If you sell any connected hardware or software in Europe, the scope of EU Cyber Resilience Act (CRA) applies to you. It’s a sweeping new law that mandates cybersecurity for virtually every product with digital elements placed on the EU market. This isn’t just for tech giants, it covers everything from smart lightbulbs to mobile apps.
The clock is ticking, with key requirements kicking in September 2026. Understanding the scope is your first, non-negotiable step toward compliance. Keep reading to decode what this regulation truly means for your business and your products.
What the EU Cyber Resilience Act Covers
Before diving into the details, here’s what you need to know about the EU Cyber Resilience Act at a glance:
- The CRA’s scope is intentionally broad, covering nearly all connected products not already under specific sector laws.
- Products are split into four risk tiers, which dictate the rigor of the required compliance process.
- The law imposes strict, tiered reporting deadlines for vulnerabilities, starting with a 24-hour alert to authorities.
What Products Fall Under The Scope Of EU Cyber Resilience Act
Look around your office or home. The laptop you’re using, the router blinking in the corner, the app on your phone. If it can connect to a network, directly or indirectly, it’s likely a “product with digital elements” (PDE) under the CRA. The European Commission cast a wide net, aiming to cover the entire digital ecosystem.
This includes both hardware with embedded software and stand-alone software, even “remote data processing solutions,” which is essentially a formal term for many cloud services.
The goal is horizontal regulation, a baseline of security across all sectors. They estimate it covers nearly 100% of connected digital products not already governed by stricter, vertical rules. Think of it as a new floor for cybersecurity, one that every market participant must build upon.
- Connected consumer devices (IoT gadgets, smart home gear).
- Commercial software and applications.
- Network-connectable hardware components.
Which Sectors and Product Categories Are Exempt from the CRA?
Credits: Hogan Lovells
The CRA isn’t universal. It leaves specific sectors alone where EU law already sets cybersecurity rules, which avoids a regulatory mess for companies. We see this as practical, but it means you need a checklist.
“The Cyber Resilience Act (CRA) is an EU regulation that sets mandatory cybersecurity requirements for hardware and software with digital elements throughout their lifecycle, from design to end-of-life. […] it is a product-centric law that makes secure‑by‑design and secure‑by‑default engineering a legal duty for manufacturers and publishers placing products on the EU market.” – Cycode
For example, medical devices stay under the MDR. Your car’s software has its own automotive rules. Non-commercial open-source projects get a pass, though commercial involvement can change that. These aren’t loopholes; they’re clear carve-outs.
- Medical devices (EU MDR)
- Motor vehicles and aviation
- Defense and national security products
- Non-commercial open-source software
How Are Products Classified Under the CRA Risk Tiers?
Risk determines the rules. The CRA uses four tiers: Default, Important Class I & II, and Critical. This classification is crucial, it sets your entire compliance path. In our training, we stress that most products (think smart toys or basic apps) will be “Default,” allowing for internal self-assessment.
But as risk climbs, so does scrutiny. Important Class II items, like firewalls, need a third-party check. Critical products, including hardware security modules, face the toughest certification. Getting the tier wrong means wasted effort or dangerous shortcuts.
Here’s what each tier usually covers:
| CRA Risk Tier | Example Products | Conformity Assessment Path |
| Default | Smart toys, photo editing apps, most consumer IoT. | Internal self-assessment. |
| Important Class I | Password managers, identity management systems. | Internal self-assessment. |
| Important Class II | Firewalls, industrial routers, hypervisors. | Third-party assessment by a notified body. |
| Critical | Smart meter gateways, hardware security modules. | Most rigorous third-party certification. |
What Are the Mandatory Reporting Timelines for Vulnerabilities?
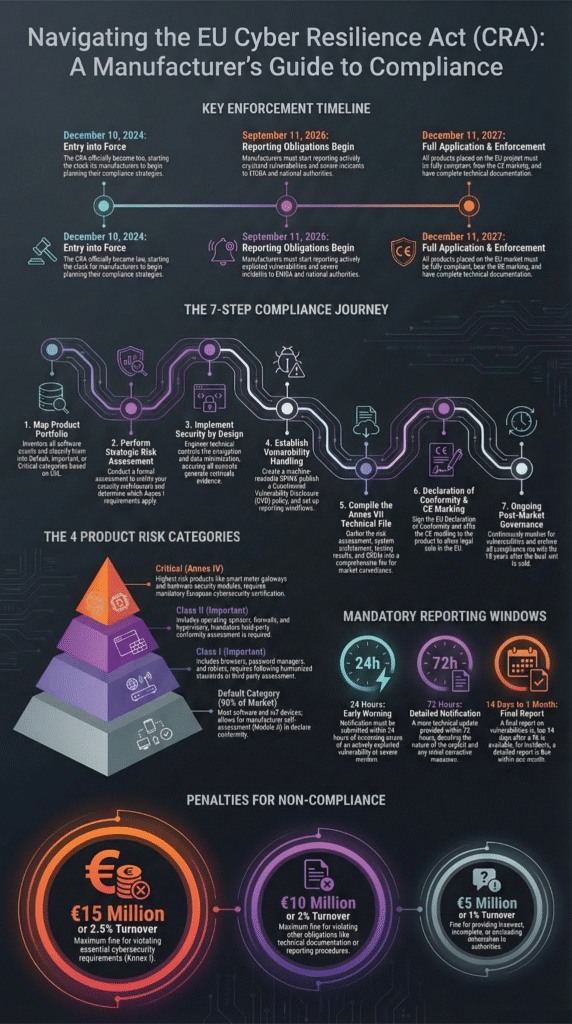
An infographic detailing the scope of the EU Cyber Resilience Act and key enforcement timelines for compliance.
This is where the “resilience” part gets real. The CRA mandates a strict, multi-stage reporting cascade when a severe incident or actively exploited vulnerability is discovered. It’s not a suggestion, it’s a countdown.
“The CRA proposal covers all products with digital elements put on the market which can be connected to a device or a network, including their building blocks (i.e., hardware and software), and encompassing also solutions provided in a Software as a Service (SaaS) fashion if they qualify as remote [data processing].” – European-Cyber-Resilience-Act
The moment you become aware, a 24-hour timer starts for an early warning to ENISA and your national CSIRT team. It’s a heads-up, a flare shot into the night.
Then you have 72 hours to submit a detailed initial report. Fourteen days after that, a final analysis is due, complete with root cause and remediation steps. This timeline transforms vulnerability management from an internal IT task into a regulatory obligation with legal weight. For teams used to quieter fixes, this transparency will feel jarring.
The reporting obligation itself goes live on September 11, 2026, making your incident response plan a cornerstone of compliance.
What Are the Penalties for Non-Compliance with the CRA?
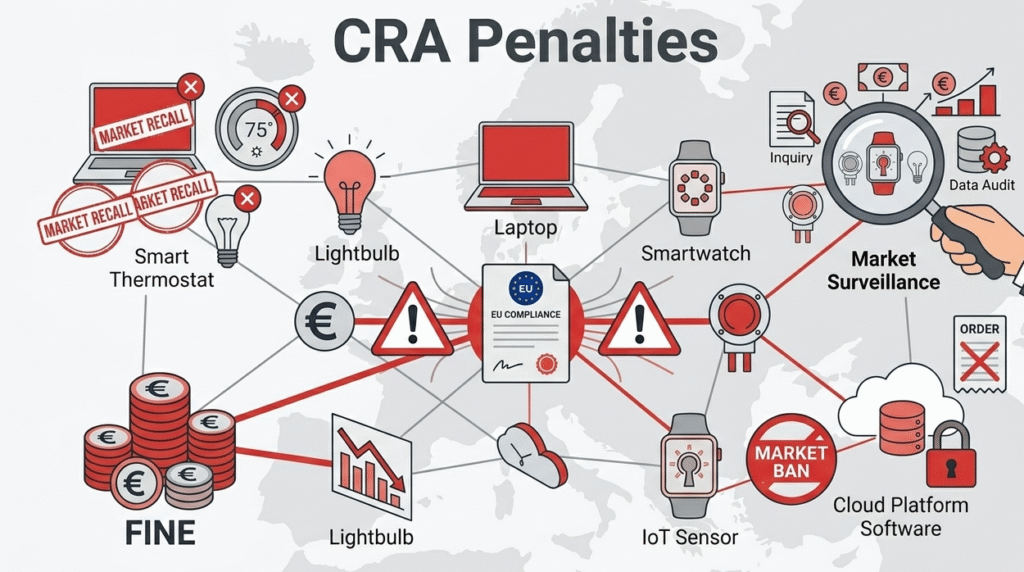
The EU is serious. Non-compliance isn’t a slap on the wrist, it’s a existential business threat. Financial penalties can reach up to €15 million or 2.5% of your total global annual turnover, whichever is higher. For failing to report a severe incident, fines can hit €10 million or 2% of turnover. The numbers are designed to get the attention of any C-suite.
Beyond fines, market surveillance authorities have powerful tools. They can order a product recall, demand its withdrawal from the EU market, or impose a complete sales ban. Imagine the logistics, the reputational damage, the shareholder questions.
The law entered force in December 2024, with a long runway for a reason. The full weight of enforcement arrives in December 2027, but the core requirements start in 2026. Preparing now isn’t early, it’s essential.
FAQ
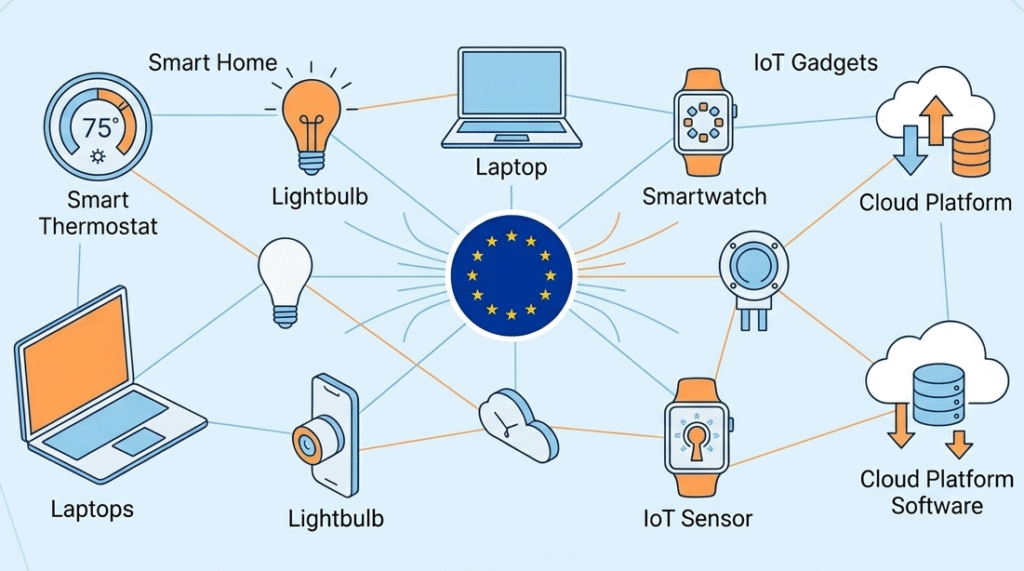
Which digital products are included under the Cyber Resilience Act?
The Cyber Resilience Act (CRA) applies to all products with digital elements placed in the European Union. This includes hardware and software that connect to a network, IoT devices, smart home devices, and remote data processing solutions.
Products like software-defined vehicles or embedded software also fall under CRA requirements, ensuring basic cybersecurity standards across the digital ecosystem.
How are products classified under the EU Cyber Resilience Act risk tiers?
Under the CRA, digital products are categorized into Default, Important Class I, Important Class II, and Critical. Classification depends on the product’s function, exposure to cyber threats, and potential impact on operational resilience.
Critical products, such as baby monitors or industrial IoT devices, require the strictest conformity assessment, including third-party evaluation by a notified body, before market entry in the European Union.
What are the key reporting obligations for severe security incidents?
Products with digital elements must follow CRA vulnerability management rules. Severe incidents must be reported quickly to the security incident response team and European Union Agency for Cybersecurity.
Initial alerts are due within 24 hours, followed by detailed reports within 72 hours, and final remediation updates later. This ensures a robust operational resilience framework and mitigates online attacks and data breaches.
Are any products or sectors exempt from the EU Cyber Resilience Act?
Yes, the CRA exempts products already regulated under sector-specific laws. Medical devices governed by the European Medical Device Regulation, software under open-source licenses without commercial contribution, and certain automotive hardware or defense products fall outside CRA scope.
This avoids conflicts with other EU cybersecurity requirements while still enforcing baseline standards for general digital products in the European Union.
Navigating the New Digital Landscape
The Cyber Resilience Act fundamentally changes manufacturing in Europe. It’s not about a checkmark; it’s about embedding security into your product’s entire life. Exemptions are narrow, risk tiers are strict, and reporting clocks are ticking. Your first move is an honest audit to see where your products fit.
The real work begins now. Every connected product you sell is a direct statement of your security posture.
Building that resilient foundation requires skilled developers. Our hands-on Secure Coding Bootcamp trains teams in practical, essential security practices. Equip your team to build securely from the start.

