If you sell a connected product in Europe, when Cyber Resilience Act applies to you. The law, Regulation (EU) 2024/2847, took effect on December 10, 2024. It changes how digital products are built and supported. It covers nearly any product with a chip that connects to a network, from a smart thermostat to enterprise software.
You must be fully compliant by the end of 2027. Fines for non-compliance can go as high as €15 million. Time is short. Read on to see where you stand and what to do.
When the Cyber Resilience Act Applies: Key Points
Here’s a quick overview of when the Cyber Resilience Act applies to your products:
- The CRA applies broadly to any hardware or software with digital elements sold in the EU, regardless of where your company is based.
- Critical compliance deadlines are staggered, with vulnerability reporting starting in September 2026 and full enforcement in December 2027.
- Your obligations are determined by a product’s risk classification, ranging from self-assessment for default items to third-party audits for critical ones.
The Core Question: What is a “Product with Digital Elements”?
So, what counts as a “product with digital elements”? The law’s definition is broad on purpose. It’s not just cybersecurity software. If your product connects to a device or network, directly or indirectly, it’s almost certainly included. Think IoT gadgets, factory sensors, server OS, or even a password manager app.
This is a horizontal rule that touches nearly every sector, defining the specific scope and applicability of these security mandates across the digital landscape.
Understanding who must comply with the Cyber Resilience Act starts with the manufacturer, who carries the main responsibility. That’s us, if we develop a product under our name or trademark, or if we modify an existing one substantially.
Importers and distributors have duties, but the core legal burden for cybersecurity compliance sits with the maker. Your company’s location is irrelevant. Selling into the EU market means you must follow these rules.
Products That Are Exempt (And Common Misconceptions)
Credits: Tributech
The scope of the EU Cyber Resilience Act doesn’t cover every digital product. It carves out clear exemptions for specific categories. Medical devices and cars, for instance, follow their own, stricter laws. Products made only for the military or national security are also out.
The trickiest exemption is for open-source software. The law excludes free, open-source software developed outside of commercial activity. This means a hobbyist posting code online is fine. But if your business uses that code in a product you sell, or if an open-source project charges for support, that commercial link brings your final product under the CRA’s rules.
Don’t assume your old products are safe. They aren’t. If you’re still manufacturing and selling a device after December 11, 2027, it must comply. This is causing real headaches in sectors like industrial manufacturing, where equipment is often used for 10 or 20 years.
Key Exemptions:
- Medical devices
- Vehicles
- Military/security products
- Non-commercial open-source software
Not Exempt:
- Legacy products sold after 2027
The Compliance Clock: Critical Dates You Cannot Miss
The CRA timeline is phased, giving everyone time to prepare, but the deadlines are strict. When the regulation entered into force on December 10, 2024, the transition period officially began. From September 10, 2026, manufacturers must report any actively exploited vulnerability or severe incident within 24 hours to ENISA and national CSIRTs.
By December 10, 2027, every product with digital elements must be fully compliant, complete with CE marking, technical documentation, and a Software Bill of Materials. At our bootcamp, we emphasize planning early; the key is to treat these milestones as checkpoints for structured compliance rather than last-minute panic.
| Milestone | Date | What It Means For You |
| Law In Force | December 10, 2024 | Transition period begins; start your compliance prep now. |
| Reporting Obligations Start | September 10, 2026 | Must report severe incidents/exploited vulnerabilities within 24 hours. |
| Full Enforcement | December 10, 2027 | All new products must be fully compliant with CRA to be sold in the EU. |
Categorizing Your Product’s Risk Level
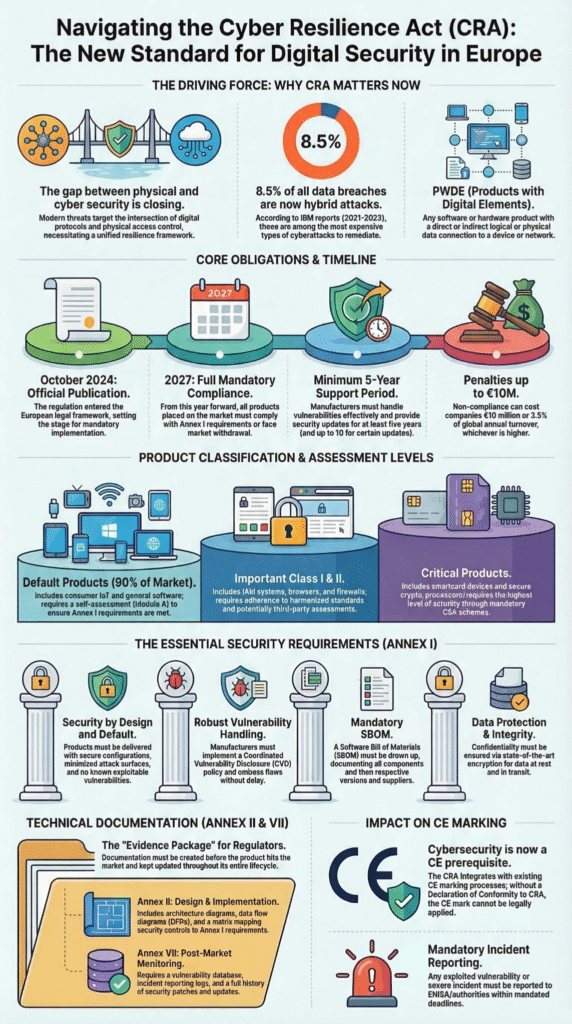
Not all products carry the same level of risk. We guide teams to classify products into four categories: Default, Important Class I, Important Class II, and Critical. Most consumer IoT devices fall under Default and allow self-assessment. Important products like VPNs and browsers may require notified body involvement.
“The CRA will obligate all products with digital elements, including their remote data processing, put on the European market to follow this regulation. … its horizontal nature gives it a big scope, including a wide set of hardware and software, but excluding medical devices, cars and other product types with their own safety and security rules.” – OpenSSF
Critical products, such as HSMs or smart meter gateways, need full third-party audits. By assessing risk early, our students understand how to allocate resources and ensure each product meets the CRA’s requirements efficiently.
Building a Compliant Product: From Design to Disposal
Security must be integrated from day one. At our bootcamp, we teach “secure by design”: embedding threat modeling, peer review, and dynamic testing throughout development. Creating a Software Bill of Materials (SBOM) is essential, especially for open-source components.
“The regulation applies to any company placing products with digital elements on the EU market, regardless of where the company is headquartered. … The regulation extends responsibility across the supply chain. Manufacturers will require detailed documentation such as a Software Bill of Materials (SBOM) from third-party component suppliers.” – ICS
We also stress long-term support: free security updates for at least five years and clear public declarations of support. A formal vulnerability-handling process, with designated contacts and coordinated patching, is critical. By practicing this workflow in our labs, developers see firsthand how proactive security reduces risk and prepares products for CRA compliance.
Navigating the Conformity Assessment
Conformity assessment proves compliance. Default products follow Module A: self-assessment with documentation and an EU Declaration of Conformity. Important and Critical products require notified bodies, which audit technical files and may inspect production lines.
Following harmonized standards like ETSI EN 303 645 can simplify the process and create a presumption of conformity. In our bootcamp, we simulate audits so participants understand the practical steps, from documentation preparation to third-party review, ensuring they’re ready for real-world scrutiny.
Your Practical Roadmap for CRA Applicability
We advise starting with a product audit: list every item sold in the EU and check for digital elements. Next, classify each product per CRA risk tiers and map gaps against the 21 essential requirements. Building the SBOM early and integrating secure coding practices into your workflow is critical.
Finally, set up a robust vulnerability management process. At our bootcamp, we run tabletop exercises simulating incidents to practice rapid responses. By doing this now, teams won’t be scrambling in 2026, they’ll know exactly how to meet CRA deadlines confidently.
FAQ
When does the Cyber Resilience Act apply to products with digital elements in the EU?
The EU Cyber Resilience Act applies to almost all digital products with digital elements sold in the European Single Market. This includes smart devices, smart home devices, and remote data processing solutions.
Compliance starts with understanding CRA requirements, performing risk assessments, and implementing cybersecurity standards across the product lifecycle to prevent security flaws and meet reporting obligations.
How should developers handle vulnerability management under the Cyber Resilience Act?
Products with digital elements require strong vulnerability handling processes. Software developers must track security flaws, coordinate incident reporting, and deliver timely updates. CRA requirements emphasize secure by design principles and continuous vulnerability management across the product lifecycle.
Using a Software Bill of Materials helps identify affected components, ensuring compliance with cybersecurity requirements and protecting the product and supply chain from online attacks.
What are the main conformity assessment obligations for digital products under the CRA?
The CRA sets risk-based conformity assessment paths. Default products may allow internal self-assessment, while critical products require evaluation by a notified body or Conformity Assessment Body.
Compliance includes technical documentation, EU Declaration of Conformity, CE marking, and adherence to harmonised standards like ETSI EN 303 645. These steps ensure consistent cybersecurity standards across Member States.
Are open-source software or non-commercial components exempt under the EU Cyber Resilience Act?
Free, non-commercial open-source software is generally excluded from CRA obligations. However, if incorporated into a product with digital elements sold in the EU, the final digital product must meet all CRA requirements.
Developers must apply secure by design principles, document dependencies with a Software Bill of Materials, and maintain cybersecurity standards and reporting obligations for the combined solution.
Final Steps for the New Digital Reality
The Cyber Resilience Act sets the new baseline for secure digital products in Europe. Manufacturers must embed security from design to end-of-life, or risk fines, recalls, and lost market access.
At our Secure Coding Practices Bootcamp, we train developers with hands-on coding labs covering OWASP Top 10, input validation, secure authentication, encryption, and dependency safety. Build safer products from day one, join the bootcamp today and start your compliance journey.
References
- https://openssf.org/blog/2024/11/25/understanding-the-cra-openssfs-role-in-the-cyber-resilience-act-implementation-part-1/
- https://www.ics.com/blog/cyber-resilience-act-isnt-just-europes-problem

