
You look at a smart lock on your door, or the industrial sensor monitoring a city’s water supply. They seem like simple tools. But the European Union now classifies them as “high-risk” products. This isn’t bureaucratic noise, how cyber resilience act high risk products.
It’s a fundamental shift in how digital security is regulated, placing direct legal obligations on manufacturers for the entire lifecycle of their products. If you make, sell, or use connected devices in the EU, the Cyber Resilience Act (CRA) changes your rules. Let’s break down what “high-risk” really means and what you need to do next.
Understanding Cyber Resilience Act High-Risk Products
Before diving deeper, here are the essential points to understand about Cyber Resilience Act high-risk products and why they matter for manufacturers and developers in the EU.
- High-risk products are defined by function, not brand. Things like firewalls, password managers, and certain industrial control systems fall into Important or Critical classes.
- Compliance requires a “secure-by-design” approach and ongoing vulnerability management, including reporting serious bugs to ENISA within 24 hours.
- The timeline is strict. While the law is active now, the full weight of product requirements hits on December 11, 2027, with vulnerability reporting starting September 2026.
What Actually Qualifies as a “High-Risk” Product Under the CRA?
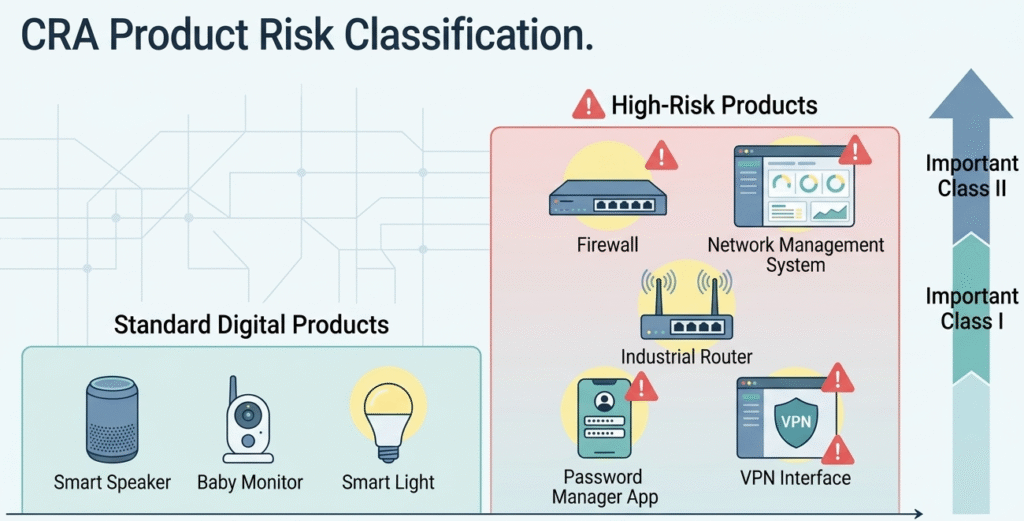
The Act doesn’t just call everything risky; rather, the scope and applicability of the law depend on a tiered system.Most digital products, about 90%, fall into the “default” category. They have obligations, but the process is simpler.
High-risk products are those in the “Important” and “Critical” classes. The classification hinges on the product’s intended function and its potential impact if compromised.
Think about it this way. A web browser or a password manager (Important Class I) is a gateway. Its failure can expose a vast amount of personal data or system access. A firewall or an intrusion detection system (Important Class II) is a barrier. Its failure can let threats into a network. The EU argues these aren’t just products; they are critical components of the digital ecosystem’s health. The rules get stricter accordingly.
Important Class I (Higher Risk):
- Web browsers
- Password managers
- Virtual Private Networks (VPNs)
- Smart locks & connected home security
- Identity management systems
Important Class II (Highest Risk):
- Firewalls
- Intrusion Detection/Prevention Systems (IDS/IPS)
- Network management systems
- Industrial routers
- Tamper-resistant microprocessors
The conformity assessment, the proof you follow the rules, differs too. For Class I, you can often self-assess if you use established harmonized standards. For Class II, you generally need a third-party assessment. It’s a more rigorous, and costly, process.
The Manufacturer’s Burden: New Obligations for High-Risk Gear
Credits: Hogan Lovells
Once a device is labeled among high-risk products, determining who must comply becomes a critical legal priority as manufacturer responsibilities grow quickly. It’s no longer just about shipping a device.
During our secure coding bootcamps, we stress that compliance starts with design, not with patching later.
Key obligations include:
- Secure-by-design development integrated into coding and architecture
- Continuous vulnerability management and flaw remediation
- Security updates for at least five years or the declared lifecycle
- 24-hour reporting of exploited vulnerabilities to ENISA
- Transparency documentation, including a Software Bill of Materials
| Obligation | Key Action | Timeline / Note |
| Secure-by-Design | Integrate security into design & development processes. | Required for all new products. |
| Vulnerability Management | Establish process to identify, document & patch flaws. | Must be maintained for product’s lifecycle or 5 years minimum. |
| Exploit Reporting | Report actively exploited vulnerabilities to ENISA. | Mandatory reporting begins September 11, 2026. |
| Transparency | Provide security documentation & Software Bill of Materials (SBOM). | Required for market access. |
The Practical Countdown: How the CRA Timeline Affects Your Products
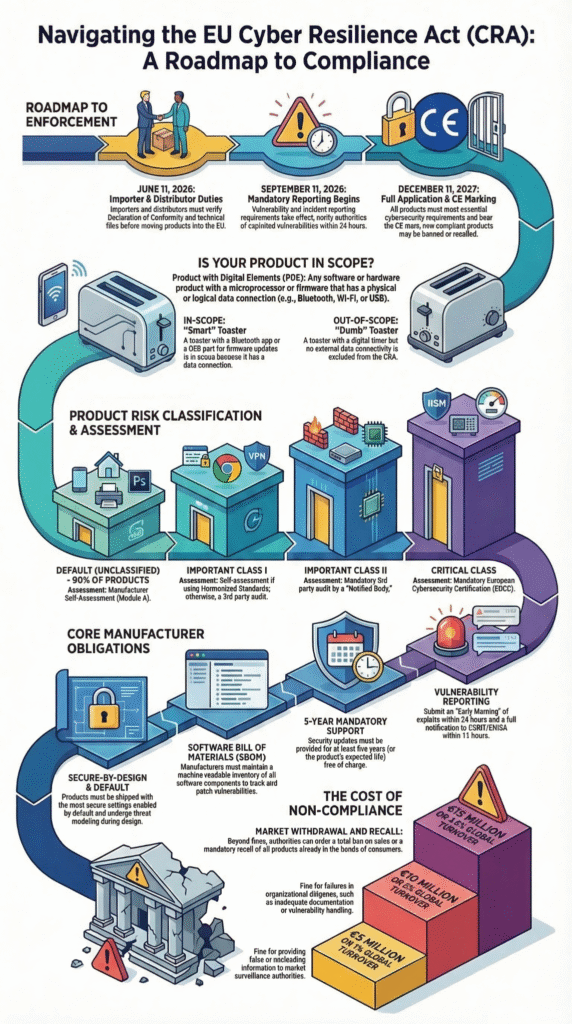
The regulation entered into force on December 10, 2024, but the specific dates for when the Cyber Resilience Act applies to product hardware vary by category. Teams we train often underestimate how quickly that window closes.
“Class II products, including hypervisors and container runtime systems, firewalls and other security systems, and tamper-proof microcontrollers and microprocessors, must be tested externally. In addition, high-risk products such as smart cards and smart meter gateways must be certified according to the appropriate European certification system.” – NTT DATA
Three dates matter most for cyber resilience act high risk products:
- Dec 10, 2024: Regulation officially active
- Sept 11, 2026: Mandatory vulnerability reporting begins
- Dec 11, 2027: Full compliance required for products sold in the EU
Another important concept is “placing on the market.” If a product was sold before the deadline, it may avoid new rules. But that protection disappears if a manufacturer makes a substantial modification.
In our experience working with developers, even a small firmware change can trigger a full reassessment. That’s why planning compliance early saves serious trouble later.
The Embedded Challenge: When Legacy IoT Meets Modern Regulation
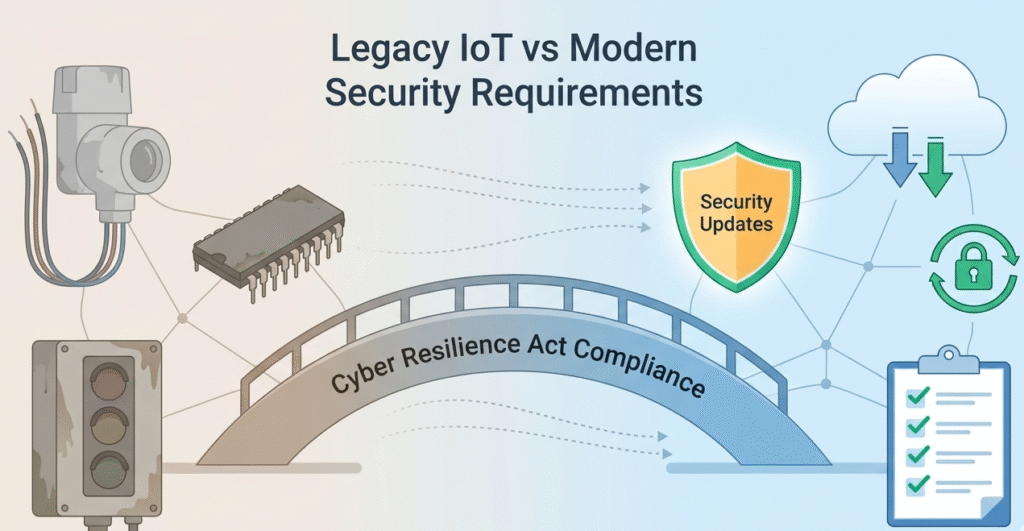
This is the real pinch point: legacy IoT and embedded systems. We see it with clients all the time. Think of a traffic light’s microcontroller or a factory sensor. They were built to last ten years, but with hardware that’s now ancient. There’s no RAM for proper encryption, no CPU headroom for monitoring.
“The Act defines PDEs [Products with Digital Elements] in the critical category as hardware devices with security boxes (i.e., devices used to capture, protect and transfer data securely), smart meter gateways within smart metering systems and other devices for advanced security purposes (such as secure crypto-processing), and smartcards or similar devices.” – URM Consulting Services
The CRA demands these devices be updateable and secure. That creates a brutal compliance gap. You could have thousands of units in the field that simply cannot meet the new rules. The law offers no amnesty for old tech. Your choices narrow to two: fund a massive, costly redesign for these legacy units, or end their support and sales in the EU.
For smaller shops, this isn’t a regulatory headache, it’s an existential threat. Telling someone to “just patch” a device that can’t be patched is pointless.
FAQ
How does the Cyber Resilience Act classify high-risk products with digital elements?
Under the EU Cyber Resilience Act, high-risk digital products are defined by function and potential impact. Devices such as IoT devices, connected devices, and smart home systems may fall into higher product risk categories if compromised systems could affect safety or data security.
Manufacturers must conduct a risk assessment, follow cybersecurity requirements, and ensure secure by design development throughout the product lifecycle.
What cybersecurity requirements apply to high-risk digital products in the EU market?
High-risk products with digital elements must follow strict CRA requirements before entering the EU market. These include security by design, vulnerability handling, regular security updates, and documented risk management practices.
Manufacturers also need to maintain a Software Bill of Materials and demonstrate compliance with cybersecurity standards defined under the European Cyber Resilience Act framework.
How does the conformity assessment procedure work for high-risk digital products?
The conformity assessment procedure evaluates whether a product with digital elements meets the security requirements of the EU Regulation. Some products may follow a self-assessment method, while higher-risk items require evaluation by a conformity assessment body or notified bodies.
After successful verification, the product can receive a CE mark, allowing it to enter the European Union market legally.
What role do vulnerability management and incident reporting play under the CRA?
The Cyber Resilience Act requires manufacturers to maintain a strong vulnerability management system and clear incident response protocols. If active cyber threats or exploited flaws appear, companies must follow strict incident reporting and reporting obligations.
This process helps market surveillance authorities across Member States detect risks early and protect connected digital products from widespread security failures.
Navigating Forward
The Cyber Resilience Act is more than a checklist, it changes how we build and support digital products. For cyber resilience act high risk products, security must exist from design to end of life. Teams need secure-by-design development, continuous vulnerability management, and clear lifecycle support.
At our training sessions, we show developers how to apply these principles in real code. Want practical skills? Join the Secure Coding Practices Bootcamp, a 2-day hands-on course covering OWASP Top 10, secure authentication, encryption, and safe dependency use so developers can ship safer software from day one.
References
- https://benelux.nttdata.com/insights/blog/cyber-resilience-act-what-manufacturers-must-do
- https://www.urmconsulting.com/blog/deconstructing-the-eu-cyber-resilience-act

