Trust boundaries in data flow diagrams mark where data shifts between areas with different security levels. These crossing points? That’s where attackers probe. When you map these boundaries, your team spots dangerous paths, locks down access, and closes gaps before someone finds them.
Most breaches happen at these handoff points because nobody thought them through carefully enough. Your system’s actual security depends on whether you’ve mapped these transitions or just hoped nothing breaks. The rest of this piece shows how to do it right.
Key Takeaways
- Trust boundaries identify where trust levels change in data flows, exposing possible security risks.
- Including trust boundaries in DFDs helps focus threat modeling and security controls effectively.
- Properly marked trust zones reduce vulnerabilities by clarifying where validation and authentication matter most.
What Are Data Flow Diagrams (DFDs)?
Data flow diagrams work like maps. They show how information moves through a system, what processes touch it, where it sits stored, and which outside players connect in. When we build these diagrams, we’re essentially drawing out the data’s complete journey, entry point to storage to exit.
The symbols matter here. Circles or rounded rectangles represent processes, where work happens on the data. Open rectangles show us where data lives at rest: databases, files, caches. Squares become external entities, those users or outside systems poking at our application. Arrows tie it together, showing which direction data flows.
We’ve found DFDs simplify things that seem impossible to understand otherwise. They break down what looks like chaos into pieces our teams can actually work with. That visualization piece? Crucial for spotting how different parts of a system talk to each other. Our experience tells us that when developers and security folks sit down with a DFD, suddenly weak points jump out that nobody caught before.[1]
What Are Trust Boundaries?
Think of trust boundaries as invisible fences running through your system. Proper defining and managing trust boundaries makes these lines explicit, marking where data crosses from trusted zones into less trusted ones. These lines help us know exactly where security needs to get strict.
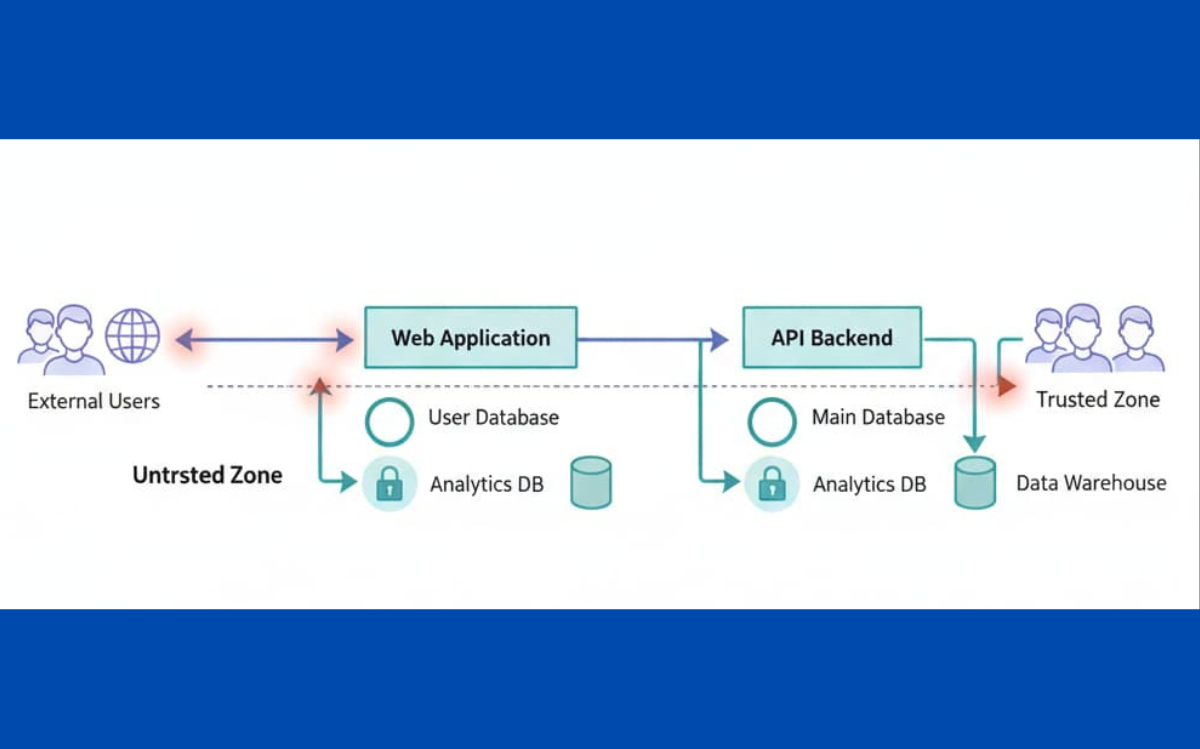
On our diagrams, trust boundaries show up as dotted lines or rectangles that separate different trust zones. When data moves from an external user through the internet into an internal system, that’s a boundary crossing. The same thing happens when two microservices with different security setups talk to each other. Our teams represent them visually because it keeps everyone focused on the right spots.
What makes them powerful is they act as control points. Each time data crosses one of these lines, we might need validation, authentication, maybe encryption. We’ve noticed that once you start mapping these out, the entire team’s thinking shifts about what’s actually risky in their code.
Why Trust Boundaries Matter for Security
Credits: Gus Nonie
Without clearly identifying what are trust boundaries security, gaps appear where attackers hunt. An attacker exploits weak input validation right where data moves from a user interface (untrusted space) into backend processing (trusted space). Or they target microservices communicating over channels we thought were secure but really weren’t.
When we include trust boundaries in our DFDs, our security teams gain real advantages:
- We can pinpoint exactly where secure coding practices need to apply.
- Threat modeling focuses on actual critical crossing points instead of everywhere.
- We know precisely where access control enforcement matters most.
- The diagram shows us how privilege levels shift as data moves through systems.
On a recent project we worked with, marking trust boundaries revealed something our team had missed, a gap between cloud services and systems running on-site. That one diagram caught a risk we might’ve discovered only after breach. We implemented stronger authentication and layered encryption after that, and the attack surface shrank noticeably.
Examples of Trust Boundaries in Systems
Our systems tend to have these trust boundaries show up repeatedly:
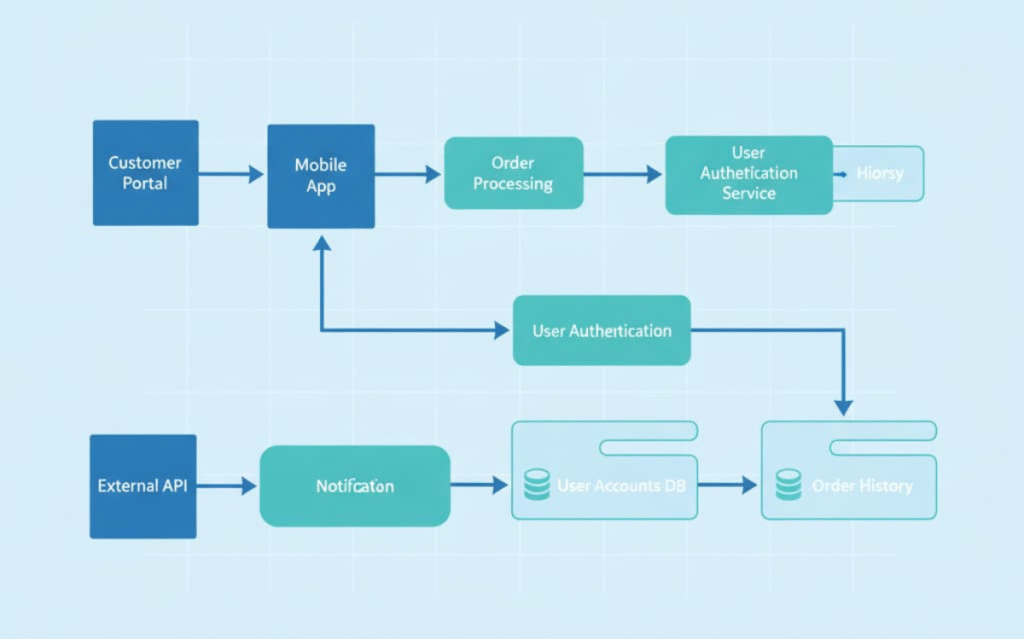
Data crossing from external users into a web application’s front end. Communication between microservices where each has different security requirements. Boundaries separating cloud infrastructure from networks we run ourselves.
Front-end inputs moving into backend processing logic. Firewalls filtering traffic between network zones. API endpoints where untrusted client requests meet trusted service code. Access level shifts that define who can do what.
Each one marks a point where data needs careful handling. We’ve learned that naming these explicitly, writing them down on diagrams, keeps our teams remembering where validation happens, where we authenticate, where we encrypt. When developers see these boundaries during code review, they catch problems earlier.[2]
How Trust Boundaries Help with Threat Modeling
Threat modeling tries to catch security problems before they cause damage. Trust boundaries provide the roadmap, showing exactly where data moves between zones of different trust levels.
When identifying trust boundaries application architecture, our teams gain structure:
- We visualize how data enters and leaves the system.
- Attack surfaces become visible, places where someone might breach into trusted areas.
- Security controls get placed where they actually matter.
- Privilege escalation paths show themselves on the diagram.
Our threat modeling sessions changed once we started using trust boundaries. Instead of circling around vague concerns, we’d point at specific boundary crossings and ask: “How do we validate here? What monitors this line?” Input validation at boundaries, monitoring data movement, these became concrete actions rather than general good intentions.
Practical Uses of DFDs with Trust Boundaries
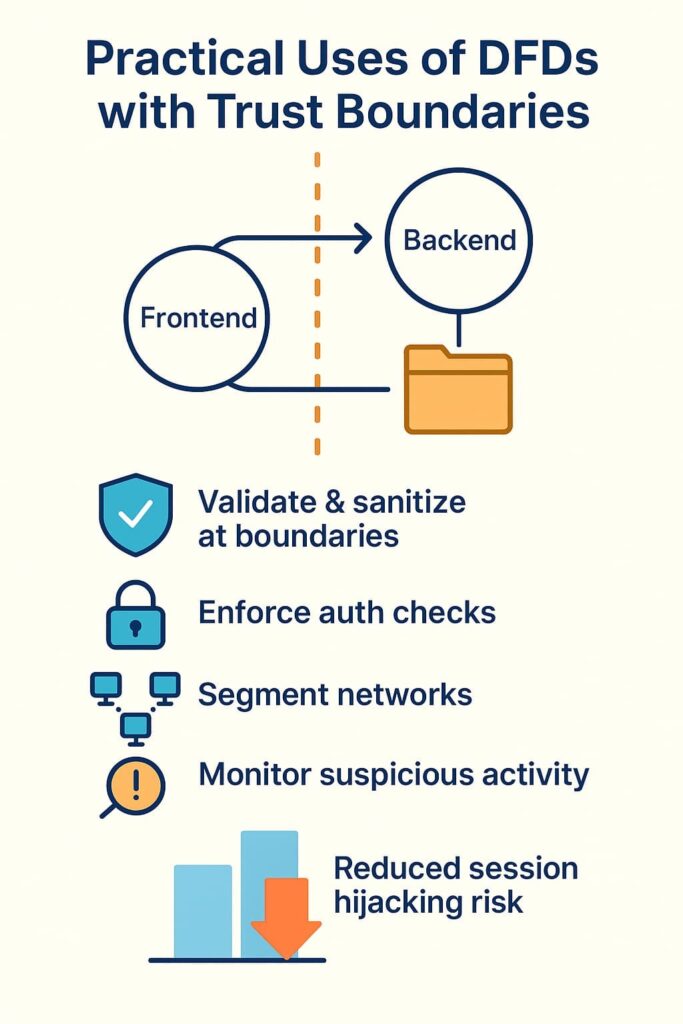
The real value shows up when teams stop treating DFDs as boxes to check and start using them to build better defenses.
Here’s what happens in practice:
- Find components handling sensitive data as it crosses trust zones.
- Write code that enforces validation and sanitization at those exact points.
- Build authentication and authorization checks right at boundary crossings.
- Segment networks to isolate trust zones, either physically or logically.
- Set up monitoring to catch suspicious activity crossing those boundaries.
One project we worked on involved separating frontend applications from backend APIs with a clear trust boundary. That single line on the diagram forced us to think harder about session management and token validation. Session hijacking risks dropped noticeably after we implemented controls at that boundary.
Benefits of Adding Trust Boundaries to DFDs
The reasons matter here. Mapping trust boundaries isn’t busywork—it changes how your team builds security.
| Benefit | What It Means |
| Enhanced Security Visualization | You see exactly where trust shifts happen. |
| Targeted Security Controls | Protections go where they’re needed, not scattered everywhere. |
| Improved Threat Modeling | Your team focuses on actual risks instead of guessing. |
| Reduced Vulnerabilities | Fewer openings for attackers to exploit. |
Drawing lines on diagrams sounds simple. But those lines force decisions about where your actual defenses belong.
How to Implement Trust Boundaries: Step-by-Step
Adding trust boundaries works best when your team follows a clear path:
- List every component and trace how data moves through them.
- Assign trust levels to each part (trusted, untrusted, somewhere in between).
- Draw boundary lines where trust levels shift on your diagram.
- Analyze what could go wrong at each crossing point.
- Apply controls, input validation, authentication checks, encryption.
Our bootcamp students work through this process repeatedly because it builds muscle memory. By the third or fourth system they diagram, they start spotting boundaries before being told where they are. That’s when learning sticks.
Enhancing Security with Secure Coding Practices
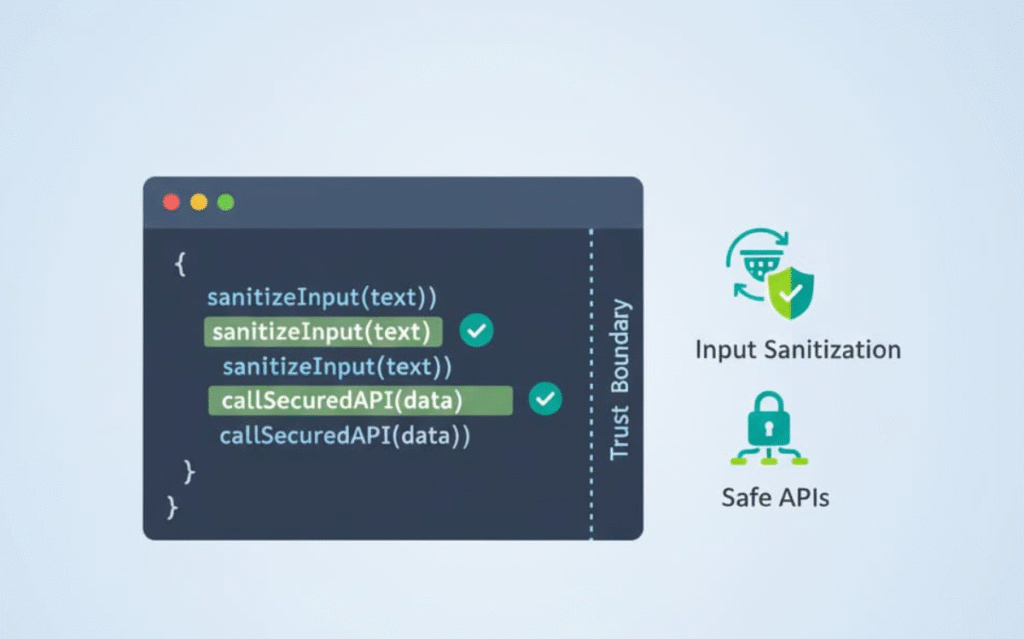
Trust boundaries show developers exactly where their code needs teeth. Secure coding practices become the enforcement mechanism at these crossing points. Input validation, proper error handling, data sanitization, these aren’t optional where boundaries exist.
When developers treat boundaries as mandatory checkpoints, secure coding stops being a list of rules and becomes part of how they think. Code that crosses a trust boundary gets scrutinized differently than code that stays within a zone. That shift in perspective matters more than any checklist ever could.
FAQ
How do data flow diagrams help people understand trust boundaries in a system?
Data flow diagrams show where data moves and where trust boundaries sit. They map DFD trust zones, trusted vs untrusted zones, and access control boundaries using trust boundary symbols and trust boundary lines. With clear data flow visualization and DFD components like processes, data stores, and data flow connectors, people can see data crossing trust zones and understand how communication trust levels shape data flow security.
What should I look for when identifying trust boundary examples inside DFD trust zones?
Look for moments where external vs internal trust shifts, like input trust boundaries, API trust boundaries, or firewall trust zones. Trust zone identification highlights data crossing trust zones in places where authentication boundaries matter. These trust boundary examples often show weak privilege boundaries, network trust levels, or unsafe data movement diagrams that reveal important data flow risk points.
How do cloud trust boundaries and microservices trust zones change a DFD?
Cloud trust boundaries, microservices trust zones, and SaaS data flows add more security zones in DFD models. You’ll see DFD process mapping across inter-service trust areas, trust zone isolation, and internal network trust versus external network untrusted connections. These data interaction flows help track trust boundary impact, especially in distributed systems where network segmentation and trusted data flow isolation are essential for data flow security.
How do trust boundaries support threat modeling diagrams and data flow risk analysis?
Threat modeling diagrams rely on DFD arrow meanings, trust enforcement points, and security boundary crossing markers. They help teams see data flow direction, user trust levels, and session trust boundaries. Using threat surface mapping and DFD and threat analysis together highlights security zones in DFD, trust zone vulnerability, and data integrity zones so teams understand where attackers target data flow risk points.
How can teams use trust boundary assessment to improve compliance and architecture design?
Teams use trust boundary assessment to strengthen security design diagrams, trust zone policy enforcement, and trust zoning best practices. With DFD for compliance, security control mapping, and trust zone documentation, they track trust zone differentiation and trust zone access control. This helps identify trust boundary attack paths, trust boundaries in distributed systems, and trust zones in hybrid cloud or zero trust and DFD environments.
Wrapping Up Trust Boundaries in Data Flow Diagrams
Trust boundaries mark where trust shifts on your diagrams. They’re not decorative lines, they show where data needs guarding and where attackers probe. When your team identifies these spots, the security picture gets clearer.
Combined with secure coding, access controls, and network segmentation, boundaries become real defenses. Mapping them carefully forces better decisions about where your actual protections belong. Your system gets stronger when you treat these boundaries as mandatory checkpoints, not afterthoughts.
If your team wants to get better at applying these principles in real code, you can build those skills through the Secure Coding Practices Bootcamp. It’s a practical, developer-focused training that teaches defensive coding through hands-on sessions, not theory. Learn more or join here: Secure Coding Practices Bootcamp
References
- https://arxiv.org/pdf/2401.04446
- https://www.infosecurity-magazine.com/news/99-organizations-report-api/

