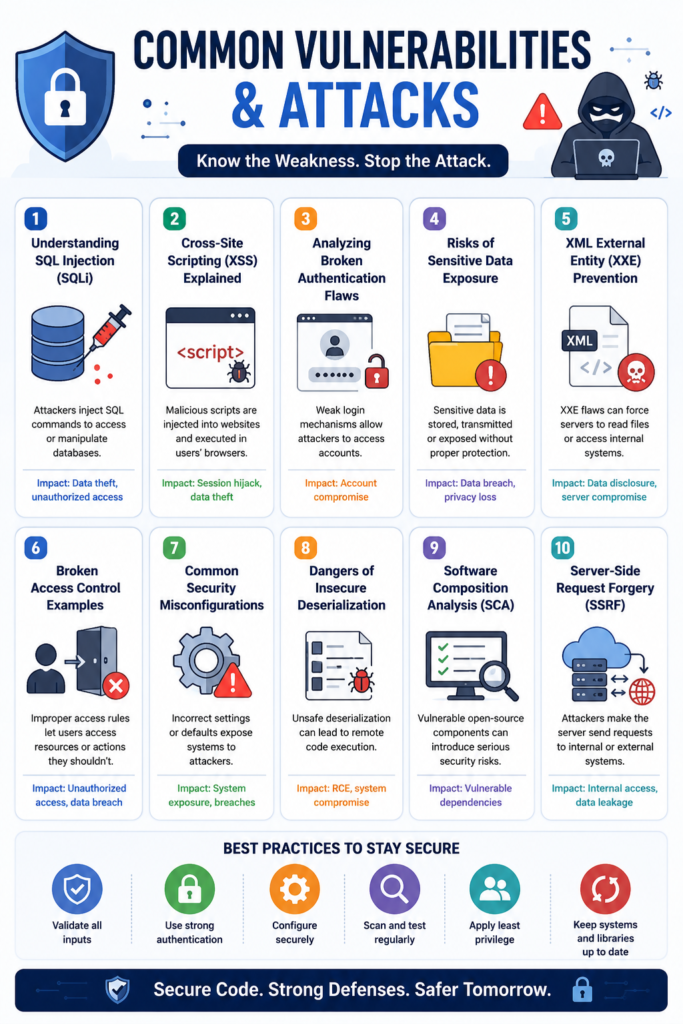
Cyberattacks often happen because of common vulnerabilities hidden inside applications, APIs, and systems. Issues like SQL injection, XSS, broken authentication, and SSRF continue affecting organizations of all sizes.
From our experience, many businesses improve security faster when they understand how these vulnerabilities work and where attackers usually exploit them. Strong security starts with better visibility, secure development practices, and continuous testing. Keep reading to explore the most common vulnerabilities and attacks shaping modern cybersecurity risks.
Key Security Insights
Understanding vulnerabilities helps organizations reduce risks before attackers exploit them.
- Many cyberattacks succeed through preventable weaknesses.
- Secure coding and testing improve long-term resilience.
- Continuous monitoring helps reduce operational exposure.
Understanding SQL Injection (SQLi)
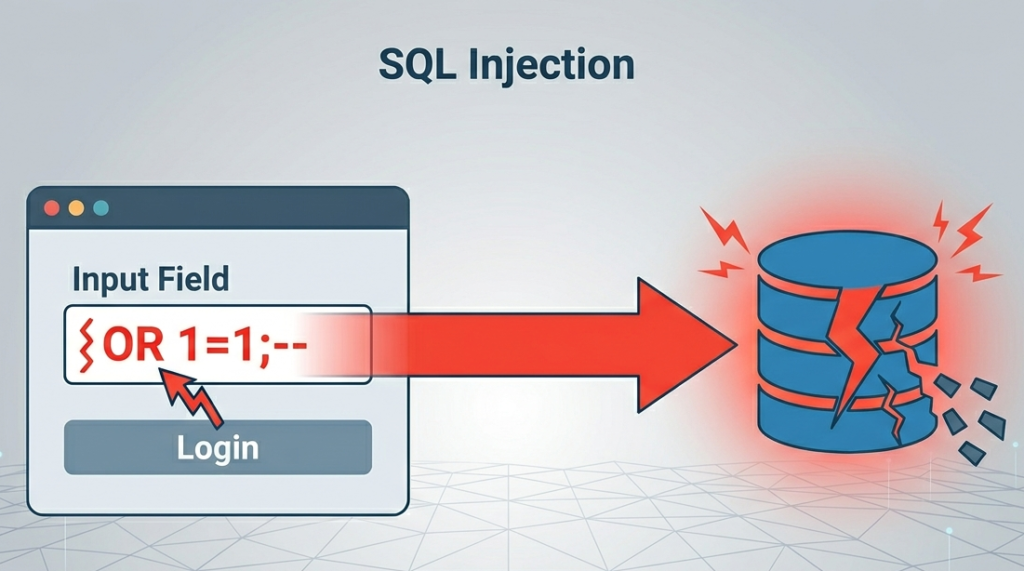
SQL Injection happens when attackers manipulate database queries through insecure input handling. This vulnerability can expose sensitive records or allow unauthorized database access.
“Web application security is a major concern due to the growing prevalence of cyberattacks, particularly SQL injection attacks, which compromise the integrity, confidentiality, and availability of data” – Jurnal E-Komtek
Common SQLi risks include:
- Data theft
- Credential exposure
- Database manipulation
- Unauthorized access
Organizations often reduce SQLi risks through:
- Parameterized queries
- Input validation
- Secure database permissions
- Prepared statements
We often see SQL injection remain active in older applications using outdated development practices.
Cross-Site Scripting (XSS) Explained
Cross-Site Scripting allows attackers to inject malicious scripts into web applications viewed by other users.
Common XSS attack types include:
- Stored XSS
- Reflected XSS
- DOM-based XSS
Potential impacts include:
- Session hijacking
- Credential theft
- Browser manipulation
- Unauthorized transactions
Many organizations improve XSS prevention through stronger input sanitization and output encoding practices.
Analyzing Broken Authentication Flaws
Credits: Hacker Joe
Broken authentication vulnerabilities happen when applications fail to secure identities, sessions, or credentials properly.
Common authentication weaknesses include:
- Weak password requirements
- Session fixation
- Credential stuffing exposure
- Missing MFA protection
Strong authentication controls help reduce account takeover risks significantly.
Risks of Sensitive Data Exposure
Sensitive data exposure occurs when confidential information is stored or transmitted insecurely.
Common causes include:
- Weak encryption
- Misconfigured cloud storage
- Insecure backups
- Exposed credentials
Sensitive information often targeted includes:
- Customer records
- Financial information
- API keys
- Internal documents
From our perspective, small configuration errors frequently create large exposure risks.
XML External Entity (XXE) Prevention
XXE vulnerabilities happen when applications process insecure XML input containing malicious external entities.
“Simply asking reviewers to focus on security during the code review increases eight times the probability of vulnerability detection”. – University of Zurich (ZORA)
Potential XXE impacts include:
- Internal file disclosure
- SSRF exploitation
- Internal network access
- Denial-of-service attacks
Prevention methods often include:
- Disabling external entities
- Secure XML parsers
- Input validation
- Restricted parser permissions
Organizations handling XML-based integrations should review parser configurations carefully.
Broken Access Control Examples
Broken access control vulnerabilities allow users to access restricted functions or data improperly.
Common examples include:
- Unauthorized account access
- Privilege escalation
- Insecure direct object references
- Restricted data modification
Many organizations struggle with maintaining consistent authorization rules across APIs and cloud platforms.
Strong role-based access controls usually improve visibility and security consistency.
Common Security Misconfigurations
Security misconfigurations remain one of the most widespread cybersecurity issues across infrastructure and applications.
Common examples include:
- Default credentials
- Open cloud storage
- Excessive permissions
- Exposed admin interfaces
- Unnecessary services enabled
We often see rushed deployments create avoidable exposure risks.
Continuous configuration reviews help reduce vulnerabilities significantly.
Dangers of Insecure Deserialization
Insecure deserialization vulnerabilities occur when applications process untrusted serialized data insecurely.
Potential impacts include:
- Remote code execution
- Application compromise
- Privilege escalation
- Service disruption
Organizations often reduce risks through:
- Integrity validation
- Input filtering
- Secure serialization methods
- Minimal trust assumptions
Applications handling complex object processing usually require additional testing.
Software Composition Analysis (SCA)
Software Composition Analysis helps organizations identify vulnerable third-party dependencies inside applications.
SCA processes commonly identify:
- Vulnerable libraries
- Outdated dependencies
- License compliance issues
- Supply chain risks
| SCA Function | Purpose |
| Dependency Tracking | Monitor third-party software |
| Vulnerability Detection | Identify known weaknesses |
| License Visibility | Improve compliance management |
| Risk Prioritization | Support remediation planning |
Many businesses underestimate risks hidden inside open-source components.
Server-Side Request Forgery (SSRF)
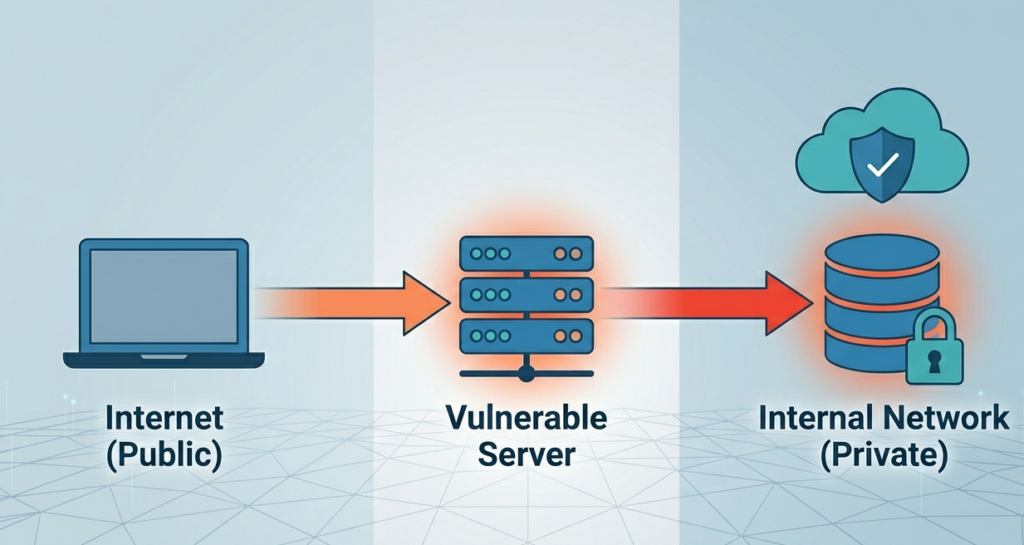
SSRF vulnerabilities allow attackers to force servers into making unauthorized internal or external requests.
Common SSRF risks include:
- Cloud metadata exposure
- Internal network scanning
- Credential theft
- Access to restricted services
Prevention strategies include:
- URL validation
- Request filtering
- Network segmentation
- Metadata restrictions
SSRF attacks continue increasing because cloud services depend heavily on interconnected internal systems.
FAQ
What are common vulnerabilities in cybersecurity?
Common vulnerabilities include SQL injection, XSS, SSRF, XXE, broken authentication, and security misconfigurations.
Why is SQL injection dangerous?
SQL injection can expose sensitive databases and allow attackers to manipulate stored information.
What does Software Composition Analysis do?
SCA identifies vulnerable third-party libraries and dependencies inside software applications.
How can organizations reduce vulnerability risks?
Organizations improve resilience through secure coding, access management, testing, and continuous monitoring.
Building Stronger Security Through Vulnerability Awareness
Modern security relies on catching weaknesses before they become disasters. As cloud environments grow, organizations must shift from just “fixing” problems to preventing them through better coding and testing.
Building a resilient defense starts with your development team. Instead of dealing with complex jargon, focus on practical, hands-on skills that secure your software from the start. Join the Secure Coding Practices Bootcamp Learn to ship safer code and protect your business from day one.
References
- https://jurnal.politeknik-kebumen.ac.id/E-KOMTEK/article/download/2260/1443
- https://www.zora.uzh.ch/server/api/core/bitstreams/370fbc77-733d-4df5-93fc-4de7d16769c2/content
