Open source and supply chain security are now central to regulatory compliance under the Cyber Resilience Act (CRA). We’ve seen organizations struggle not because they lack tools, but because managing dependencies, documentation, and validation processes becomes overwhelming at scale.
These challenges often surface during audits, when it’s already too late to fix gaps efficiently. By understanding CRA requirements early, teams can reduce friction and risk exposure. Keep reading to learn how to approach compliance with clarity and confidence.
Open Source and Supply Chain Under the Cyber Resilience Act
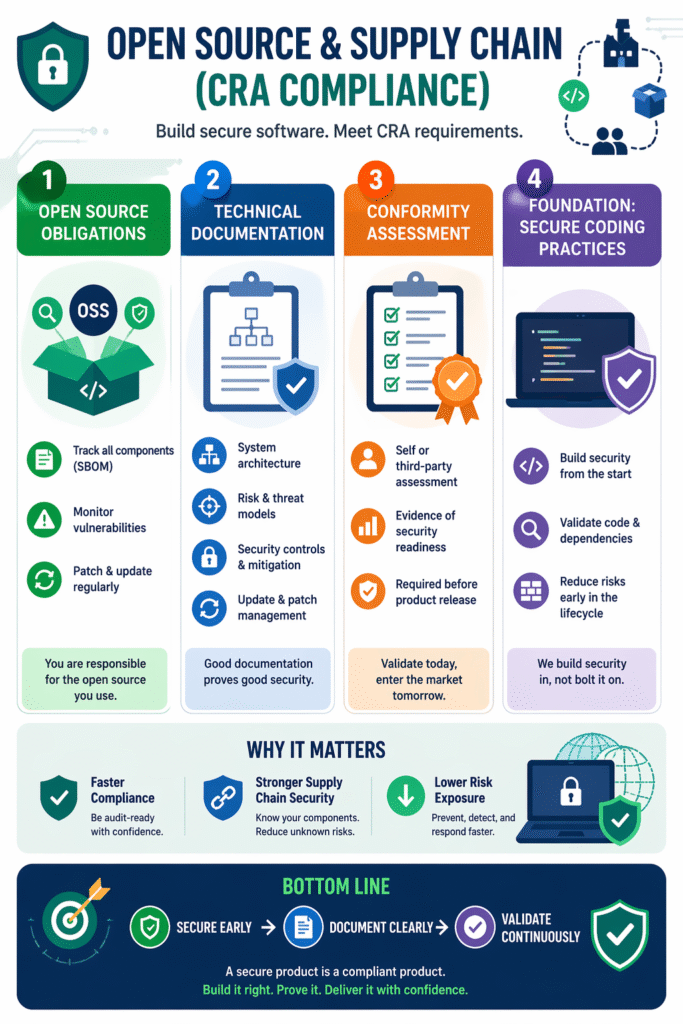
To navigate CRA requirements effectively, it’s important to focus on what truly drives compliance:
- Open source obligations demand visibility and continuous risk management
- Technical documentation must reflect real security practices, not assumptions
- Conformity assessment validates readiness before market access
Open Source Obligations Cyber Resilience Act
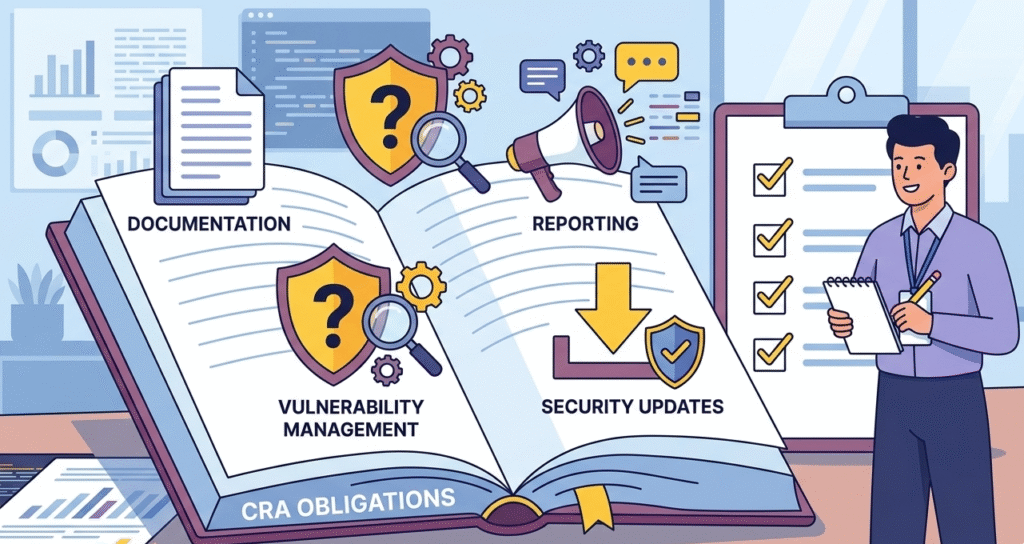
Open source components are deeply embedded in modern software supply chains. However, under the CRA, organizations are accountable for how these components are managed.
Key expectations include:
- Maintaining a Software Bill of Materials (SBOM)
- Tracking vulnerabilities across dependencies
- Ensuring timely remediation and disclosure
We’ve worked with teams where open source usage grew organically without governance. Over time, this creates blind spots that are difficult to untangle during compliance checks.
“Open-source software is software with source code that anyone can inspect, modify, and enhance.” – Wikipedia
That flexibility is valuable, but it also introduces shared responsibility. This is why we prioritize Secure Coding Practices early, reviewing dependencies, validating inputs, and enforcing secure standards helps reduce supply chain risks before they escalate.
Cyber Resilience Act Technical Documentation
Credits: Brodie Robertson
Technical documentation is a critical pillar of CRA compliance. It demonstrates not only what was built, but how security was considered throughout the process.
This includes:
- Architecture and system design
- Risk assessments and threat models
- Security controls and mitigation strategies
- Update and patch management workflows
In many cases, teams treat documentation as an afterthought. From what we’ve seen, that approach leads to inconsistencies and audit delays.
“Technical documentation refers to any document that explains the use, functionality, creation, or architecture of a product.” – Wikipedia
When Secure Coding Practices are embedded into development, documentation becomes easier to maintain because security decisions are already structured and traceable.
Conformity Assessment Cyber Resilience Act
Conformity assessment ensures that products meet CRA requirements before entering the market. It’s essentially the checkpoint where all security, documentation, and risk management efforts are validated.
This process may involve:
- Internal self-assessments
- Third-party audits depending on risk classification
- Continuous compliance monitoring
We’ve seen organizations delay product releases simply because evidence wasn’t organized or complete. The issue isn’t always security, it’s proof.
A more effective approach is to align development and compliance early. By applying Secure Coding Practices from the beginning, teams can generate consistent evidence, streamline validation, and reduce last-minute pressure during assessments.
Supply Chain Risk Management Cyber Resilience Act
Beyond open source obligations, the CRA emphasizes full supply chain visibility and control. This includes not only software components but also vendors, integrations, and third-party services.
Key focus areas:
- Vendor risk assessment and continuous monitoring
- Dependency mapping across the entire software lifecycle
- Incident response readiness for supply chain attacks
- Integration of security controls across development and deployment
From what we’ve seen, organizations often focus only on code-level risks, but overlook supplier dependencies. This creates gaps that attackers can exploit.
By combining this with Secure Coding Practices, we reduce exposure at both the code and ecosystem level, ensuring that security is not just internal, but extends across the entire supply chain.
FAQ
What are open source obligations under the Cyber Resilience Act?
Organizations must actively manage all open source components used in their software. This includes maintaining an up-to-date SBOM, identifying vulnerabilities, and applying patches promptly. It’s not enough to rely on community updates—companies are responsible for ensuring their supply chain remains secure and compliant over time.
Why is technical documentation important for supply chain security?
Technical documentation provides visibility into how software is built and secured. It helps organizations trace dependencies, understand risk decisions, and demonstrate compliance during audits. Without proper documentation, even well-secured systems can appear non-compliant due to lack of evidence.
What is involved in conformity assessment under the CRA?
Conformity assessment evaluates whether a product meets CRA security requirements. Depending on the product’s risk level, this may include internal reviews or third-party audits. It also requires clear documentation, testing evidence, and proof that vulnerabilities are managed effectively.
How do Secure Coding Practices improve CRA compliance?
Secure Coding Practices reduce vulnerabilities at the source by enforcing secure design, validation, and testing during development. We’ve found that when teams apply these practices early, they spend less time fixing issues later and face fewer obstacles during compliance assessments.
Open Source and Supply Chain Compliance Strategy
Open source and supply chain security under the Cyber Resilience Act require structured, ongoing processes. Success comes from aligning development, documentation, and validation from the start. By embedding Secure Coding Practices into workflows, teams reduce risk and simplify compliance.
Ready to strengthen your approach? The Secure Coding Practices Bootcamp offers hands-on training in OWASP essentials, encryption, and safe dependencies, equipping your team to ship safer code from day one. Secure Coding Practice: Join the Bootcamp
References
- https://en.wikipedia.org/wiki/Open-source_software
- https://en.wikipedia.org/wiki/Technical_documentation
