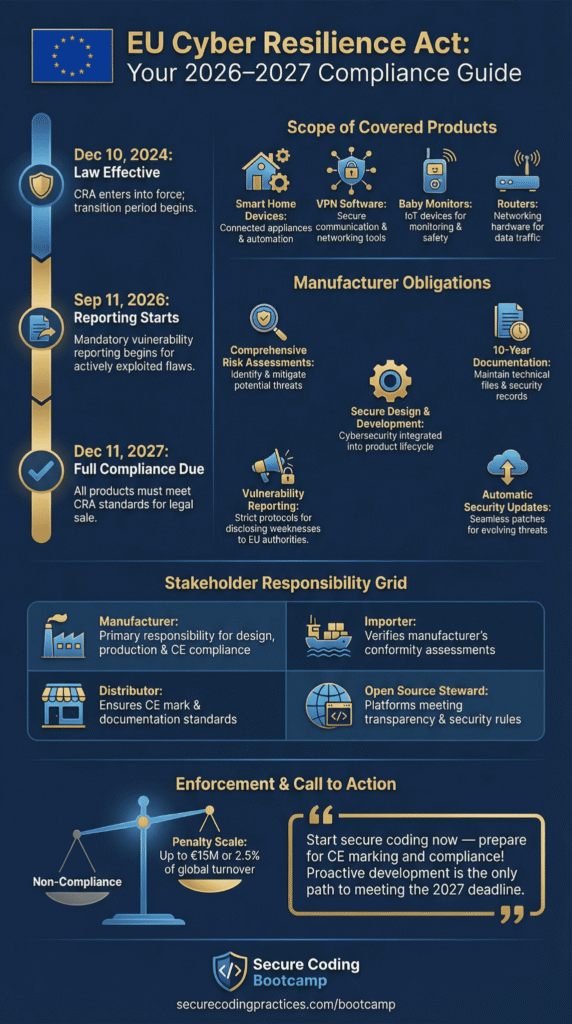
EU Cyber Resilience Act explained, officially Regulation (EU) 2024/2847, it imposes mandatory cybersecurity requirements on digital products sold in the EU. It took effect on December 10, 2024. Full compliance is required by December 11, 2027. However, the obligation to report vulnerabilities starts even earlier, on September 11, 2026.
That deadline is the real pressure point. Companies that aren’t preparing now will face a difficult scramble. This law changes everything about how connected devices and software are designed, documented, and maintained for the EU market. If you sell these products, it applies to you.
Many teams are now aligning development with secure coding practices so their products meet the evolving expectations of the Cyber Resilience framework before enforcement deadlines arrive.
EU Cyber Resilience Act: What You Must Know Now
- The Cyber Resilience Act mandates lifecycle cybersecurity for all products with digital elements sold in the EU.
- Reporting exploited vulnerabilities becomes mandatory in 2026, full compliance in 2027.
- Secure Coding Practices and structured vulnerability management are now regulatory expectations, not optional upgrades.
What Is the EU Cyber Resilience Act?
The EU Cyber Resilience Act establishes binding cybersecurity requirements for hardware and software products connected directly or indirectly to networks within the European Union regulation EEA framework.
The law targets systemic cyber risk. According to the European Commission,
“The Cyber Resilience Act (CRA) aims to safeguard consumers and businesses buying software or hardware products with digital elements. The CRA addresses the inadequate level of cybersecurity in many products and the lack of timely security updates. It also tackles the challenges consumers and businesses currently face when trying to determine which products are cybersecure and in setting them up securely.” – European Commission
This makes the purpose of the regulation very clear. It is not just about preventing attacks. It is about raising the baseline of cybersecurity across the entire EU digital market.
Products must resist known threats and provide secure update mechanisms. It applies whether a product is sold for payment or provided free of charge. That includes software-only products, embedded systems, and remote processing solutions. If the product connects, it likely falls in scope.
The key obligations are clear. Companies must:
- Conduct cyber risk assessments during development and support.
- Keep technical documentation for 10 years.
- Implement automatic security updates.
- Report severe incidents to authorities.
Fines are steep: €15 million or 2.5% of global annual turnover, whichever is higher. These figures are set by the European Commission and backed by ENISA.
Which Products Fall Within the CRA Scope?
Credits: Hogan Lovells
If a product has digital bits and connects to a network, the CRA likely covers it. The only real exceptions are for things like medical devices, already regulated elsewhere.
This means both business and home products are in scope. Your Wi-Fi router, smart vacuum, or baby monitor now has to meet these new IoT security rules.
Enterprise systems are included as well. Network Management Systems, VPN software, IAM software, and Container Runtime Systems are covered when placed on the EU market. Even spare parts with digital elements qualify.
Open source treatment depends on the commercial context. Pure non-commercial open source software remains exempt. Commercial distribution or integration into a product brings it into scope. Open source stewards must maintain cybersecurity policies and cooperate on vulnerability handling.
Here is a simplified scope comparison:
| Category | Example | In Scope? |
| Consumer IoT | Smart home devices | Yes |
| Enterprise Software | Network devices software | Yes |
| Medical devices | Regulated separately | No |
| Motor vehicles | Covered by other EU law | No |
Reporting obligations begin in 2026, even for products placed on the market before full applicability in 2027. Legacy products are not retroactively redesigned unless substantially modified, but reporting still applies.
What Are the Core Security Requirements for Manufacturers?
The core security requirements for manufacturers are straightforward. They must build secure development practices, manage risk across the product’s entire lifecycle, and define a clear support period. This isn’t optional for any digital product sold in the EU.
Annex I of the Act lists the essential rules. As outlined in ENISA’s official requirements mapping,
“Products with digital elements shall be designed, developed, and produced in such a way that they ensure an appropriate level of cybersecurity based on the risks;… [and] shall be delivered without any known exploitable vulnerabilities.” – ENISA
This language is strict. It means security cannot be added later as a patch strategy. It must be built in from the start. Products must be protected against known security holes. They need a secure way to receive updates, use proper encryption, and withstand common attacks.
Manufacturers also have to:
- Announce a defined support period, typically five years.
- Keep technical documentation for a decade.
- Provide a software bill of materials (SBOM) listing components.
- Maintain a vulnerability management process.
The rules work with existing standards, like ETSI EN 303 645 for IoT and ISO/IEC 27001 for security management, to build a single EU-wide framework.
Roles and Obligations Across the Supply Chain

The CRA divides responsibilities. Manufacturers, importers, distributors, and even open-source stewards each have specific duties.
The manufacturer carries the heaviest load. They must complete the conformity assessment, draft the EU Declaration of Conformity, and affix the CE mark. Importers verify the manufacturer’s work before the product enters the EU. Distributors ensure the product has the correct labels and instructions.
The reporting deadlines are fixed and very short:
- An early warning must go out within 24 hours of finding a serious issue.
- A detailed notification is due within 72 hours.
- A final report is required within 14 days for actively exploited flaws, or one month for other severe incidents.
| Stakeholder | Main Duties | Reporting Obligation |
| Manufacturer | Risk assessment, documentation, CE marking | 24h early warning |
| Importer | Verify compliance, halt non-compliant products | Confirm reporting |
| Distributor | Verify markings and support info | Report suspicions |
| Open-Source Steward | Maintain security policy | Cooperative reporting |
We’ve worked with companies where no one was sure who owned these tasks. To avoid missing a critical deadline, you need a clear internal team responsible for incident response, guided by ENISA’s guidelines.
How Does Conformity Assessment Work?
The conformity assessment process depends on your product’s classification. For most standard products, manufacturers can perform a self-assessment. But for important or critical products, you’ll need a third-party review.
Annex III defines what counts as an “important” product, like specific network security tools. Annex IV lists “critical” products, which include things like operating systems and core infrastructure software.
For these critical items, a designated “notified body” must check your compliance. In some cases, they might even require a formal European cybersecurity certificate before you can apply the CE mark.
Member States have until June 11, 2026, to appoint these notified bodies. While self-assessment is allowed if you correctly follow the official standards, getting it wrong means your product can’t be sold. From our experience helping teams, we recommend building these compliance checks into your development pipeline now.
Teams that rely too heavily on rapid vibe coding without structured security validation may struggle when formal conformity assessments begin. Waiting until 2026 will create a major bottleneck.
What Is the Official CRA Timeline?

The official timeline has three key dates that every company needs to mark on its calendar.
The Act itself became law on December 10, 2024. The mandatory vulnerability reporting requirement starts on September 11, 2026. Full technical compliance for all new products is required by December 11, 2027.
| Phase | Date | Impact |
| Entry into Force | Dec 10, 2024 | Regulation active |
| Notified Bodies | Jun 11, 2026 | Certification system operational |
| Reporting Live | Sep 11, 2026 | Mandatory incident reporting |
| Full Applicability | Dec 11, 2027 | All new products are compliant |
There’s an important detail about existing products. Legacy products placed on the market before December 2027 don’t need a full redesign, unless they are “substantially modified.” However, the new reporting rules will still apply to them starting in September 2026. We’ve seen this point cause a lot of confusion in discussions with developers.
Penalties and Enforcement Mechanisms
Each EU member state has its own market surveillance authority to enforce the CRA, and they all work together. The penalties for getting it wrong are serious.
Fines can go as high as €15 million, or 2.5% of a company’s total worldwide yearly revenue, for breaking the core security rules. For less serious violations, fines can still reach €5 million or 1% of revenue.
If your company is based outside the EU, you must appoint an authorized representative within the EU to keep selling there. Small businesses get some breaks on fines for missing reports, but they still have to follow all the other rules.
Enforcement will focus on transparency. This means your documentation, your software bill of materials (SBOM), and your logs of security incidents are just as important as the technical security of the product itself.
How Should Businesses Prepare for CRA Compliance?
Businesses need to start preparing now. The key is to map your products, build secure development controls, and set up reporting workflows well before the 2026 deadline.
We always tell our clients to start with secure coding practices. As discussions grow around whether AI-generated code will dominate future development, teams still remain accountable for security outcomes under the CRA.
In our bootcamps, when teams build security in from the start, their risk assessments become useful, living documents instead of a last-minute rush. This method follows guidelines like NIST SP 800-161 and saves money by avoiding expensive late-stage redesigns.
Your immediate to-do list should include:
- Deciding who owns compliance across your product and legal teams.
- Setting up a clear process for reporting vulnerabilities.
- Building the ability to create and manage SBOMs.
- Performing a cyber risk assessment for your product’s entire lifecycle.
In the next year or so, you’ll need to align your technical documentation with Annex I and prepare your CE marking files. Companies that wait until 2026 to start will face long certification delays in 2027. Those who delay too long risk losing access to the entire EU market.
FAQ
What does the Cyber Resilience Act mean for my digital products?
The Cyber Resilience Act is a European Union regulation that sets mandatory cybersecurity requirements for products with digital elements sold in the European Union. This includes digital products, connected devices, IoT devices, and software-only products.
If you place a product with digital elements on the EU market, you must conduct risk assessments, address security vulnerabilities, provide timely security updates, and ensure compliance throughout the entire product lifecycle.
Do my connected devices need CE marking under the EU Cyber Resilience Act?
Yes, many connected devices must undergo a conformity assessment before they can carry the CE mark. Under this European Union regulation EEA framework, manufacturers must demonstrate compliance with the cybersecurity requirements listed in Annex I.
After meeting these security requirements, they must prepare an EU Declaration of Conformity. Certain critical products may require third-party evaluation before receiving market approval and CE marking.
How are software developers affected by new cybersecurity obligations?
Software developers who create products with digital elements must follow secure by design and cybersecurity by default principles. The EU Cyber Resilience Act requires secure development practices, structured vulnerability management, automated security testing, and formal incident reporting processes.
Developers must maintain a software bill of materials, support automatic security updates, and reduce product security gaps across the full product lifecycle to comply with cybersecurity standards.
What types of products are covered by the EU Cyber Resilience Act?
The Cyber-Resilience Act applies to a broad range of digital products and connected devices placed on the European Union market.
Covered items include smart home devices, baby monitors, alarm systems, Wi-Fi routers, network devices, Industrial IoT systems, embedded systems, robo-vacuum cleaners, VPN software, IAM software, Container Runtime Systems, Network Management Systems, and spare parts with digital elements that contain digital features.
How does the Act handle vulnerability management and incident reporting?
The EU Cyber Resilience Act establishes clear rules for vulnerability management and incident reporting. Manufacturers must identify and fix security vulnerabilities, conduct cyber risk assessments, and report severe incidents within required timelines.
They may need to coordinate with the European Union Agency for Cybersecurity and follow ENISA Guidelines. Organizations must also maintain a security incident response team and implement cybersecurity measures to reduce cyber threats and data breaches.
EU Cyber Resilience Act Compliance: The 2026–2027 Countdown
The EU Cyber Resilience Act is not a distant rule. It is a deadline, December 11, 2027, moving closer each day. You can react under pressure, or you can lead with confidence. Teams that build secure coding practices now will not just comply. They will reduce breach risk, avoid costly recalls, and earn long-term customer trust across the European market.
Join the Secure Coding Practices Bootcamp and train your team through hands-on labs, real-world code reviews, and practical security skills. No jargon. Just action. 👉 https://securecodingpractices.com/bootcamp/#Join
References
- https://digital-strategy.ec.europa.eu/en/policies/cyber-resilience-act
- https://www.enisa.europa.eu/publications/cyber-resilience-act-requirements-standards-mapping
