Importance Trust Boundaries Threat Modeling: Why Defining Limits Matters
Trust boundaries are the invisible lines between things that trust each other and things that shouldn’t. A user’s computer…
Get practical advice, tutorials, and updates from security professionals. Our blog helps developers write safer code, understand real-world threats, and grow their secure coding skills.
Trust boundaries are the invisible lines between things that trust each other and things that shouldn’t. A user’s computer…
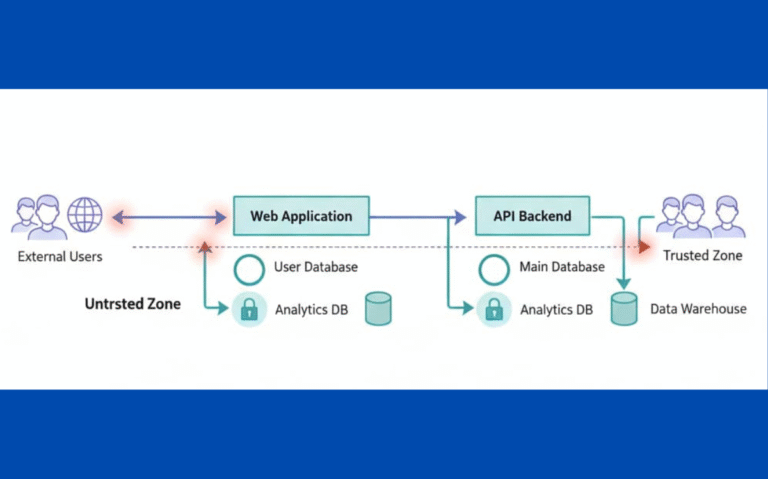
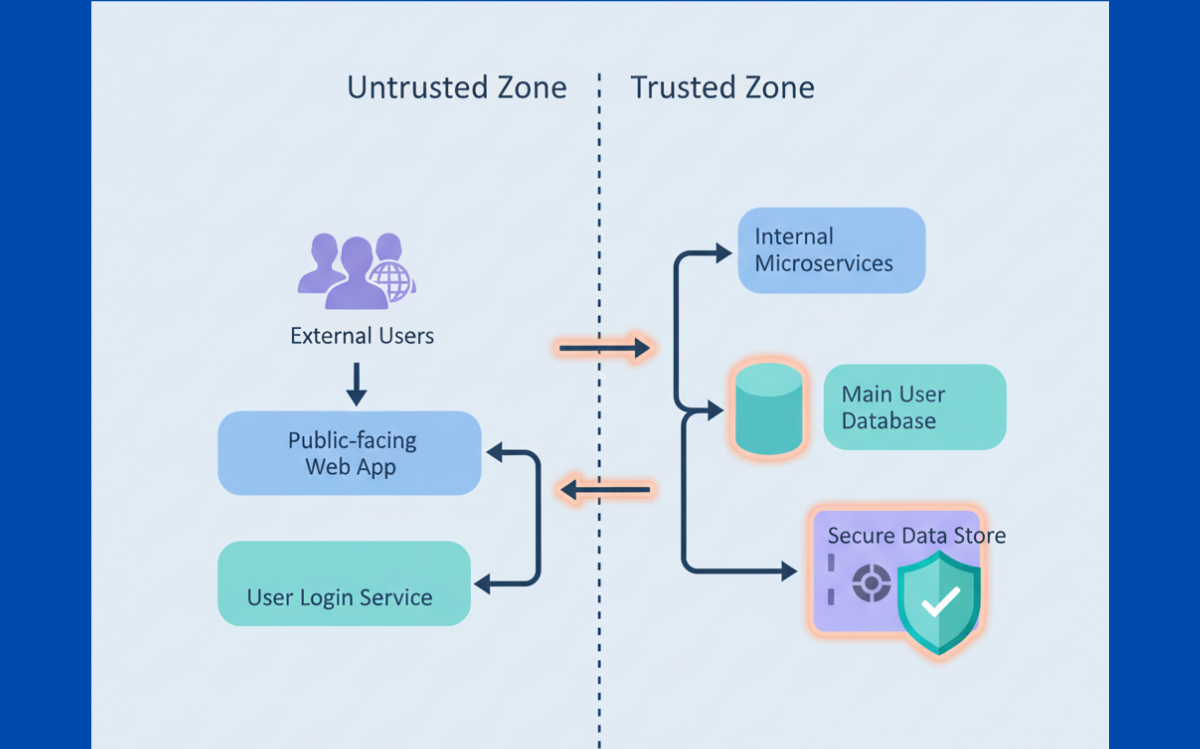
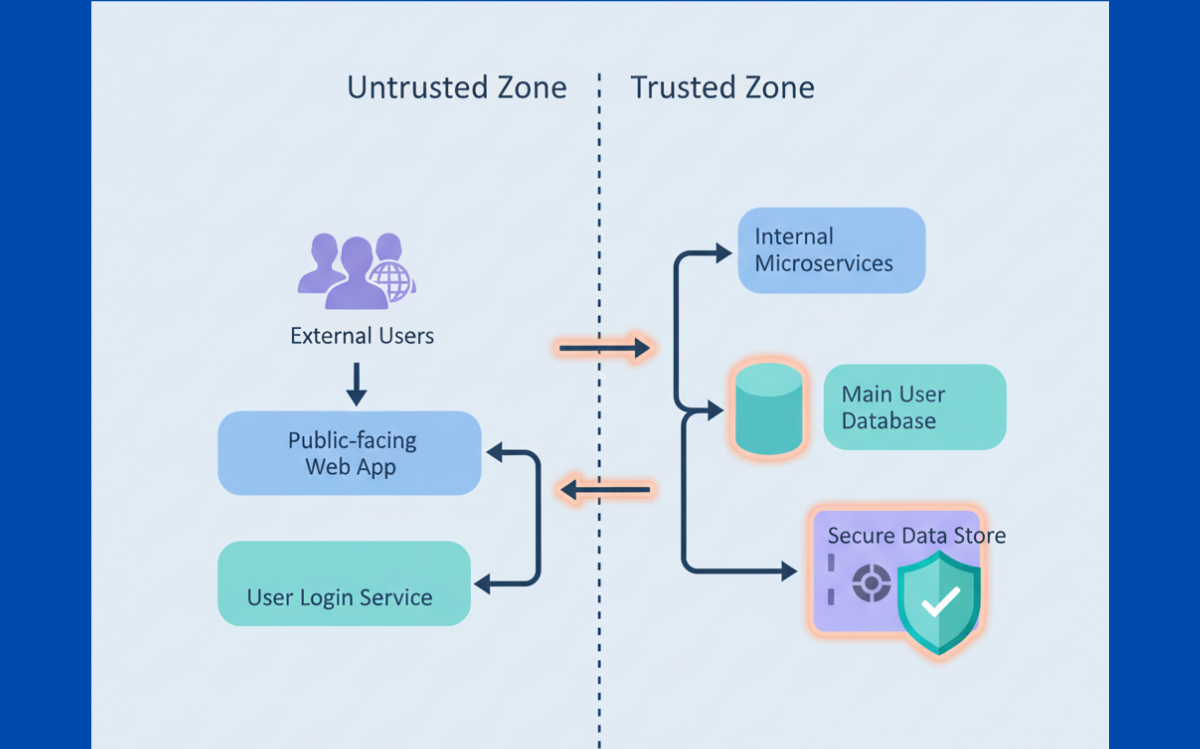
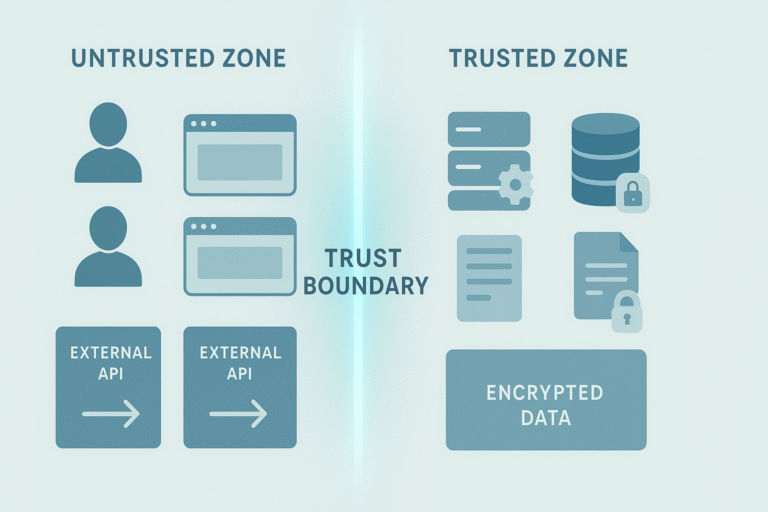
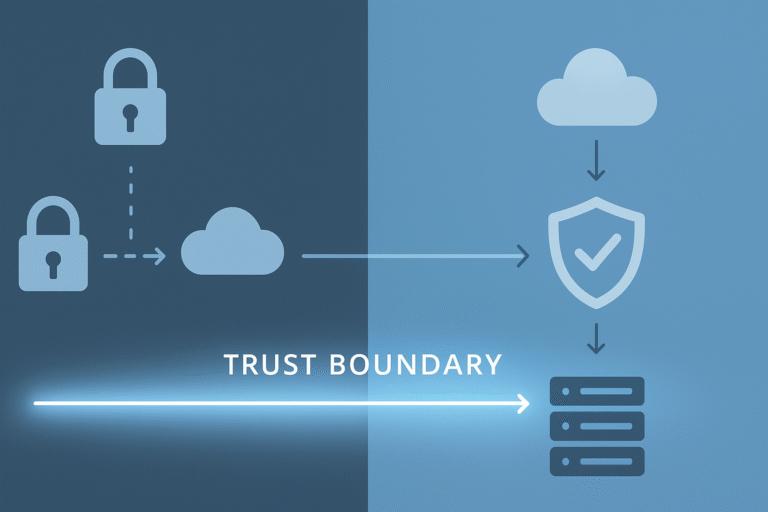
Trust boundaries in data flow diagrams mark where data shifts between areas with different security levels. These crossing points?…
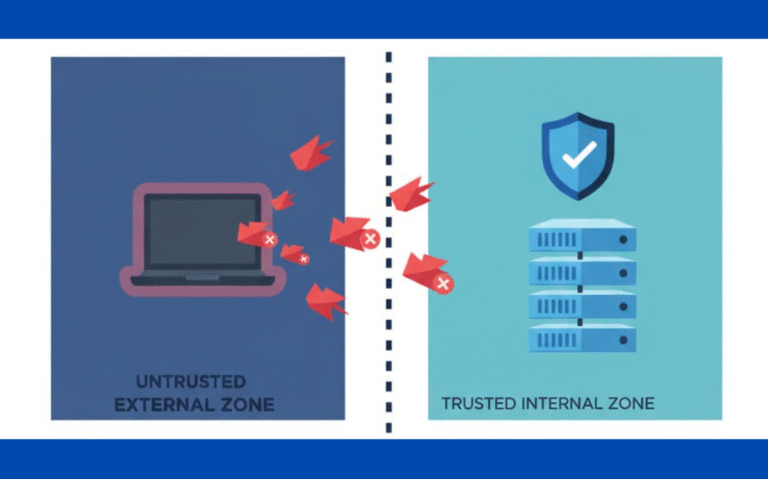
When untrusted data gets into protected zones without checks, attackers slip through. A trust boundary violation is when code…
We’ve watched developers miss obvious security gaps because they never mapped where their data actually moves. Trust boundaries are…
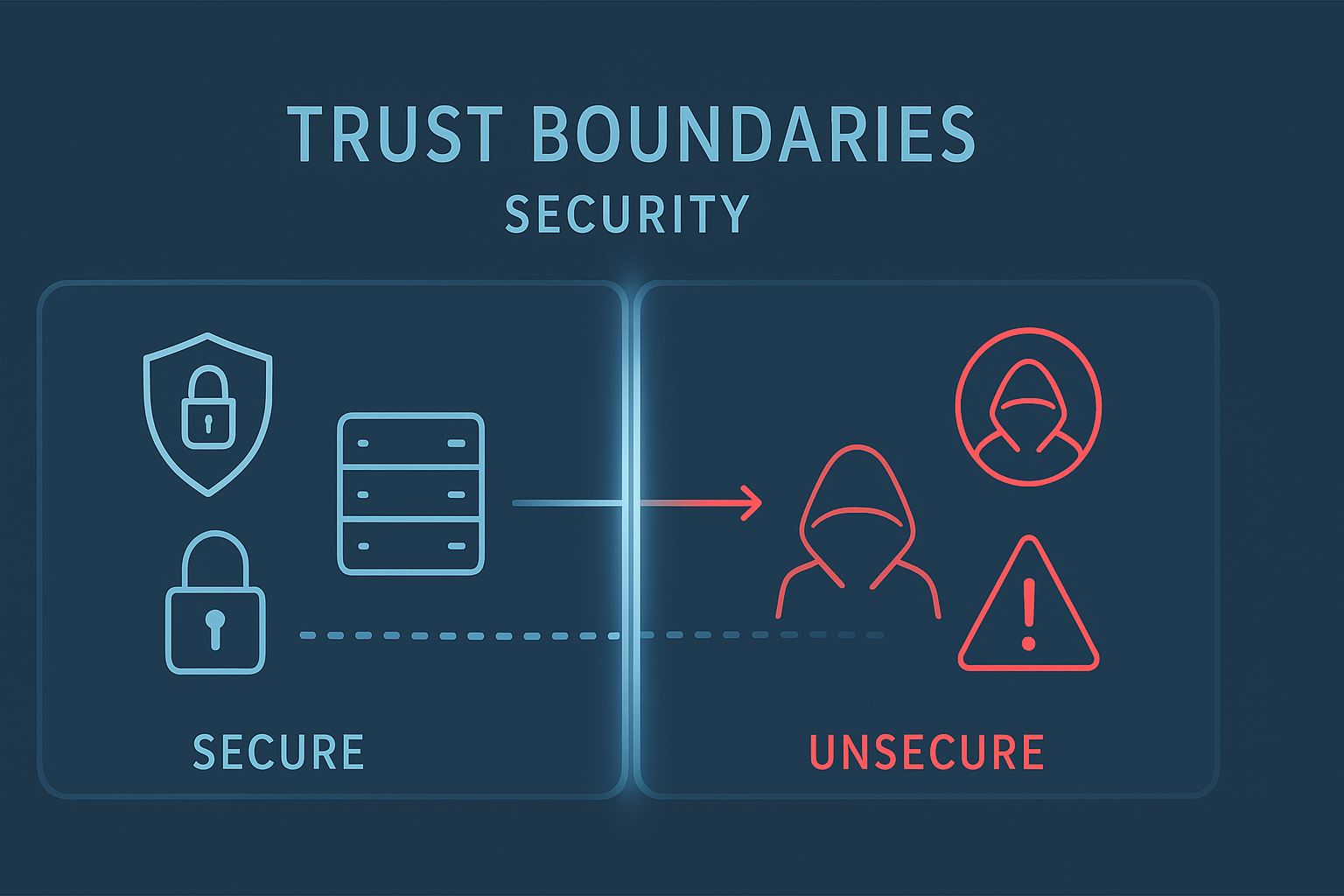
Trust boundaries define critical points in software systems where data crosses between secure and less-trusted zones. Our secure development…
Trust boundaries mark the line where secure meets unsecure areas within software systems. These crossing points need special attention…
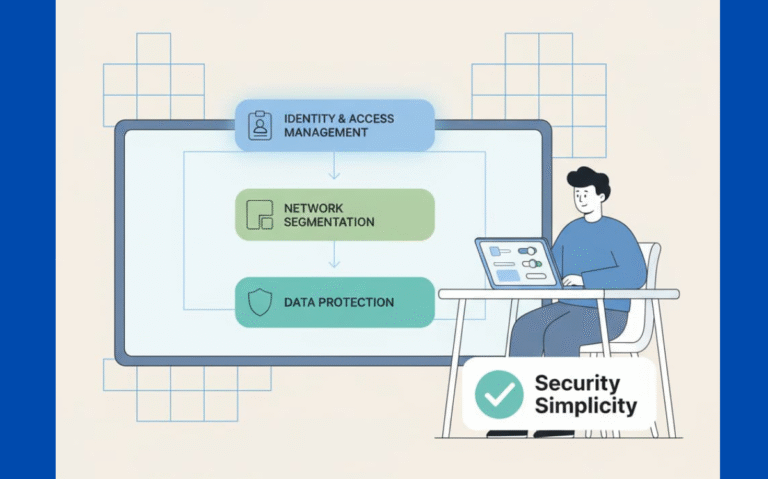
Complex security doesn’t mean better security, something most coders learn the hard way. When teams stack security features like…
Security doesn’t need to be complicated. Most data breaches happen because someone piled on too many security tools, creating…
Clean code beats fancy tricks when it comes to security. Nobody wants to debug a maze of functions at…
Look, security doesn’t have to be rocket science. Most teams mess up by adding endless layers of protection that…