Yes, application security training is fundamentally broken. It’s a system built on mandates and compliance checkboxes, not on empowering the people who write the code. You see the symptoms everywhere, developers overwhelmed by vulnerability alerts, AppSec teams drowning in a reactive “defensive tax,” and a painful friction where security feels like an obstacle, not a partner. The data paints a stark picture of this disconnect.
This isn’t about needing more training, it’s about needing a different kind of training altogether. One that starts where developers work and solves the problems they actually face.
Keep reading to understand the precise fractures in the current model and what a working alternative looks like.
Key Statistics on Broken AppSec Training
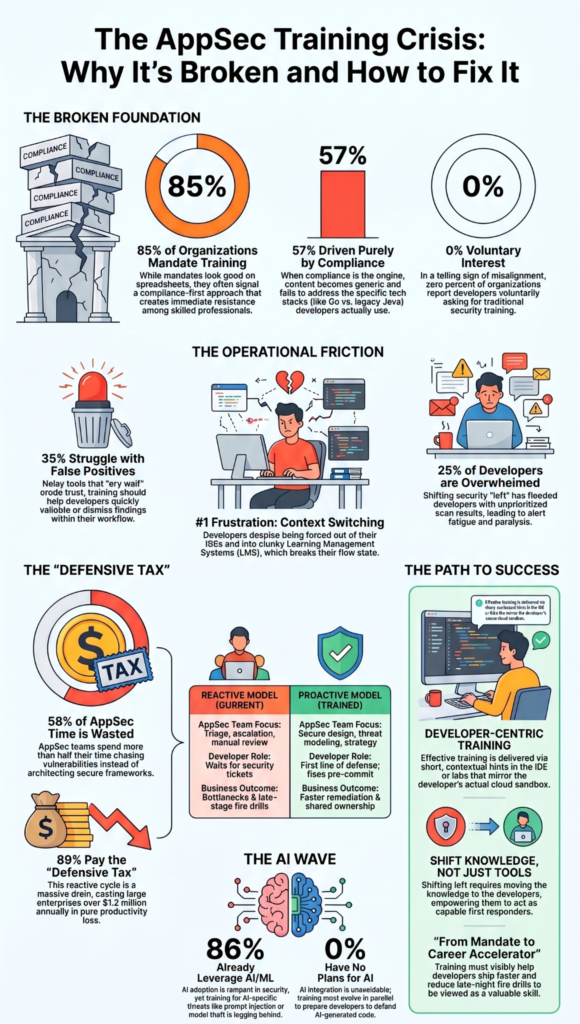
The numbers don’t lie. They reveal a massive gap between what organizations are spending on security education and the tangible outcomes they’re getting. Here are the figures that define the crisis.
- 85% of organizations mandate AppSec training, yet it’s driven by policy, not developer need.
- 57% of organizations say compliance is the primary driver for their AppSec training programs.
- Developers’ #1 frustration is security content not delivered through dev or security tools, creating a context switch that breaks their flow.
- 25% of developers report being overwhelmed by the sheer volume of vulnerabilities they must address.
- 58% of AppSec teams spend more than half their time just chasing vulnerabilities, not building proactive programs.
- A staggering 89% of AppSec professionals spend at least a quarter of their time in “defensive tax” mode, reacting to issues.
- 86% of organizations are leveraging AI/ML significantly within their security strategy already.
- 0% of organizations have zero plans to integrate AI into their security approach, making it an unavoidable wave.
- In a telling stat, 0% of organizations reported developers voluntarily asking for security training.
- 35% of organizations say false positives are their top “shift left” challenge, eroding developer trust.
85% of Organizations Mandate AppSec Training
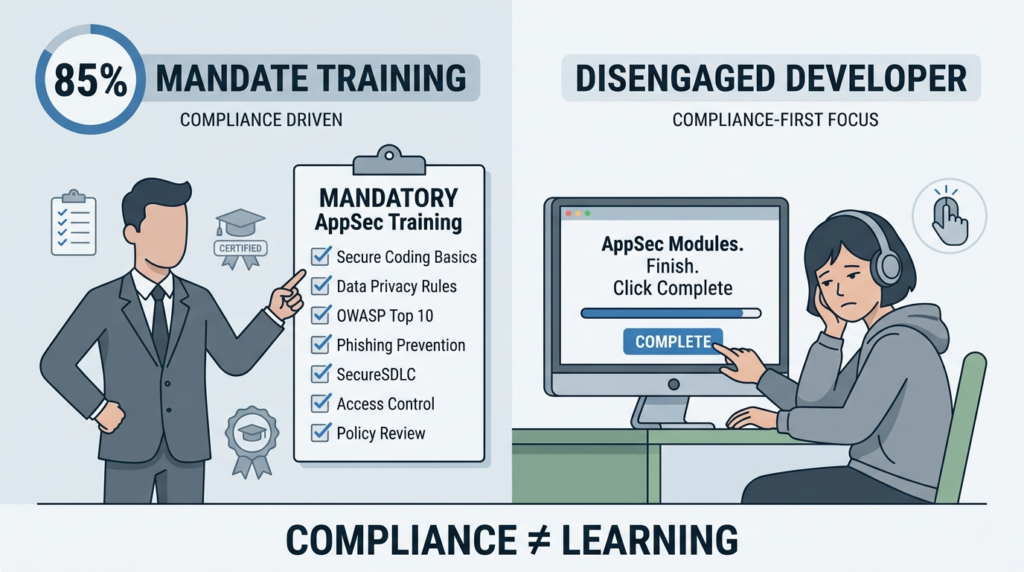
According to Security Compass (March 31, 2026), 85% of organizations mandate AppSec training. The high mandate rate looks like commitment on a spreadsheet.
In practice, it often signals a top-down, compliance-first approach. Training becomes a requirement to satisfy an audit or a contract clause, not a skill-building exercise.
This foundation sets the tone for everything that follows. When the “why” behind training is “because you have to,” you immediately create resistance. Developers, like any skilled professionals, engage with material that feels relevant and useful to their daily work.
Mandates without meaningful context prepare the ground for disengagement. The completion certificate becomes the goal, not the secure coding skill.
57% of Organizations Where Compliance Drives Training
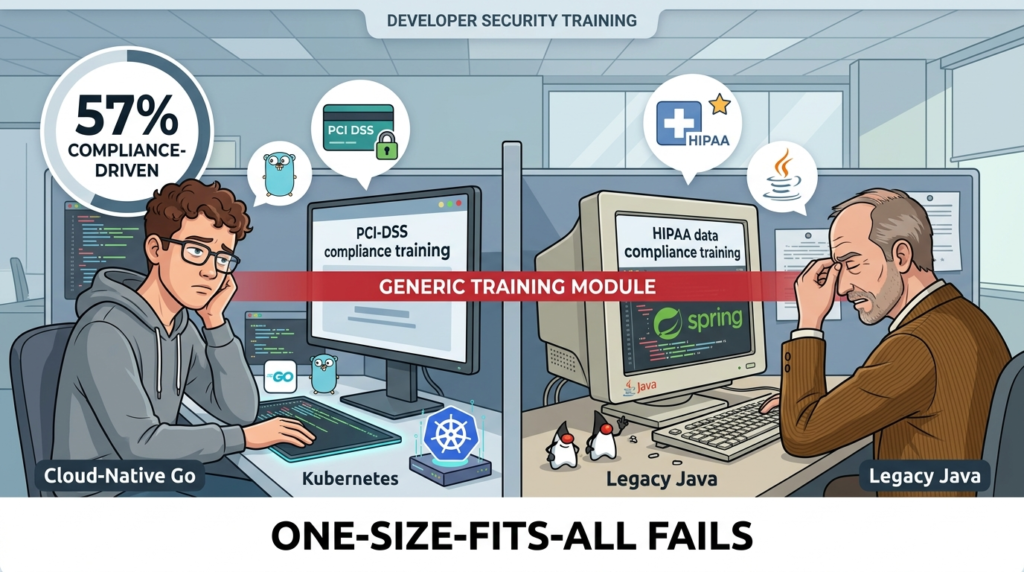
According to Security Compass (March 31, 2026), 57% of organizations say compliance drives their AppSec training. When compliance is the engine, the training content becomes generic. It has to be. It’s designed to cover broad regulatory bases like PCI DSS or HIPAA for the widest possible audience.
This creates a critical misalignment. A developer working on a cloud-native microservice in Go faces the same generic module as someone maintaining a legacy Java monolith. The principles might be universal, but the application isn’t.
This gap between the generic lesson and the specific tech stack is where knowledge evaporates. Developers sit through it, check the box, and return to their IDEs no better equipped to handle the actual security flaws in their pull requests.
Developers’ #1 Frustration: Content Not in Dev Tools
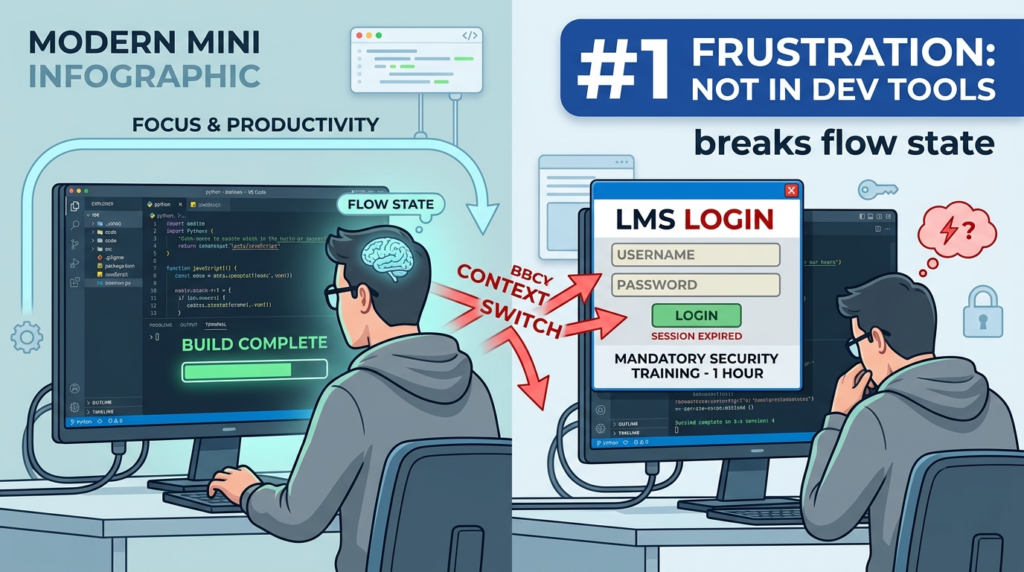
According to Security Compass (March 31, 2026), developers’ top frustration is that training content is not delivered through development or security tools. This is the operational heart of the failure.
Developers live in their integrated development environments (IDEs), version control, and CI/CD pipelines. Forcing them to log into a separate, often clunky learning management system (LMS) is a productivity killer. It’s a context switch that their workflow is designed to avoid.
The frustration isn’t about learning security, it’s about the friction of the delivery. Effective training meets developers where they are. Think short, contextual hints in the IDE when a vulnerable pattern is typed, or interactive labs that mirror their actual cloud sandbox. The tooling disconnect makes security feel like a separate, burdensome discipline instead of an integrated part of building software.
- It breaks flow state, which is critical for deep work.
- It makes training feel divorced from real tasks.
- It reinforces the “security vs. speed” false dichotomy.
25% of Developers Overwhelmed by Vulnerability Volume
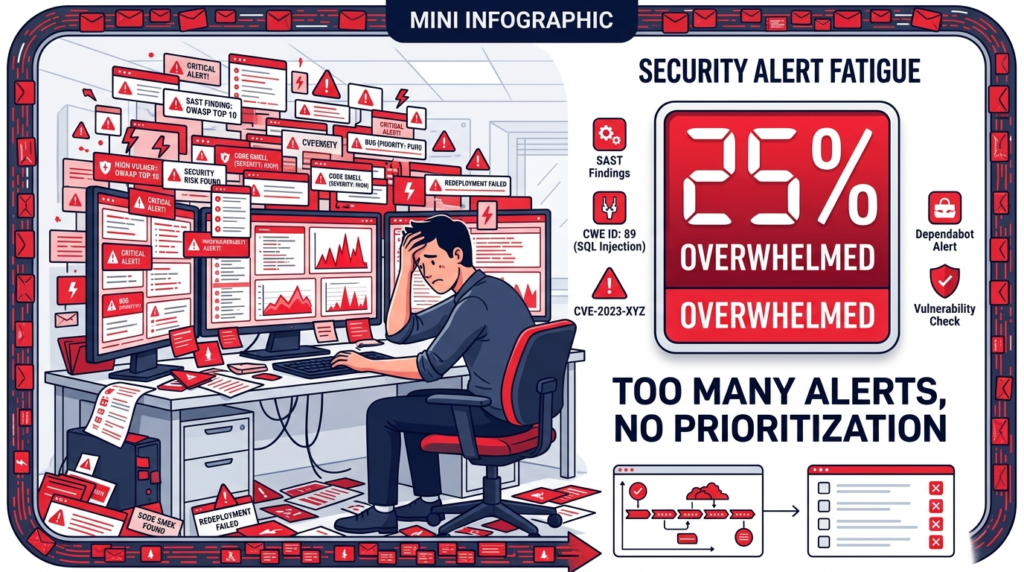
According to Pynt’s shift-left security survey (April 9, 2026), 25% of developers report being overwhelmed by vulnerability volume. Shift-left principles brought security tools earlier into the development lifecycle.
The unintended consequence was flooding developers with raw, unprioritized scan results. A SAST tool might flag hundreds of potential issues, many of which are false positives or low-risk code smells. Without the training to triage and understand these alerts, developers are paralyzed.
They either ignore the noise or waste hours investigating minor issues. This overwhelm directly leads to alert fatigue, where critical warnings get lost in the clutter. Training shouldn’t just teach secure coding, it must teach vulnerability management, how to read a scan report, and how to prioritize a fix based on actual exploitability.
58% of AppSec Teams Spend >50% of Time Chasing Vulnerabilities
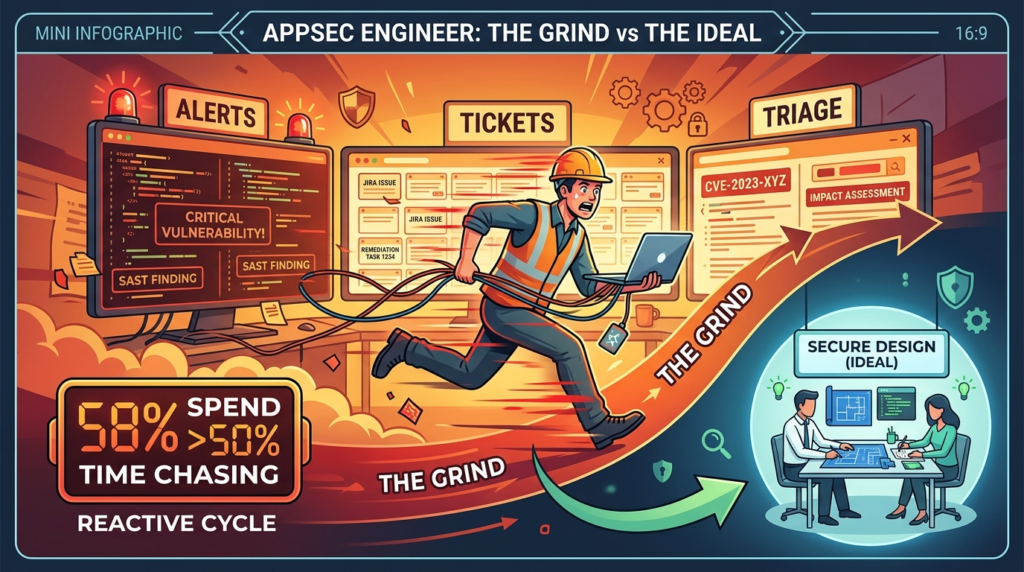
According to Backslash Security (March 30, 2026), 58% of AppSec teams spend more than half their time chasing vulnerabilities. This statistic reveals the unsustainable reactive cycle. AppSec professionals, who should be architecting secure frameworks and guiding developers, are instead stuck in a loop of triage and escalation.
They become human routers between scanning tools and development teams. This “chasing” is the core of the defensive tax, a massive drain on resources that prevents proactive security work. It often stems from the very training gap we’re discussing. When developers aren’t empowered to fix common issues themselves, every medium-severity SQL injection finding becomes a ticket for the AppSec team to analyze, explain, and follow up on.
The table below contrasts the reactive trap with a proactive, trained-up state.
| Resource Allocation | Reactive Model (Current State) | Proactive, Trained Model |
| AppSec Team Focus | Triage, escalation, manual review | Secure design, threat modeling, tooling strategy |
| Developer Role | Code author, waits for security tickets | First line of defense, fixes common flaws pre-commit |
| Outcome | Bottlenecks, friction, late-stage fire drills | Faster remediation, fewer critical bugs, shared ownership |
89% of AppSec Teams in “Defensive Tax” Mode
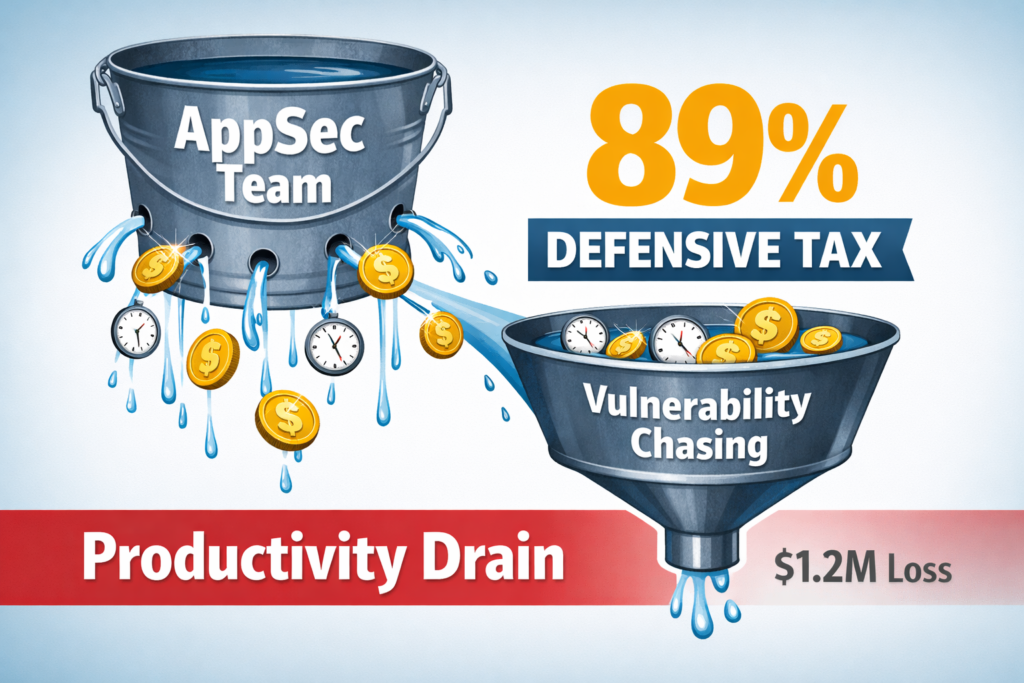
According to Backslash Security (March 30, 2026), 89% of AppSec teams spend at least 25% of their time in “defensive tax” mode. The defensive tax is the aggregate cost of that reactive cycle.
It’s measured in the salary hours spent chasing vulnerabilities instead of building robust programs, and in the delayed feature releases because security reviews are a bottleneck. For large enterprises, this tax can exceed $1.2 million annually in pure productivity loss.
It’s a direct result of a missing enablement layer. You’ve shifted left by moving the tools, but you didn’t shift left the knowledge. The AppSec team remains the sole owner of security knowledge, creating a constant pull on their time.
Reducing this tax requires investing in training that turns developers into capable first responders.
86% of Organizations Leveraging AI/ML in Security

According to Security Compass (March 31, 2026), 86% of organizations are already leveraging AI/ML in their security strategy. AI adoption in security is rampant, primarily for threat detection, log analysis, and code scanning.
This changes the attack surface and the defense strategy. Yet, how much training addresses securing AI-powered applications themselves, or understanding the novel vulnerabilities in AI-generated code? There’s a gap.
Developers using GitHub Copilot or Amazon CodeWhisperer need to know how to review and secure AI-suggested code. Teams building with LLMs need training on prompt injection, training data poisoning, and model theft. The training curriculum is racing to catch up to the technology already in use.
0% of Organizations With No Plans to Integrate AI
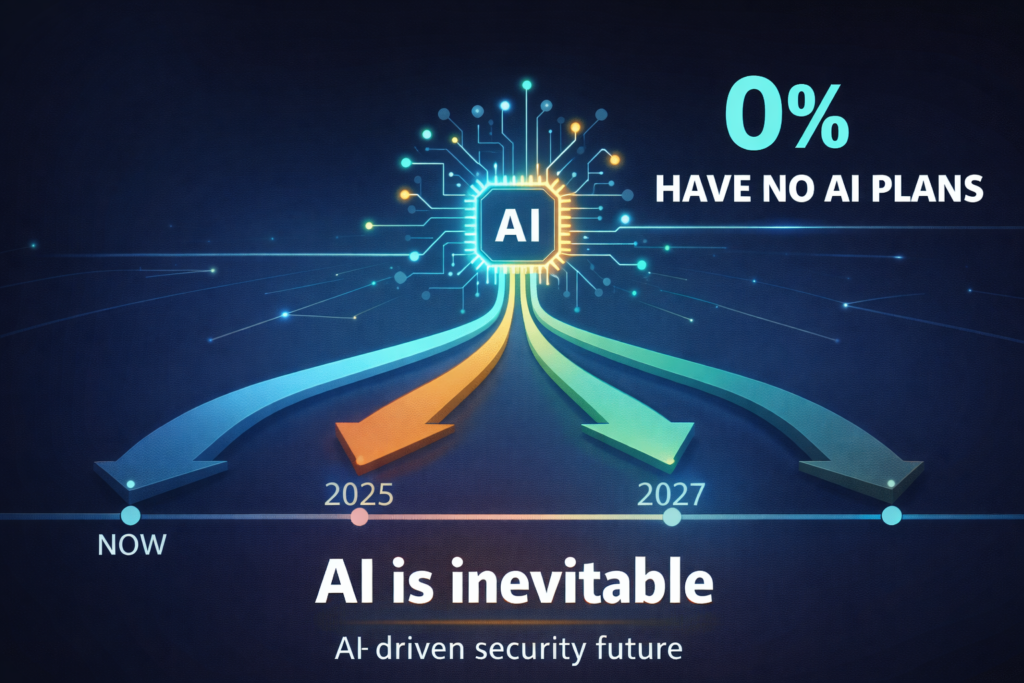
According to Security Compass (March 31, 2026), 0% of organizations have no plans to integrate AI into security. This is the clearest signal of an unavoidable trend.
AI will be part of the security fabric for every organization. The question isn’t if, but how and how securely. This universal trajectory makes AI-aware security training not a niche topic, but a core competency for the next generation of developers.
Waiting to train your team until after AI integration is complete is a major strategic risk. The training must evolve in parallel, preparing developers to build with and defend these new technologies from the start.
0% Where Developers Asked for Training Voluntarily
According to Security Compass (March 31, 2026), 0% of organizations report developers asking for security training voluntarily. This is perhaps the most damning statistic. In zero percent of organizations did developers ask for this training.
Let that sink in. It underscores that current offerings are not seen as valuable career development or useful problem-solving tools. They are seen as an obligatory corporate ritual.
This is the ultimate proof of misalignment. To fix AppSec training, you must create something developers would seek out, something that visibly helps them do their jobs better, ship faster, and reduce late-night fire drills. It must transition from a “compliance mandate” to a “career accelerator.”
35% Citing False Positives as Top Shift-Left Challenge

According to Pynt’s shift-left security survey (April 9, 2026), 35% of organizations cite false positives as the top shift-left challenge. False positives are a trust killer. When a security tool cries wolf repeatedly over non-issues, developers learn to ignore it. This erodes the entire value of shifting left.
Training is a primary solution to this, but not in the way you might think. It’s not about teaching developers to accept more alerts. It’s about teaching them the why behind the tool’s logic, so they can quickly validate or dismiss a finding.
It’s about training them to write code that doesn’t trigger those false positives in the first place. Understanding the underlying security rules transforms a noisy, antagonistic tool into a precise, helpful linter.
FAQ
Why does AppSec training often fail developers in real-world coding environments?
AppSec training often fails because it relies on outdated vulnerability modules and generic training pitfalls. Many programs focus on checkbox compliance training instead of real-world coding issues. Developers face AppSec fatigue due to tedious cybersecurity modules, low engagement, and lack of hands-on AppSec labs. Without role-specific secure coding or alignment with short dev cycles, adoption rates drop and learning doesn’t translate into practice.
How can AppSec training better align with modern development workflows?
To improve alignment, AppSec training must integrate with SDLC security practices and reflect evolving framework updates. Traditional AppSec shortcomings come from event-focused vs process training approaches. Developers need interactive AppSec experiences tied to real vuln focused sessions, not video-based secure coding fails. Embedding scan data mapped training and API attack training needs into workflows helps bridge the gap between learning and daily development tasks.
What makes developers disengage from secure coding courses?
Developer resistance to AppSec often comes from overengineered training programs and time-consuming AppSec sessions. Low engagement is driven by lack of engaging content, missing tech-specific examples, and poor problem-solving dev engagement. When training ignores feature priority security lag and short dev cycles pressure, developers see it as irrelevant. This leads to low adoption rates, Q1 usage spikes drop, and weak vulnerability fix skills.
What are the biggest gaps in traditional AppSec training programs?
Key gaps include missing immersive AppSec methodology, lack of continuous assessment needs, and weak behavior change metrics. Many programs fail due to SAST DAST training disconnect and OWASP Top 10 gaps without context. There’s also poor alignment between L&D security alignment and real developer workflows. Without vulnerability reduction metrics and team participation tracking, organizations struggle to measure effectiveness or justify budget investment.
How can organizations build effective and scalable AppSec training programs?
Effective programs focus on role-specific secure coding, real vuln focused sessions, and continuous threat evolution upskilling. Moving beyond compliance beyond checkbox, organizations should adopt immersive AppSec methodology with interactive labs and coding standards updates. Tracking adoption metrics, integrating ERP integrated training, and aligning with regulation-aligned AppSec ensures scalability. Strong security culture build depends on practical, developer-centric learning that evolves with market pressure adaptations.
The Path to Training That Actually Works
The data shows a system straining under its own weight. Mandates without engagement, tools without understanding, and teams stuck in a costly reactive loop. The fix isn’t more of the same, it’s a fundamental redesign centered on the developer’s reality.
Effective training is contextual, delivered in the workflow, and built on the specific vulnerabilities found in your own codebase. It’s short, hands-on, and feels like solving a problem, not sitting through a lecture. It moves beyond the OWASP Top 10 generics to address the API security issues, the cloud misconfigurations, and the AI-specific threats your team is actually facing. This is how you turn a defensive tax into a strategic investment. This is how you build a security culture that sticks.
Stop checking the box and start building capability. Explore how hands-on, developer-centric training can transform your AppSec posture at Secure Coding Practices.
