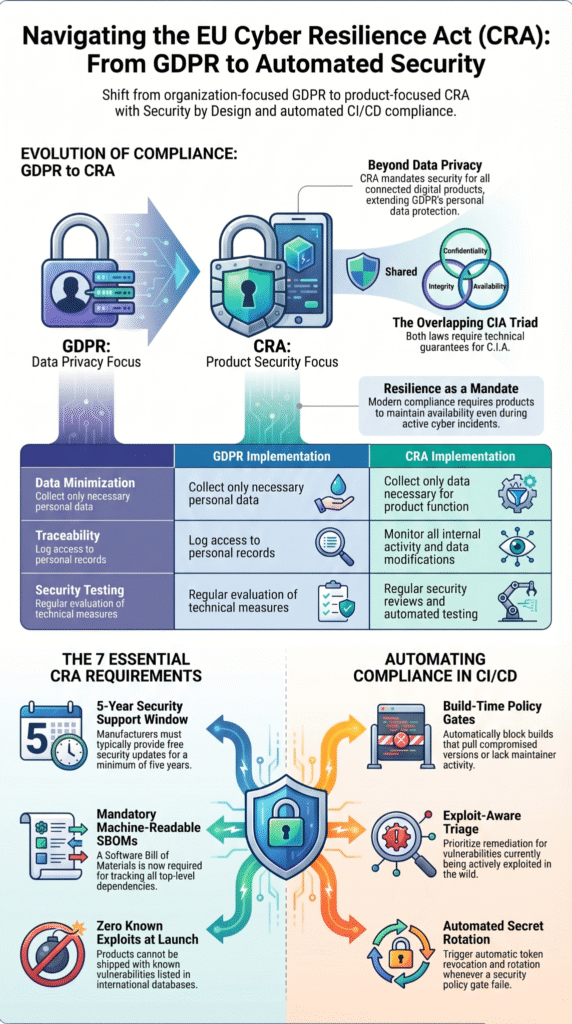
Core CRA Security Requirements
Credits: Hogan Lovells
CRA defines clear expectations for product security across the lifecycle. Understanding the broader legal and regulatory context is essential, as these requirements often reshape how engineering workflows are structured to maintain compliance.
| Area | CRA Expectation | Practical Impact |
| Secure development | Security integrated in SDLC | Earlier threat modeling |
| Vulnerability handling | Timely fixes + reporting | Continuous patching |
| Secure defaults | Safe configuration by default | Fewer misconfigurations |
We often see teams adjusting pipelines to include security checks earlier, especially during build and deployment stages.
How CRA Changes Real Development Practice
In practice, CRA pushes security deeper into daily development work. We experience this shift directly in projects we support through Secure Coding Practices. Developers no longer treat security as a separate audit phase.
“Secure by design is about embedding privacy and security into enterprise architecture and organisational culture.” – Sciencedirect
- Security checks are part of coding workflow
- Code reviews include vulnerability thinking
- Dependency risks are continuously monitored
This change can feel heavy at first, especially for teams used to fast release cycles. However, over time, systems become easier to maintain and production issues decrease significantly.
Practical Steps to Meet CRA Requirements
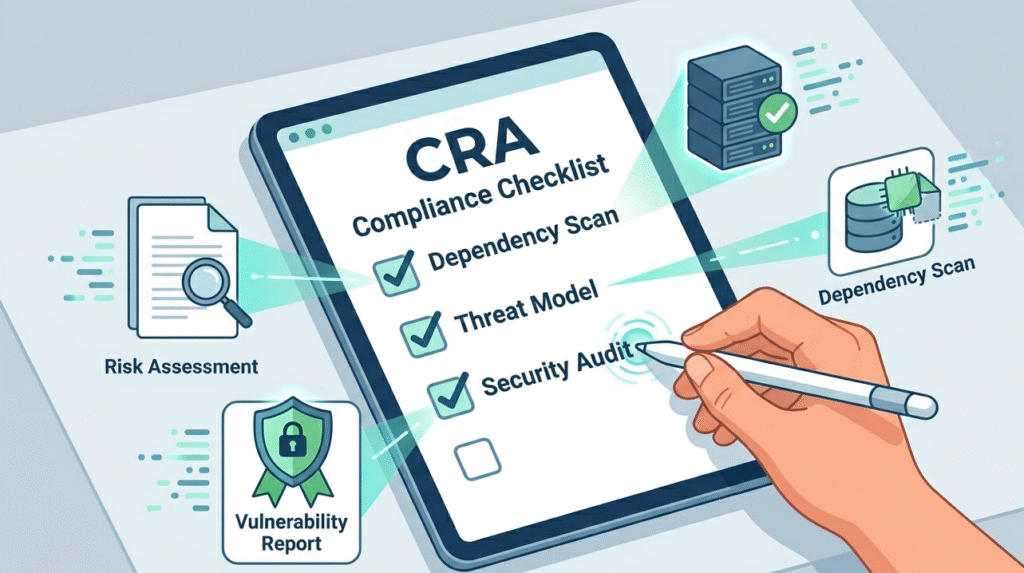
To align with CRA, we apply practical and repeatable steps in real development environments. These steps are rooted in the secure coding EU regulatory context, moving beyond theory into hands-on implementation that secures the software supply chain.
- Conduct threat modeling before development starts
- Enforce secure coding standards (input, auth, access control)
- Monitor third-party libraries continuously
- Build logging and incident detection early
- Automate security testing in CI/CD pipelines
At Secure Coding Practices, we often guide teams through these steps so security becomes part of routine engineering work, not a separate burden.
FAQ
What is security by design under CRA requirements in software development?
Security by design under CRA means security is built into software from the start, not added later. It focuses on preventing vulnerabilities during architecture, coding, and deployment. In practice, developers must think about risks early and design systems that are secure by default.
This approach reduces long-term security issues and improves overall system resilience across the entire development lifecycle.
How do CRA requirements change security by design in real projects?
CRA requirements make security a legal obligation in development. Teams must include risk assessment, vulnerability management, and secure defaults in every stage. In real projects, this changes how developers plan features, write code, and test systems.
Security becomes part of daily workflows instead of a separate step, leading to more consistent and predictable secure software delivery.
What skills are needed to meet security by design CRA requirements?
Developers need secure coding skills, threat modeling knowledge, and understanding of common vulnerabilities. They must also know how to apply authentication, authorization, and input validation correctly.
In CRA-based projects, continuous learning is important because security practices evolve. Teams benefit from practical experience applying security in real development rather than only theoretical knowledge or late-stage testing.
Why is secure development lifecycle important for CRA compliance?
Secure development lifecycle is important because CRA requires security at every stage of software creation. It ensures risks are identified early and managed continuously. This includes planning, design, coding, testing, and maintenance.
Without a structured lifecycle, vulnerabilities can be missed. A strong lifecycle approach helps teams stay consistent, reduce errors, and meet regulatory expectations more effectively.
Final Insight
CRA security by design requirements fundamentally change how software is engineered in the EU. It requires developers to think about security from architecture to deployment, not just at the end of testing.
From our experience at Secure Coding Practices, teams that adopt this approach early build systems that are easier to maintain, more resilient, and better aligned with regulatory expectations. To strengthen these skills in practice, join our hands-on Secure Coding Practices Bootcamp
References
- https://en.wikipedia.org/wiki/Secure_by_design
- https://www.sciencedirect.com/science/article/pii/S1353485820300957

