
Trust relationships define which systems can access which resources, and under what conditions. In our secure development bootcamp, we see teams struggle not with the handshake itself, but with everything that happens after. We’ve watched devs wire up access between domains, partner apps, and shared services, only to forget those connections exist six months later.
That’s where risk creeps in. A trust link isn’t just a checkbox, it’s a living part of the environment that needs review, pruning, and sometimes, hard resets. Keep reading to see how we design, test, and maintain these trusts in real projects.
Key Takeaways
- Trust is built on clear policies and secure coding from the start.
- Continuous monitoring is more critical than the initial setup.
- Regular, scheduled reviews prevent trust from becoming a liability.
The Foundation is Everything
We often see teams rush to establish connections between systems. The pressure to enable collaboration is high. But the most secure trust relationships are built on a foundation of deliberate, thoughtful policy. Before a single line of code is written, you need to ask: What is the specific purpose of this trust? What resources need to be shared, and who truly needs access?
Answering these questions defines the trust boundary. This is the invisible line that separates the trusted from the untrusted, a concept that becomes clearer when you look at trust boundaries and how they shape secure interactions. A well-defined boundary makes every subsequent decision easier.
It informs the direction of trust, should it be one-way or two-way? It dictates the level of authentication required. Skipping this step is like building a house on sand. The structure might go up quickly, but it won’t withstand the first storm.
Secure coding practices are the bricks and mortar of this foundation. We write code that assumes nothing, that validates everything. This means rigorously checking all credentials presented at the trust boundary. It means implementing proper error handling so that a failed authentication doesn’t leak sensitive system information. This initial diligence pays off exponentially in reduced vulnerabilities down the line.
- Start with a clear policy defining the “why” and “what” of the trust.
- Explicitly map out the trust boundary before technical implementation.
- Code for the worst-case scenario, validating every input and request.
The Unseen Work of Verification
Establishing the trust relationship is just the opening act. The real, ongoing work is verification. Credentials and authorizations aren’t static. People change roles, systems are updated, and partnerships evolve. A trust relationship that isn’t actively verified is like a door left unlocked. It might be fine for a while, but eventually, it will be found.
This is where a robust identity and access management (IAM) strategy becomes essential. Think of it as the active security detail for your trust relationships. It’s not enough to just have a list of who should have access. You need to constantly check that the person or system requesting access is who they claim to be, and that they are still authorized for what they’re asking.
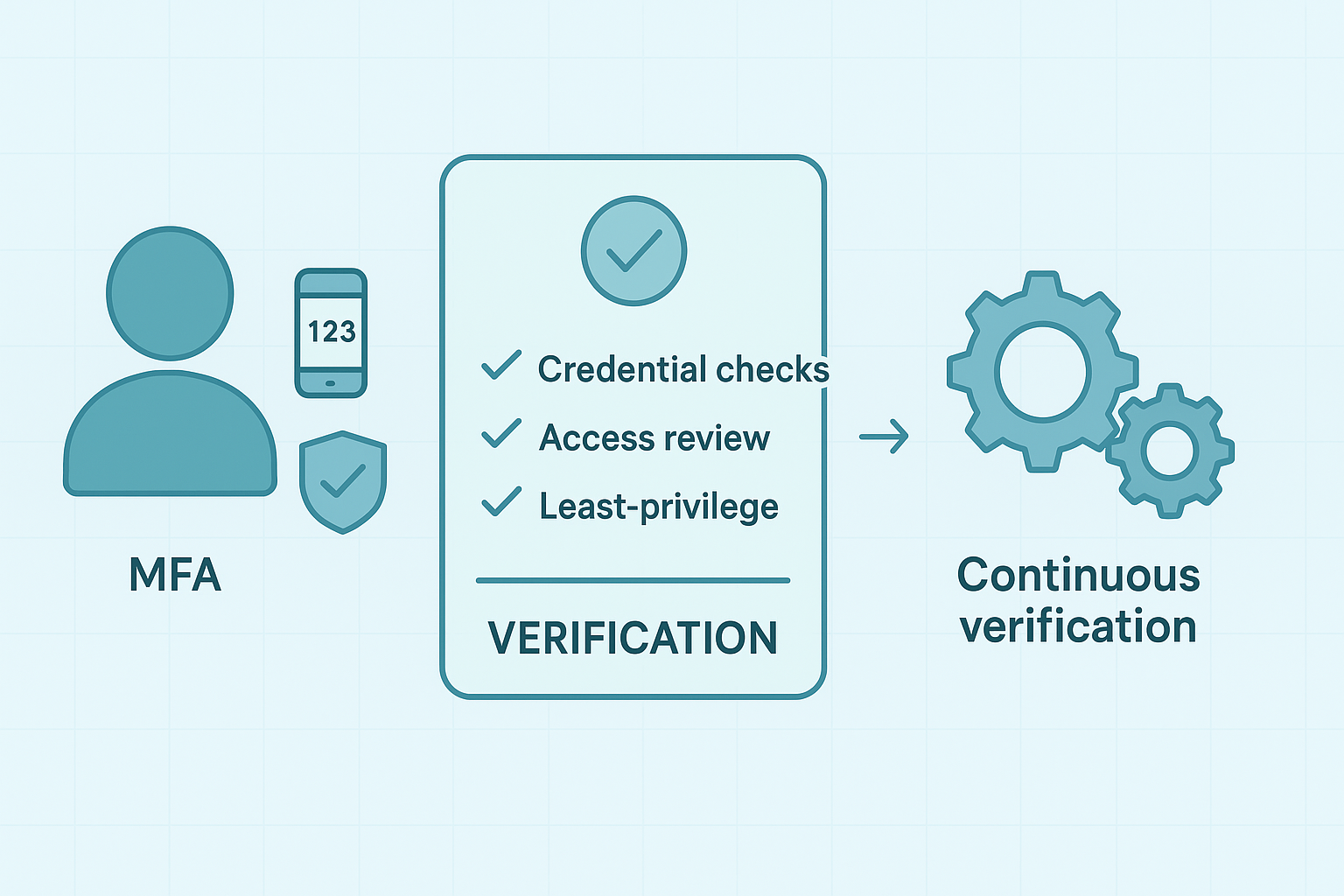
Multi-factor authentication (MFA) is a cornerstone here. It adds a critical layer of certainty to the verification process. But even with MFA, permissions can bloat over time. Regular audits of access rights are non-negotiable. This isn’t about mistrusting your users. It’s about adhering to the principle of least privilege, giving users only the access they absolutely need to perform their jobs. This minimizes the damage if a credential is ever compromised.
Automation is your best friend in verification. Manual processes are slow, prone to error, and difficult to scale. Automating credential checks and access reviews ensures consistency. It frees up your team to focus on more complex security tasks instead of routine validation.
The goal is to make verification a seamless, continuous background process, not a periodic, disruptive event. According to NIST Digital Identity Guidelines, organizations should continuously validate identities and authorization levels to maintain long-term trust across system boundaries. (1)
Listening to the Whisper of Anomalies
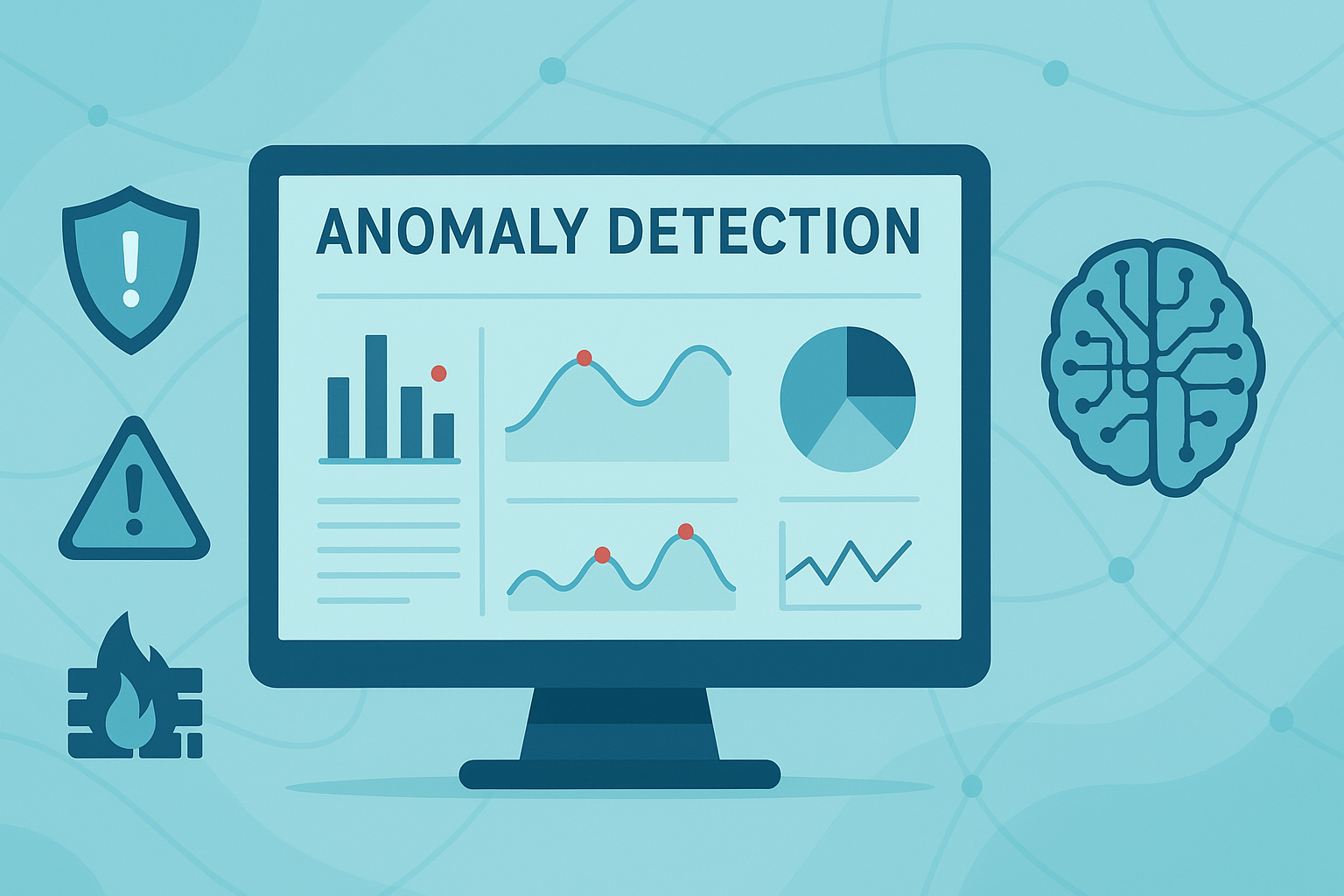
A healthy trust relationship system has a certain rhythm. You can see it in the network traffic, the log-in patterns, the types of requests being made. The key to security is learning that rhythm so you can hear when it changes. Monitoring means detecting unusual patterns in network behavior.
Intrusion detection systems help identify known malicious patterns. They listen for known patterns of malicious activity. But modern threats are sophisticated. They often don’t trip standard alarms. Behavioral analytics helps define normal activity. AI tools can flag deviations that may indicate threats.
They learn the normal “behavior” of your trust relationships and can flag subtle anomalies, like a user accessing a resource at 3 a.m. from a foreign country when they usually work 9-to-5 locally. CISA emphasizes that effective anomaly detection depends on establishing a clear baseline of normal activity, making deviations easier to spot before they escalate into systemwide issues. (2)
Security logs record all events across your trust boundaries. They contain the story of every interaction across your trust boundaries, especially when unusual patterns hint at weak boundary crossings that need closer attention.
The problem is, these books are often massive and written in a technical language. Regularly reviewing them is crucial, but it can be overwhelming. The trick is to focus on key events: failed authentication attempts, changes to trust policies, and unusual spikes in traffic. These are the chapters most likely to contain critical plot twists.
The monitoring process is useless without a clear response plan. What happens when an anomaly is detected? Who is alerted? What are the steps to contain a potential threat? Having a practiced incident response plan turns a moment of panic into a coordinated action. It’s the difference between containing a small fire and watching the whole building burn down.
Trust is a Living Agreement

Perhaps the biggest mistake is treating a trust relationship as a “set it and forget it” configuration. Organizations are not static. A trust relationship established during a merger might become obsolete after restructuring. A partnership with one company might expand to include others. Trust must be a living agreement, adaptable to the changing landscape.
This means scheduling regular reviews of all trust policies. Not just when there’s a problem, but as a matter of routine, similar to how ongoing boundary management keeps system permissions aligned with real-world changes.
These reviews should ask hard questions. Is this trust relationship still necessary? Does the scope of access still align with its original purpose? Have new risks emerged that we need to address? This proactive approach prevents trust from accumulating like digital clutter, each piece representing a potential vulnerability.
Documentation is the memory of your trust management. Every change, every review, every incident should be recorded. This isn’t just for auditors, though that is a benefit. It’s for your own team. When a problem arises six months from now, good documentation will tell you the complete history of that trust relationship. It provides context that is otherwise lost to time and personnel changes.
When a trust relationship is no longer needed, revoke it. This seems simple, but it’s often overlooked. Decommissioning trust is as important as establishing it. A forgotten trust path leaves an unintended access route into your network. Formalizing the end of a trust relationship is a critical final step in its lifecycle.
Navigating the Human Element in Trust Systems
Credits: AMTC
Technology is only one part of the equation. The human element often introduces the most significant variables into a trust model. A user might share their credentials for convenience. An administrator might grant overly broad permissions to avoid a support ticket. These actions, while well-intentioned, create gaps in your trust enforcement.
User education is not a one-time event. It’s an ongoing conversation about security. Explain the “why” behind the policies. Help users understand that multi-factor authentication isn’t just a hassle, it’s a protective shield for their own data. When people see the value, they are more likely to comply. This builds a culture where security is a shared responsibility, not just an IT mandate.
Administrators need clear guidelines too. They should have a framework for making access decisions that is aligned with the organization’s overall trust policies. This reduces ambiguity and the risk of ad-hoc, insecure configurations. A well-documented process for trust delegation ensures consistency across the board.
- Frame security policies as protective measures, not restrictions.
- Provide administrators with a clear decision-making framework.
- Celebrate secure behaviors to reinforce a positive security culture.
When Trust Breaks: Planning for Resilience
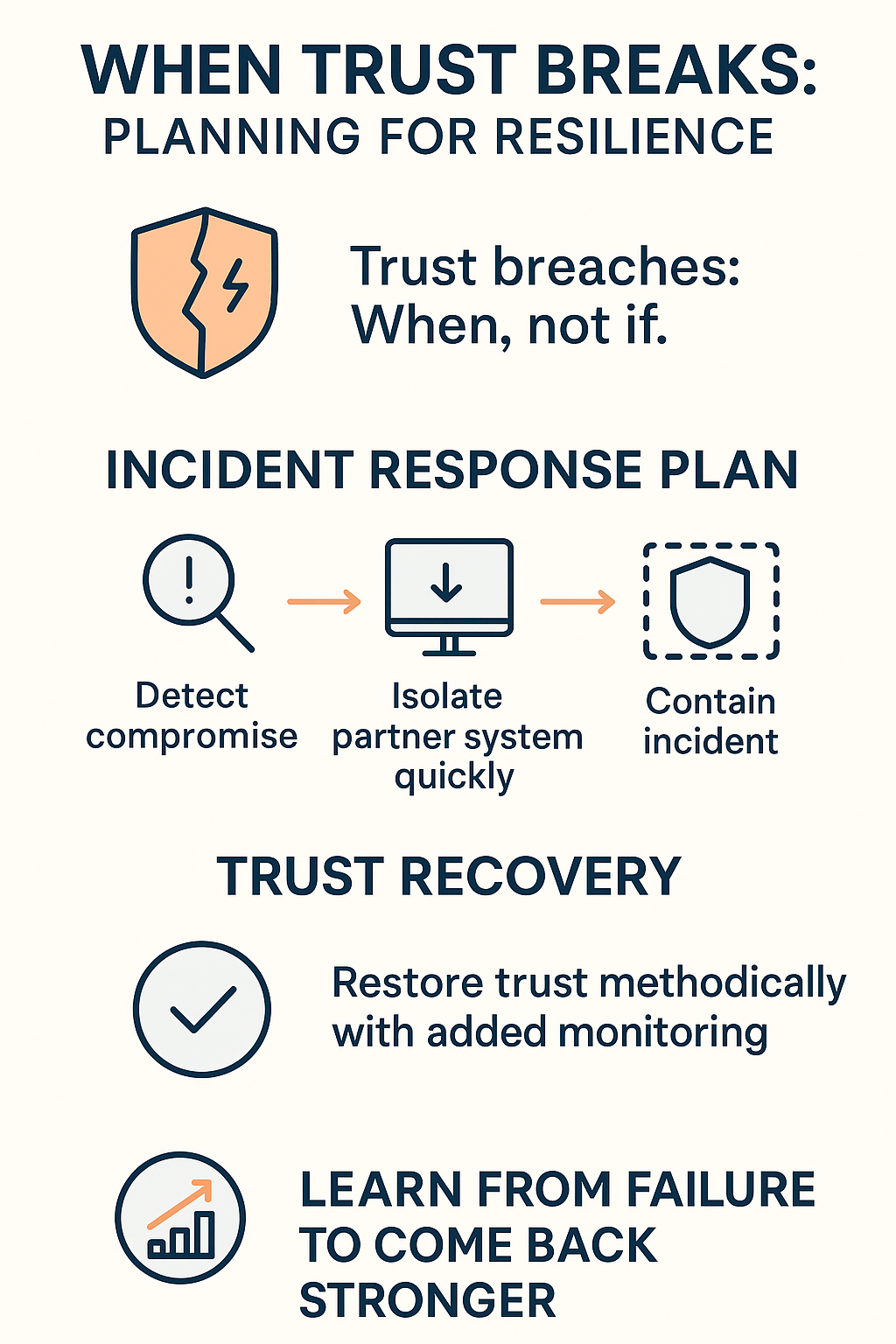
No system is perfect. A trust breach is a matter of “when,” not “if.” The true test of your trust management isn’t preventing every single incident, it’s how you respond when one occurs. A robust trust framework includes plans for trust revocation and recovery.
Your incident response plan must specifically address trust relationships. What is the immediate action if a trusted partner’s system is compromised? How do you quickly isolate that connection without causing widespread disruption? Having predefined playbooks for these scenarios cuts down response time from hours to minutes. It’s the difference between a contained incident and a full-scale breach.
Trust recovery is the final, often overlooked, phase. After a breach is contained, how do you carefully restore the necessary trust? This isn’t about flipping a switch back on. It’s a methodical process of re-establishing the relationship with enhanced scrutiny, perhaps with temporary additional monitoring. The goal is to return to normal operations without reintroducing the vulnerability. A resilient system learns from failure and comes back stronger.
FAQ
How can I understand trust relationships when systems talk to each other?
Trust relationships help systems decide who can see or use something. They depend on trust management basics like authentication, authorization, and trust policies. A clear trust model or trust framework shows how trust flows. When you map each trust boundary and trust domain, you spot weak areas early and make access control easier for everyone to follow.
What should I look for when checking trust negotiation in my setup?
Trust negotiation means two sides share just enough information to work together. You can use credential management and simple trust negotiation strategies to keep things safe. Watch for trust vulnerabilities or trust risks, and use trust validation steps to confirm claims. Good trust evaluation habits make every trust agreement smoother and less stressful.
How do I keep trust lifecycle tasks from getting messy over time?
Trust runs in cycles: trust establishment, trust monitoring, trust revocation, and trust recovery. Using clear trust metrics helps you judge trustworthiness. Simple trust auditing habits catch small problems early. Trust enforcement tools also help you spot broken trust relationships. When you track trust relationship types, you keep trust computation and trust scoring from piling up.
What signs show that my trust infrastructure needs improvement?
If secure communication feels slow or trust propagation breaks, your trust infrastructure may need work. Look for trust attacks or any trust breach hints. In big systems with federated identity or single sign-on, even small issues can spread fast. Strong trust governance and trust compliance practices keep trust architecture steady and easy to update.
How do I fix trust relationship vulnerabilities without breaking everything?
Start with a simple trust assessment to locate weak spots. Focus on trust verification, trust enforcement, and trust protocol checks. In setups with distributed trust or decentralized trust, issues can jump across systems. Use trust restoration steps after changes, and make sure your trust policy management rules stay clear so trust relationship management remains stable.
Conclusion
So where do you start if this feels overwhelming. You don’t need to boil the ocean. Begin with a single, critical trust relationship in your environment. Map its boundary. Review its policies. Check its access rights. Document everything you find. This single exercise will give you a template, a rhythm, for tackling the next one.
The tools you use should reduce complexity, not add to it. Whether it’s an IAM platform or a simple scripting tool for audits, the goal is the same: to enforce your policies consistently and free up human intelligence for higher-level tasks. The best tool is the one your team will actually use effectively.
Ultimately, managing trust relationships is about building a culture of mindful security. It’s a continuous practice of verification, observation, and adaptation. It’s acknowledging that trust in a system is not blind faith, but a carefully measured and constantly reaffirmed agreement.
Your next step. Pick one trust relationship in your system;
- Map the trust boundary,
- Verify access rights,
- Check MFA,
- Log review,
- Document findings.
Choose the one that worries you the most and schedule a 30-minute review this week. Just one. That’s how you build momentum, and start sleeping better.
Want structured training to reinforce this mindset? Join the Secure Coding Practices Bootcamp
The Secure Coding Practices Bootcamp trains developers to build secure software through hands-on, real-world coding sessions, no security jargon, just practical skills. Designed by experts and tailored for developers, it covers essentials like the OWASP Top 10, input validation, secure authentication, encryption, and safe dependency use. Offered live (online or in-person), the 2-day course includes labs, replays, cheatsheets, and a certificate. Perfect for teams or individuals (with corporate options and volume discounts), it equips developers to ship safer code from day one.
References
- https://csrc.nist.gov/publications/detail/sp/800-63/3/final
- https://www.cisa.gov/secure-by-design

