
If you build digital products or products with digital elements for the European Union, cybersecurity is no longer optional. The EU Cyber compliance basics developers Act introduces strict cybersecurity requirements that require developers to integrate security into every stage of the software lifecycle, from design to deployment and ongoing maintenance.
We’ve seen how applying secure coding practices and early cybersecurity risk assessment helps reduce security vulnerabilities, improve product security, and simplify compliance across the regulatory landscape.
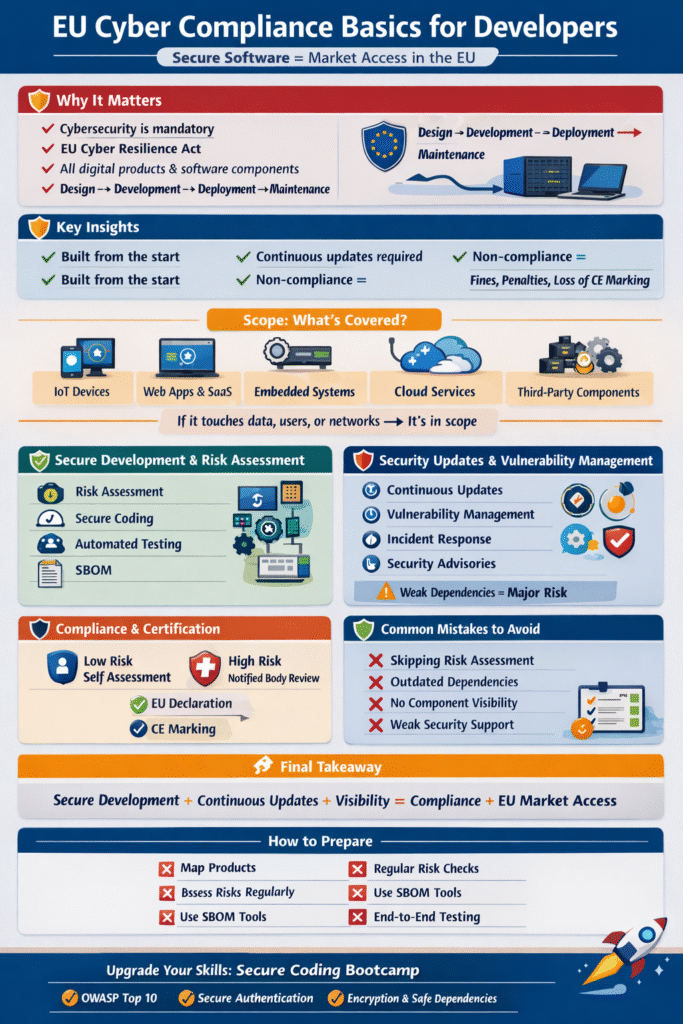
Key Insights on EU Cyber Compliance for Developers
Here’s a quick overview of what developers must focus on to stay compliant and build secure software:
- Security must be integrated into all products with digital elements from the start
- Continuous security updates and vulnerability handling are mandatory
- Poor compliance can lead to market surveillance actions, fines, or loss of CE marking
Scope: What Developers Are Responsible For
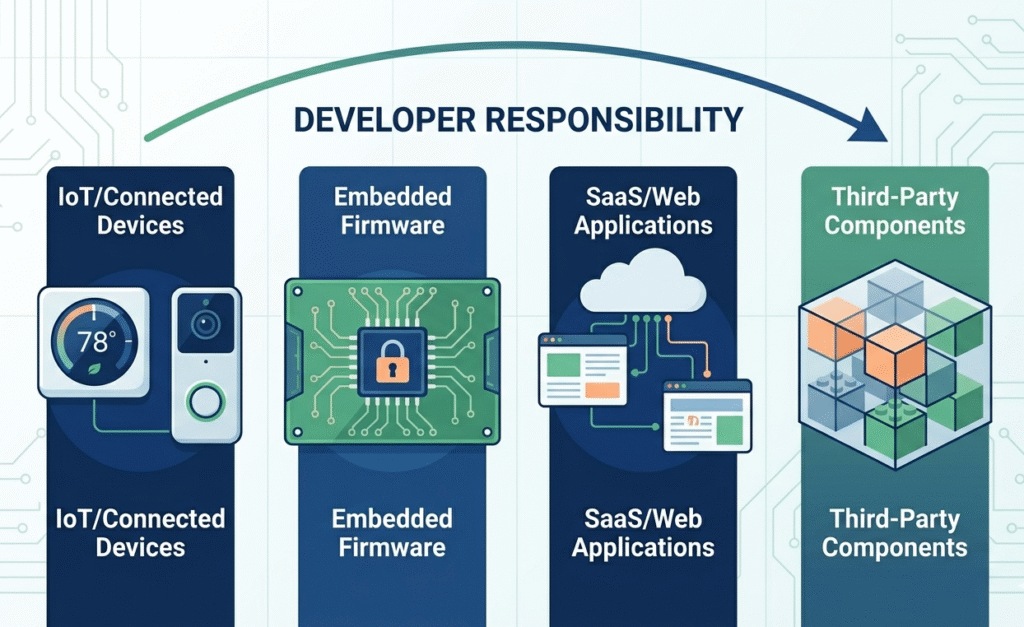
Visual showing scope of EU cyber compliance across software, IoT, and cloud platforms.
If you’re a developer, determining who must comply with the Cyber Resilience Act is essential, as your work likely falls under these rules if it involves:
- IoT devices and other connected devices
- Embedded systems and firmware
- Web applications and SaaS software
- Non-embedded software and backend services
- Software components and third-party dependencies
Anything interacting with users, data, or networks is exposed to cyber threats and falls within the scope and applicability of European cybersecurity regulations.
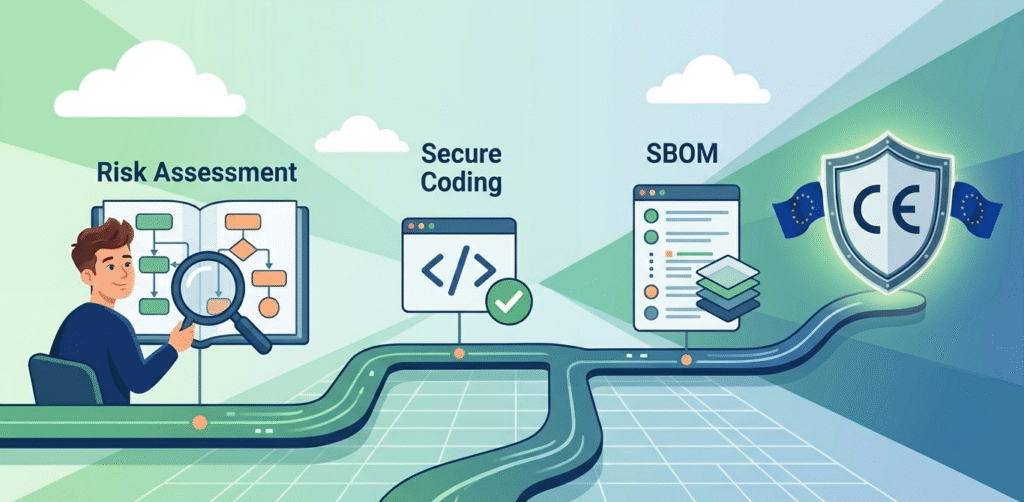
Secure Development and Risk Assessment
The foundation of compliance starts with strong software development practices:
- Conduct a cybersecurity risk assessment to identify attack surfaces
- Apply secure coding to reduce security vulnerabilities
- Use automated security testing, SCA scan, and scanning techniques
- Maintain a software bill of materials (SBOM) for transparency
“The cybersecurity risk assessment shall be documented and updated as appropriate during a support period… [it] shall comprise at least an analysis of cybersecurity risks based on the intended purpose and reasonably foreseeable use, as well as the conditions of use.” – European Union
These steps support Developing Secure Software principles and reduce risks across the software supply chain.
Security Updates and Vulnerability Management
Credits: Somco Software
Visual showing update cycles and incident response workflow.
Security doesn’t stop after release. Developers must ensure:
- Continuous security updates throughout the software lifecycle
- Strong vulnerability management processes
- Timely incident reporting for critical issues
- Clear security advisories and security documentation
Working with Product Security Incident Response Teams improves response speed and ensures compliance with EU expectations.
Supply Chain Security and Dependencies
Infographic showing software supply chain and third-party risks.
“The CRA’s technical documentation expectations include software composition visibility and vulnerability handling information; in practice, this strengthens the role of SBOM-like evidence in conformity and market surveillance contexts.” – ResearchGate
Modern applications rely heavily on external components. Developers must:
- Monitor third-party software and open source software
- Track software supply chain risks and supply-chain vulnerabilities
- Maintain visibility across cloud platforms and integrations
Strong supply chain security and supply chain transparency reduce exposure to hidden vulnerabilities.
Conformity Assessment and Certification
Not all products follow the same compliance path:
- Lower-risk products: internal conformity assessment
- Higher-risk systems: review by a notified body
You must prepare:
- EU declaration of conformity
- Proper security documentation
- Evidence aligned with harmonised standard requirements
Achieving the CE mark (Conformité Européenne) proves your product meets EU standards and is ready for the European Economic Area.
Regulatory Landscape and Related Frameworks
EU cyber compliance connects with broader EU legislations, including:
- NIS2 Directive
- Cybersecurity Strategy
- Guidance from the European Parliament and market surveillance authorities
These frameworks shape how organizations manage cybersecurity risks, enforce market surveillance, and respond to evolving threats.
Common Risks Developers Should Avoid
Here are frequent mistakes that lead to non-compliance:
- Ignoring cybersecurity risk assessment early in development
- Using outdated third-party dependencies
- Lacking visibility into software components
- Failing to maintain proper security support
These gaps increase exposure to cyber threats and may trigger penalties under European cybersecurity regulations.
Preparing for Compliance
Timeline visual showing preparation and compliance milestones.
To prepare effectively:
- Build a clear device inventory and map all products with digital elements
- Perform regular firmware security analysis and runtime protection checks
- Use tools like SBOM managers for software supply chain visibility
- Conduct end-to-end testing across lifecycle stages
Early preparation simplifies audits and ensures readiness by understanding exactly when the Cyber Resilience Act applies to your specific product lifecycle under Regulation 2024/2847.
FAQ
How can developers reduce cybersecurity risks in digital products early?
Developers should start with a cybersecurity risk assessment, identifying attack surfaces and potential security vulnerabilities. Using automated security testing, SCA scan, and secure coding practices helps prevent issues early.
Maintaining a software bill of materials improves visibility across software components and supports better vulnerability management throughout the software lifecycle.
What role does the software supply chain play in compliance?
The software supply chain includes third-party dependencies, open source software, and integrations. Weaknesses here create supply-chain vulnerabilities and increase exposure to cyber threats.
Developers must ensure supply chain security, track dependencies, and maintain supply chain transparency to meet EU cybersecurity requirements and avoid hidden risks.
How do developers handle vulnerability management effectively?
Effective vulnerability management involves continuous monitoring, timely fixes, and clear security advisories. Developers should collaborate with Product Security Incident Response Teams and maintain proper security documentation.
Regular updates and testing reduce risks and ensure compliance with EU Cyber Resilience Act obligations related to incident reporting and security updates.
What documentation is required for EU cyber compliance?
Developers must prepare security documentation, a software bill of materials, and technical files for conformity assessment. This includes evidence of cybersecurity risk assessment, testing results, and compliance with harmonised standard requirements. These documents support the EU declaration of conformity and are essential for obtaining CE marking.
Preparing Your Product Portfolio
Start now: map your digital products against EU requirements, assess risks, and review your software supply chain. Integrating secure development, vulnerability management, and continuous updates ensures your products remain compliant, secure, and competitive in the European Economic Area.
To upskill your team, explore the Secure Coding Practices Bootcamp, a practical 2-day training covering OWASP Top 10, input validation, secure authentication, encryption, and safe dependency use, helping developers build secure, compliant software from day one.
References
- eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:32024R2847
- https://www.researchgate.net/publication/403513884_The_Cyber_Resilience_Act_as_an_Engineering_Decision_Framework_for_IT-OT_Systems

