When we think about protecting our networks, network segmentation and trust boundaries come to the forefront as some of the most effective ways to keep threats at bay. They break down your vast network into manageable, secure pieces, making it harder for attackers to roam freely if they get inside. (1)
We rely heavily on secure coding practices to ensure these segments are well-defined and enforced. Trust boundaries act like checkpoints, controlling who gets through and what they can access. Keep reading if you want to understand how to build a stronger, more resilient network.
Key Takeaways
- Network segmentation confines access and traffic, drastically reducing attack surfaces.
- Trust boundaries enforce strict control over communications between segments.
- Combining segmentation with Zero Trust principles and microsegmentation tightens security further.
The Growing Need for Robust Network Security
Data breaches aren’t just frequent, they’re devastating. According to IBM’s 2025 report, the average cost of a U.S. data breach is about $10.22 million. (2) That’s not just money lost, but trust broken and reputations damaged. Relying solely on traditional network defenses like perimeter firewalls feels like locking the front door but leaving the windows wide open.
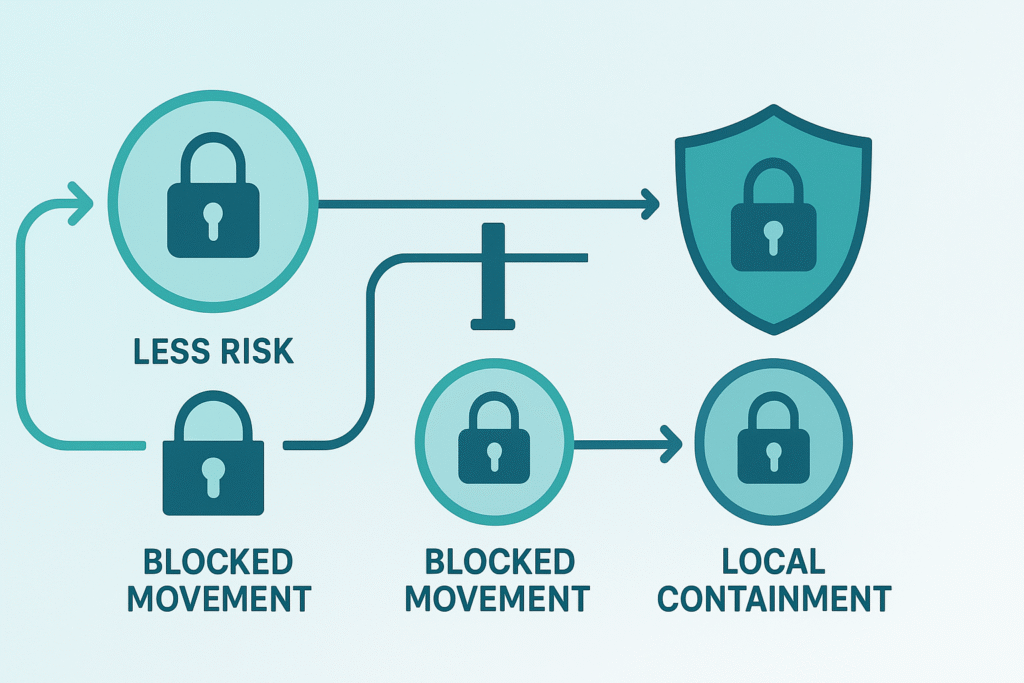
Attackers may exploit gaps to move laterally if segmentation is weak. Static, perimeter-only defenses are increasingly insufficient against modern threats like lateral movement.
The solution lies in slicing your network into smaller, isolated zones. Each segment has its own rules and controls. This approach limits exposure and makes it harder for an attacker to travel unchecked once inside. It’s something we’ve implemented ourselves with great success, tightening our security posture while still keeping operations smooth.
Understanding Network Segmentation
Network segmentation breaks a large network into smaller, isolated zones. This isn’t just about neat organization; it’s about limiting what can talk to what. When you separate systems by role, data sensitivity, or application tier, you create natural choke points to control traffic flow.
We often start with three main segmentation approaches:
- Role-based segmentation: grouping users and devices by function, like separating HR systems from IT operations.
- Data sensitivity-based segmentation: isolating highly confidential data from less critical information.
- Application tier segmentation: segregating front-end web servers from back-end databases.
This layering means even if one segment suffers a breach, the attacker can’t easily hop to others. In many cases, segmentation helps limit spread and makes incident response more efficient.
Defining Trust Boundaries
Think of trust boundaries as border control within your network. These boundaries mark where one segment ends and another begins. They govern who and what can cross, under what conditions.
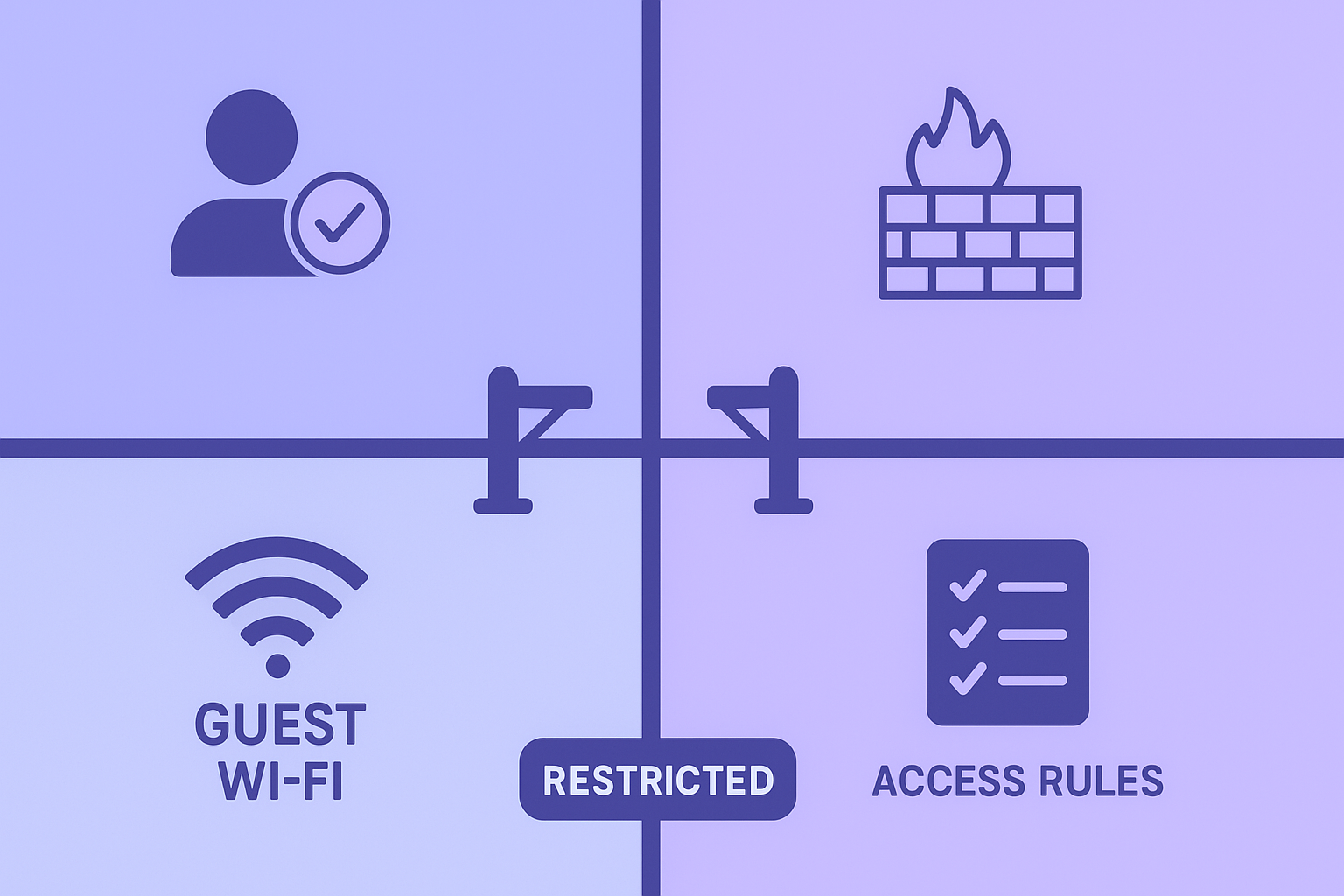
Clear trust boundaries matter because they enforce your security policies at key intersections. For example, crossing from a guest Wi-Fi zone to the corporate network should be tightly controlled, requiring authentication or other checks. We like to think of them as checkpoints that verify credentials and permissions before passage.
Without well-defined trust boundaries, segmentation falls apart. Traffic would flow freely, defeating the purpose of dividing the network. Establishing these boundaries means setting up firewalls, access controls, and monitoring systems that watch every crossing closely.
Implementing Network Segmentation and Trust Boundaries: A Step-by-Step Approach
Credits: Jenta Tech
Breaking down this process makes it more manageable. Here’s an approach that we’ve refined over multiple deployments:
Step 1: Identify Critical Assets and Data Flows
First, take inventory. What systems, applications, and data are most critical? Map out how data moves between them, similar to how teams visualize data flow to understand interactions. For instance, a hospital might pinpoint patient records and medical devices as high priority.
Step 2: Define Network Segments
Group assets logically based on roles, sensitivity, or tiers. This might mean separating guest Wi-Fi from corporate systems or isolating financial databases.
Step 3: Establish Trust Boundaries
Define rules for communication between segments. Strengthen these rules by clarifying trust boundaries within your environment. Implement authentication and authorization controls. For example, accessing sensitive data might require multi-factor authentication.
Step 4: Implement Security Controls
Deploy firewalls, intrusion detection or prevention systems, and access control lists. These controls enforce your trust boundaries, filtering traffic and stopping unauthorized access.
Step 5: Monitor and Enforce Security Policies
Continuous monitoring is vital. Keep an eye on network traffic, conduct audits, and be ready with an incident response plan.
This methodical approach ensures you build a segmentation framework that’s both secure and practical. We’ve learned that patience here pays off; rushing leads to gaps and misconfigurations.
The Role of Zero Trust
Zero Trust means verifying every request, even inside your network, rather than trusting by default. Every access request is continuously verified, regardless of origin.
Network segmentation supports Zero Trust by enabling granular control and helps teams in managing trust boundaries more precisely. You can enforce policies down to individual applications, workloads, or even devices, a concept known as microsegmentation. This fine-grained segmentation closes doors that might otherwise remain ajar.
When we apply secure coding practices in conjunction with segmentation, our software respects these boundaries from the ground up. This combination helps prevent vulnerabilities that attackers might exploit to bypass controls.
Benefits of Network Segmentation and Trust Boundaries
Here’s what happens when you get segmentation and trust boundaries right:
- The attack surface shrinks. Fewer entry points mean fewer chances for attackers to slip in.
- Lateral movement gets limited. If an attacker gains access, they can’t roam freely.
- Segmentation helps contain breaches and localize damage, buying valuable time for response.
- Security policies are enforced consistently across the network.
- Compliance becomes easier, especially with regulations that require strict data protection.
We’ve witnessed firsthand these benefits. They translate into fewer incidents, quicker recovery, and a more confident security team.
Tools and Technologies for Network Segmentation
There’s no shortage of tools to help. Firewalls remain central, but today’s solutions also include network monitoring, analysis platforms, and automation tools for segmentation.
Many organizations overlook the value of workload segmentation and cloud segmentation. These approaches apply the same principles to virtual and cloud environments, which are often more dynamic and complex.
We use automation to continuously apply segmentation policies, reducing misconfiguration and human error.
Getting Started with Network Segmentation
If the idea of segmenting your network feels overwhelming, start small:
- Conduct a thorough security assessment to understand your current state.
- Develop a clear segmentation plan that prioritizes your most critical assets.
- Implement segmentation gradually, starting with high-risk areas.
- Use continuous monitoring to validate effectiveness and adjust as needed.
Taking these steps has made a big difference for us. It’s a journey that requires commitment but pays off in stronger defenses.
FAQ
How do I know which network zones I should create first?
Start by looking at what your team needs most. Sort your systems by data sensitivity, risk management, and how often they talk to each other. Then group them into simple network zones. This helps you plan a clear segmentation strategy. It also supports better network isolation, traffic control, and risk mitigation, even before you add tools like firewall segmentation or network monitoring.
How can network segmentation help stop lateral movement inside my company?
Good network segmentation blocks easy paths attackers might use. When you build strong trust boundaries and set access control rules, bad actors cannot move from one zone to another. Adding micro-segmentation, granular access control, and network traffic filtering makes this even tighter. These steps shrink the attack surface and keep your internal network security safer.
What should small teams focus on when starting a segmentation framework?
Small teams can begin with simple steps: list important data, pick clear security zones, and set basic access policies. Use helpful network segmentation tools and keep the design easy to manage. Add segmentation enforcement slowly to avoid mistakes. Over time, bring in network microsegmentation, workload segmentation, and cloud segmentation to build a stronger security architecture that fits your size.
How does Zero Trust change the way I use segmentation?
Zero Trust means no part of the network is trusted by default. This approach makes network partitioning, application segmentation, and network tiers more important. You will check every request, even inside trusted networks. When paired with segmentation policies, protected network design, and network defense tools, Zero Trust reduces network segmentation risks and strengthens your whole security perimeter.
What challenges should I expect during segmentation implementation?
Common issues include unclear segmentation boundaries, too many access policies, and complex segmentation deployment steps. Some apps may not fit cleanly into your network segmentation topology. You may also face segmentation compliance needs or limits in older systems. Regular threat modeling, secure network design, and segmentation automation help reduce these problems and keep your segmentation framework steady.
Conclusion
Network segmentation and trust boundaries aren’t just technical jargon; they’re the backbone of a secure network architecture. By dividing the network into zones with carefully controlled communication channels, organizations reduce risk and enhance control.
Our experience shows that integrating secure coding practices early on is crucial. Building segmentation into both software and network design prevents weak points before they appear. Trust boundaries then act as vigilant gatekeepers, scrutinizing every crossing and ensuring that only the right traffic moves between segments.
Together, these strategies form a powerful defense that supports Zero Trust principles, limits attackers’ freedom, and protects sensitive data. If you’re serious about strengthening your internal network security, the next step is equipping your developers with practical, real-world security skills.
Take the next step: Join the Secure Coding Practices Bootcamp. Learn how to build safer software from the ground up through hands-on labs, OWASP Top 10 training, secure authentication, encryption, and more. Perfect for individuals or teams, includes live sessions, replays, cheatsheets, and a certificate.
References
- https://www.securityweek.com/cost-of-data-breach-in-us-rises-to-10-22-million-says-latest-ibm-report/
- https://www.sans.org/white-papers/zero-trust-segmentation

