Open source obligations Cyber Resilience Act are no longer optional, they’re foundational to software security and compliance. We’ve seen teams underestimate how deeply open source components impact their risk posture until audits expose gaps.
This regulation changes that reality by enforcing accountability across the supply chain. Whether you build, integrate, or distribute software, understanding your obligations is critical. Keep reading to uncover what this means in practice and how to prepare effectively.
Key Insights: Open Source Obligations Cyber Resilience Act
Open source is powerful, but under the Cyber Resilience Act, it comes with clear responsibilities.
- Open source components must be documented and traceable
- Security vulnerabilities must be actively managed and disclosed
- Compliance requires structured technical documentation
Why Open Source Obligations Matter More Than Ever
We’ve worked with teams who relied heavily on open source libraries without fully tracking dependencies. That approach no longer works. The Cyber Resilience Act introduces a shift: organizations are now accountable for the security of all components, even those they didn’t build.
From our experience, the biggest challenge isn’t adopting open source, it’s managing it responsibly. Developers often move fast, but compliance requires visibility, governance, and discipline.
“Open-source software is software with source code that anyone can inspect, modify, and enhance.” – Wikipedia
This openness is powerful, but it also means vulnerabilities can propagate quickly if not managed properly.
Core Open Source Obligations Under the Cyber Resilience Act
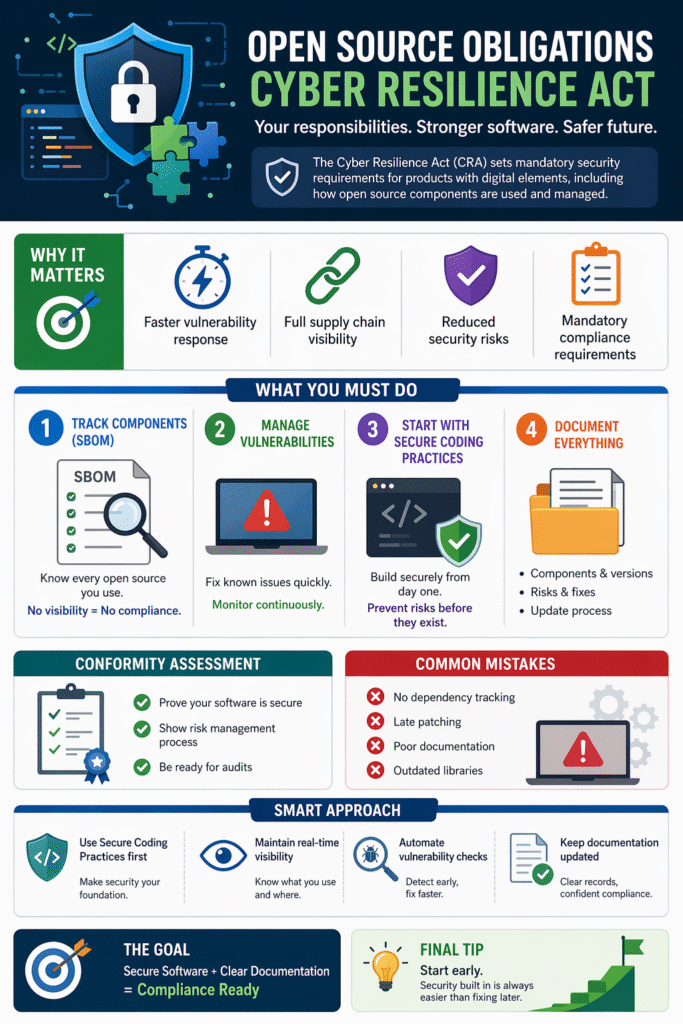
Credits: Somco Software
Organizations must rethink how they handle open source across the entire lifecycle.
1. Software Bill of Materials (SBOM)
You need a clear inventory of all open source components. We’ve found that teams without SBOMs struggle the most during audits. Without visibility, risk management becomes guesswork.
2. Vulnerability Management
It’s not enough to use secure components, you must continuously monitor and patch them. Known vulnerabilities must be addressed promptly, or they become compliance risks.
3. Secure Coding Practices First
We always prioritize Secure Coding Practices as the foundation. When we embed secure coding early, we reduce the likelihood of introducing vulnerabilities through integrations. This approach doesn’t just support compliance, it simplifies everything that follows.
4. Documentation and Traceability
Every component must be documented, including its origin, version, and known risks. This feeds directly into compliance reporting and audits.
Technical Documentation Requirements
The Cyber Resilience Act requires structured, accessible documentation. In practice, this is where many organizations struggle.
We’ve seen documentation treated as an afterthought, until regulators demand it.
Key elements include:
- Design and architecture overview
- Dependency mapping
- Security controls and mitigations
- Update and patching processes
“Software documentation is written text or illustration that accompanies computer software or is embedded in the source code.” – Wikipedia
Strong documentation isn’t just for compliance, it improves internal alignment and reduces operational friction.
Conformity Assessment: What It Means for Open Source Use
Depending on the criticality of your product, you may need a conformity assessment. This evaluates whether your software meets security and compliance standards.
From our experience, teams often underestimate this step. They assume open source equals “pre-vetted,” but regulators don’t see it that way. Responsibility still sits with the organization distributing the software.
This means:
- Validating security of dependencies
- Demonstrating risk management processes
- Providing evidence of ongoing monitoring
Common Challenges We See in Practice
Across multiple projects, a few patterns repeat:
- Lack of centralized dependency tracking
- Delayed vulnerability patching
- Inconsistent documentation standards
- Over-reliance on outdated libraries
We’ve learned that solving these issues early is far easier than retrofitting compliance later.
FAQ
Do open source components automatically comply with the Cyber Resilience Act?
No, they don’t. Even if an open source component is widely used or maintained, the responsibility for compliance lies with the organization using it. You must ensure proper documentation, vulnerability management, and integration security. This means validating each component within your own context rather than assuming external trust is sufficient.
What is the biggest risk of using open source under this regulation?
The biggest risk is lack of visibility. Without a clear inventory of components and their vulnerabilities, organizations cannot respond effectively to security issues. This becomes a compliance failure when regulators require proof of risk management and traceability.
How often should open source components be updated?
Updates should not follow a fixed schedule but rather a risk-based approach. Critical vulnerabilities should be patched immediately, while less severe issues can follow a structured update cycle. Continuous monitoring tools and processes are essential to ensure timely responses.
How do Secure Coding Practices support compliance?
Secure Coding Practices reduce the likelihood of introducing vulnerabilities during development and integration. By embedding security into coding standards, teams can proactively prevent issues rather than reacting later. This aligns directly with the Cyber Resilience Act’s focus on risk reduction and lifecycle security.
Open Source Obligations Cyber Resilience Act in Practice
Compliance with the Cyber Resilience Act requires structured action, not just reactive fixes. Organizations succeed by embedding Secure Coding Practices early to reduce friction and risk. By prioritizing visibility and proactive documentation, teams transform regulatory requirements into a strategic security advantage.
Ready to lead with resilience? The Secure Coding Practices Bootcamp offers hands-on training in OWASP essentials and safe dependency management, helping your team ship secure code from day one. Secure Coding Practice: Join the Bootcamp
References
- https://en.wikipedia.org/wiki/Open-source_software
- https://en.wikipedia.org/wiki/Software_documentation
