
If you build software for the European market, cybersecurity is no longer optional, it’s part of a strict legal and regulatory framework. The EU now enforces layered cybersecurity requirements that affect how software is designed, developed, and maintained.
Frameworks like the Cyber Resilience Act and NIS2 Directive make security a formal legal compliance obligation. From our experience, starting early helps reduce regulatory risk, improve operational efficiency, and avoid costly compliance failures.
Key Insights on EU Cybersecurity Law
Before diving deeper, here are the essentials:
- EU cybersecurity law for software is built from multiple legal and regulatory instruments
- Understanding cyber resilience act vs nis2 is key to managing product and organizational obligations
- Secure software development eu law connects directly to compliance, not just best practice
EU Cybersecurity Law for Software
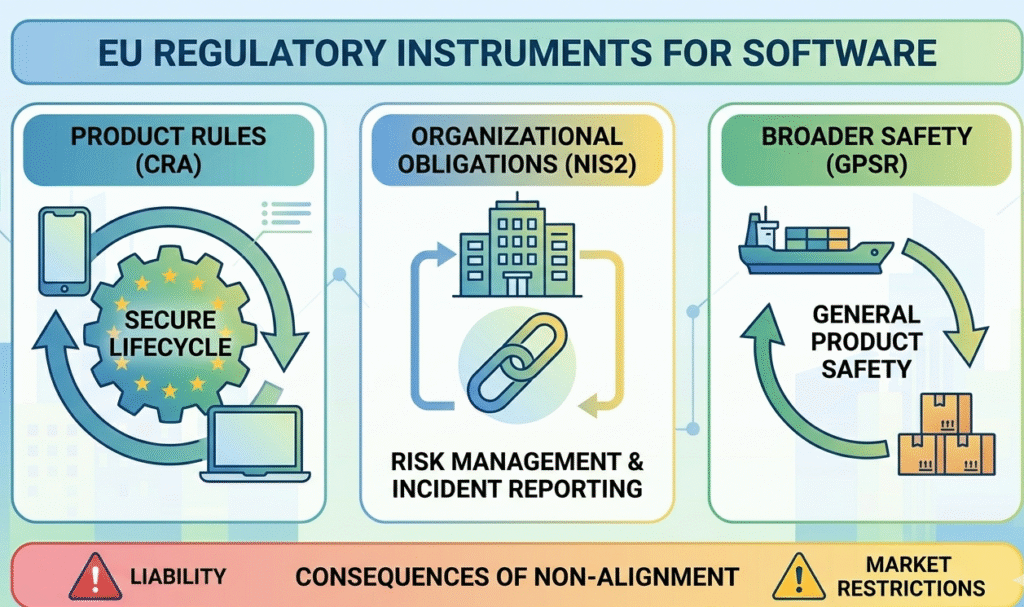
The eu cybersecurity law for software is not a single regulation. It is a combination of legal requirements that shape how organizations approach regulation and compliance.
It includes:
- Product-focused rules under the Cyber Resilience Act (CRA)
- Organizational obligations under the NIS2 Directive
- Broader safety rules under the General Product Safety Regulation
“Products with digital components … are made secure throughout the supply chain and throughout their lifecycle.” – Council of the European Union
These create a complex regulatory environment where engineering teams, governance structures, and senior management must align. Without alignment, companies face civil liability, compliance failures, and limited access to markets.
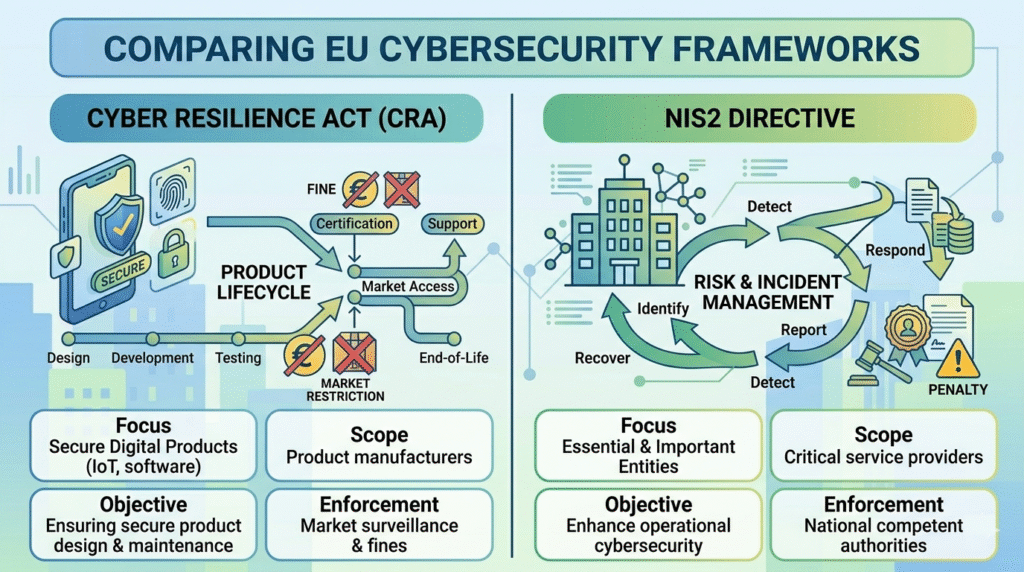
Cyber Resilience Act vs NIS2
Credits: Somco Software
Understanding cyber resilience act vs nis2 helps clarify responsibilities.
| Aspect | Cyber Resilience Act | NIS2 Directive |
| Focus | Digital products & software | Organizations & services |
| Scope | Manufacturers, developers | Operators, providers |
| Objective | Secure lifecycle | Risk & incident management |
| Enforcement | Market fines | National penalties |
In practice:
- CRA affects product design, requirements engineering, and lifecycle security
- NIS2 drives internal policies, reporting, and board-level accountability
Together, they form a complete legal and regulatory system.
EU Product Security Legislation Overview
A clear eu product security legislation overview shows how cybersecurity fits into broader legal and regulatory instruments.
Key components include:
- Cybersecurity obligations under CRA
- Product safety requirements under the General Product Safety Regulation
- Policy direction from EU institutions
These frameworks also connect with data privacy, international trade laws, and Environmental & ESG Regulation. Organizations that align early reduce regulatory risk and adapt faster to legislative change.
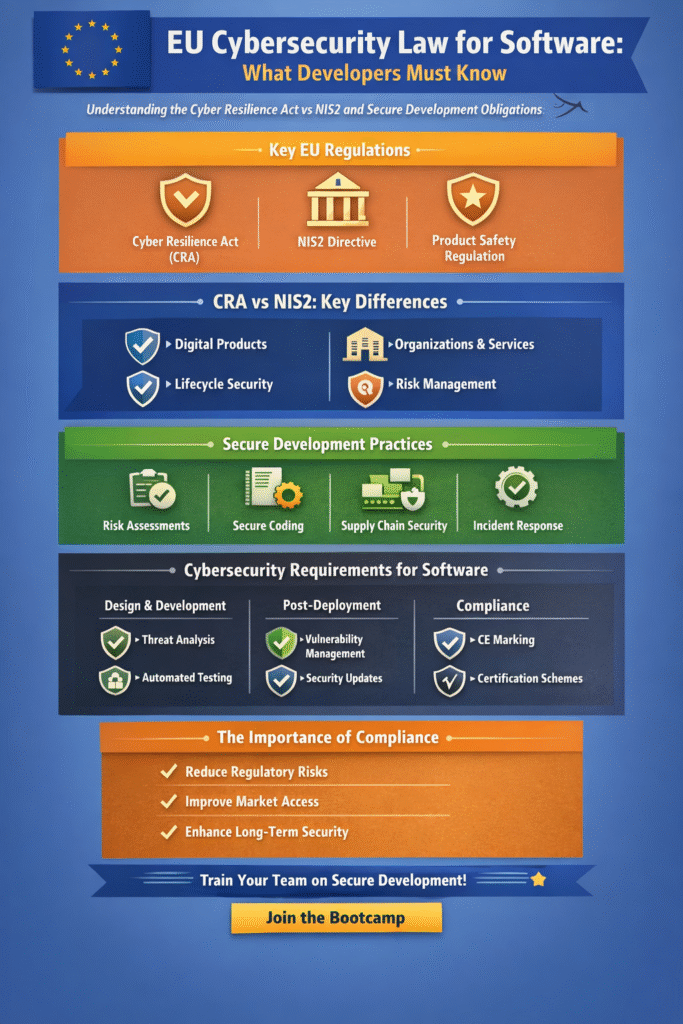
Secure Software Development EU Law
Under secure software development eu law, security must be embedded into the entire development lifecycle.
“Ensure that manufacturers improve the security of products … throughout the whole life cycle.” – European Commission
Teams should:
- Conduct cyber security impact assessment early
- Establish secure operating procedures
- Prepare for personal data breach scenarios
- Protect intellectual property rights
Secure development now includes compliance checking, identity management systems, and documentation aligned with legal authority. It is no longer optional—it is required for regulatory compliance and long-term sustainability.
Cybersecurity Requirements for Software EU
The cybersecurity requirements for software eu apply across all stages:
Design Phase
- Risk modeling and threat analysis
- Secure architecture planning
Development Phase
- Automated testing and dependency checks
- Supply chain visibility
Post-Deployment
- Continuous updates and vulnerability management
- Monitoring using identifiers like IP Address
Compliance Layer
- Documentation aligned with compliance criteria
- Alignment with global frameworks like FATF recommendations
Integrating these requirements strengthens both security and corporate reputation.
Why Legal & Regulatory Context Matters
The legal and regulatory context defines how software is built, secured, and maintained in the EU. It impacts:
- Business environment and access to markets
- Corporate reputation and compliance strategies
- Governance structures and operational efficiency
Ignoring these factors increases regulatory risk and can lead to enforcement actions or loss of market access.
FAQ
What are the key cybersecurity requirements under the EU Cyber Resilience Act?
The Cyber Resilience Act sets cybersecurity requirements for digital products and Products with Digital Elements across the European Union. It requires secure design, risk assessment, vulnerability handling, and regular security updates. Software developers must consider the full product lifecycle, including supply chains.
Compliance includes CE marking, incident response readiness, and alignment with standards for securing digital products.
How does the Cyber Resilience Act differ from the NIS2 Directive?
The NIS2 Directive focuses on organizational security across Member States, while the EU Cyber Resilience Act targets cybersecurity requirements for digital products. NIS2 applies to operators and managed security services, emphasizing incident response and reporting.
In contrast, the Cyber Resilience Act regulates software developers, hardware products, and ICT supply chain security from design to deployment.
What role does certification play in EU cybersecurity compliance?
The EU Cybersecurity Act introduces a cybersecurity certification framework with certification schemes and EU certification schemes. These help verify compliance with cybersecurity requirements and build digital trust.
Certification schemes may include Common Criteria or ENISA cybersecurity certification. Cybersecurity certification authorities and market surveillance authorities ensure products meet European product legislation and security expectations.
How should software developers manage cybersecurity risks in digital products?
Software developers must integrate cybersecurity into the product lifecycle, focusing on IoT security, secure coding, and software supply chain protection. This includes penetration testing, security audits, and Threat-Led Penetration Testing to address cyber threats like DDoS attacks and business email compromise.
Developers must also implement vulnerability management services, incident response processes, and ensure continuous security updates.
Navigating EU Cybersecurity Law for Software
EU cybersecurity law for software makes security a core part of development, not an afterthought. By understanding the Cyber Resilience Act vs NIS2 and applying secure software development practices aligned with EU law, teams can meet cybersecurity requirements more effectively.
From our experience, integrating compliance early helps reduce risks, improve efficiency, and ensures your software remains competitive and compliant in the European market. Ready to build secure, compliant software from day one? Join the Secure Coding Practices Bootcamp.
References
- https://www.consilium.europa.eu/en/press/press-releases/2024/10/10/cyber-resilience-act-council-adopts-new-law-on-security-requirements-for-digital-products/
- https://digital-strategy.ec.europa.eu/en/library/cyber-resilience-act

