Practical implementation of the Cyber Resilience Act (CRA) is where many teams struggle, not with theory, but execution. We’ve seen firsthand how gaps often appear in coding discipline, documentation, and process alignment. While regulations set expectations, turning them into daily workflows requires clarity and consistency.
This guide blends our experience with actionable steps to help teams implement CRA requirements effectively without overwhelming development cycles. Keep reading to understand how structure, tools, and mindset come together in real-world compliance.
Key Insights On Practical CRA Implementation
Implementing CRA is not just about compliance, it’s about building resilient software from the ground up.
- Start with Secure Coding Practices as the foundation
- Use structured checklists to standardize workflows
- Combine tools with human review processes
Cra Secure Software Implementation Guide
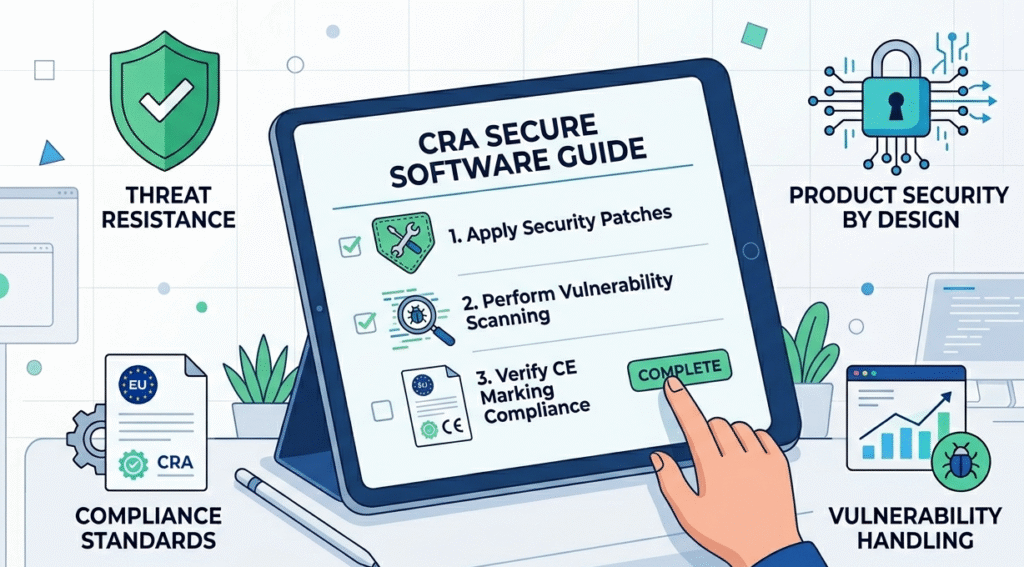
We approach CRA implementation by embedding security early in development. Instead of adding controls later, we integrate them into coding standards and workflows.
Key steps:
- Define secure development lifecycle aligned with CRA
- Integrate Secure Coding Practices into daily coding
- Establish documentation for traceability
- Perform continuous risk assessment
- Align with product lifecycle requirements
From experience, teams that treat security as a shared responsibility adapt faster and reduce audit friction.
“Secure coding is the practice of developing computer software in a way that guards against the accidental introduction of security vulnerabilities.” – Wikipedia
Cyber Resilience Act Secure Coding Checklist
Credits: Hogan Lovells
A checklist helps translate regulation into action. We rely on structured validation to ensure consistency across teams.
Checklist essentials:
- Input validation and output encoding
- Authentication and authorization controls
- Secure data storage and encryption
- Dependency and vulnerability management
- Logging and monitoring readiness
Using a checklist ensures nothing is overlooked, especially in fast-moving development environments. Teams often discover that consistency, not complexity, is the real challenge.
Secure Coding Tools Cyber Resilience Act
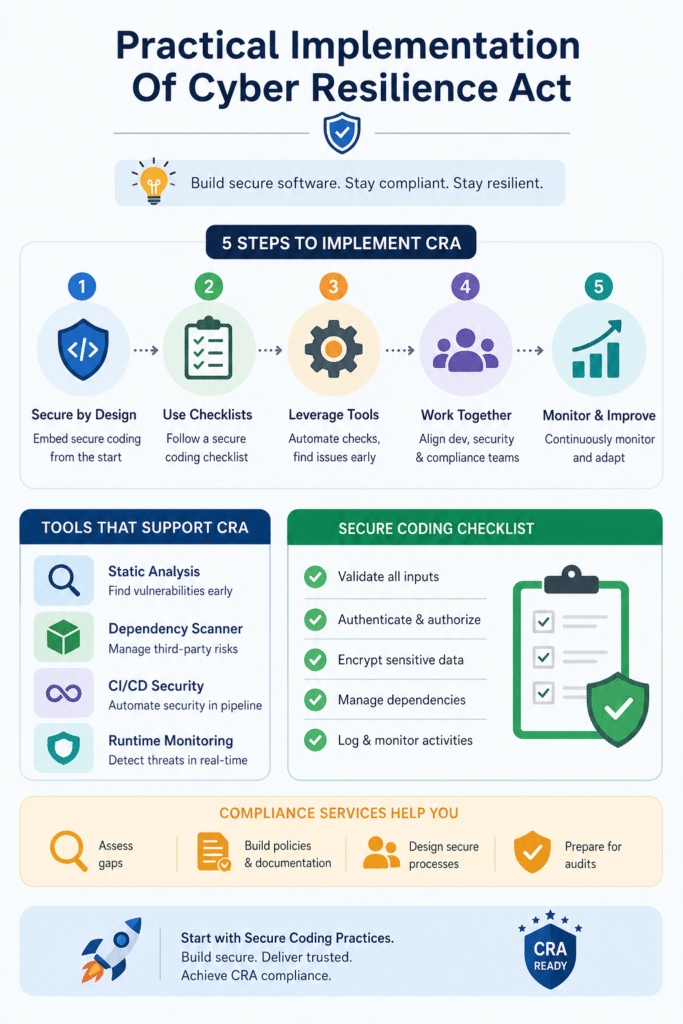
Tools support implementation, but they don’t replace discipline. We use tools to reinforce, not define, security practices.
| Tool Category | Purpose | CRA Relevance |
| Static Analysis Tools | Detect code vulnerabilities early | Supports secure development |
| Dependency Scanners | Identify third-party risks | Ensures supply chain security |
| CI/CD Security Tools | Automate security checks | Enables continuous compliance |
| Runtime Monitoring | Detect live threats | Supports lifecycle security |
The most effective teams combine automation with manual review for balanced security.
Cyber Resilience Act Compliance Services

Compliance services help organizations interpret and implement CRA requirements efficiently. While tools handle execution, services guide strategy.
Common support areas:
- Gap analysis and readiness assessment
- Policy and documentation development
- Secure development lifecycle design
- Audit preparation and reporting
In our experience, organizations benefit most when services act as enablers, not dependencies, helping internal teams build long-term capability.
“Cybersecurity involves protecting systems, networks, and programs from digital attacks.” – Wikipedia
FAQ
What Is The First Step In CRA Practical Implementation?
The first step is aligning your development lifecycle with CRA requirements. This includes defining security policies, integrating Secure Coding Practices, and ensuring all teams understand their role. Without this foundation, tools and checklists become ineffective because there is no consistent framework guiding their use.
How Often Should A Secure Coding Checklist Be Used?
Ideally, the checklist should be applied continuously, during development, code reviews, and testing. It is not a one-time validation tool. Teams that embed it into CI/CD pipelines and daily workflows achieve better consistency and fewer compliance gaps.
Are Tools Enough For CRA Compliance?
No, tools alone are not sufficient. While they automate detection and monitoring, human oversight is critical. Developers must understand security principles, and teams must review results contextually. Tools support implementation, but discipline ensures effectiveness.
When Should Companies Consider Compliance Services?
Organizations should consider compliance services when they lack internal expertise or need structured guidance. This is especially useful during early implementation or audit preparation. However, the goal should always be to build internal capability rather than rely entirely on external support.
Turning CRA Into Daily Practice
Practical implementation of the Cyber Resilience Act is about consistency, not complexity. By embedding security into development through structured workflows, checklists, and tools, teams can meet compliance requirements without slowing innovation.
We’ve seen that starting with Secure Coding Practices creates a strong foundation for everything else. If you want sustainable compliance and stronger software, begin integrating Secure Coding Practices into your daily workflow today.
References
- https://en.wikipedia.org/wiki/Secure_coding
- https://en.wikipedia.org/wiki/Computer_security
