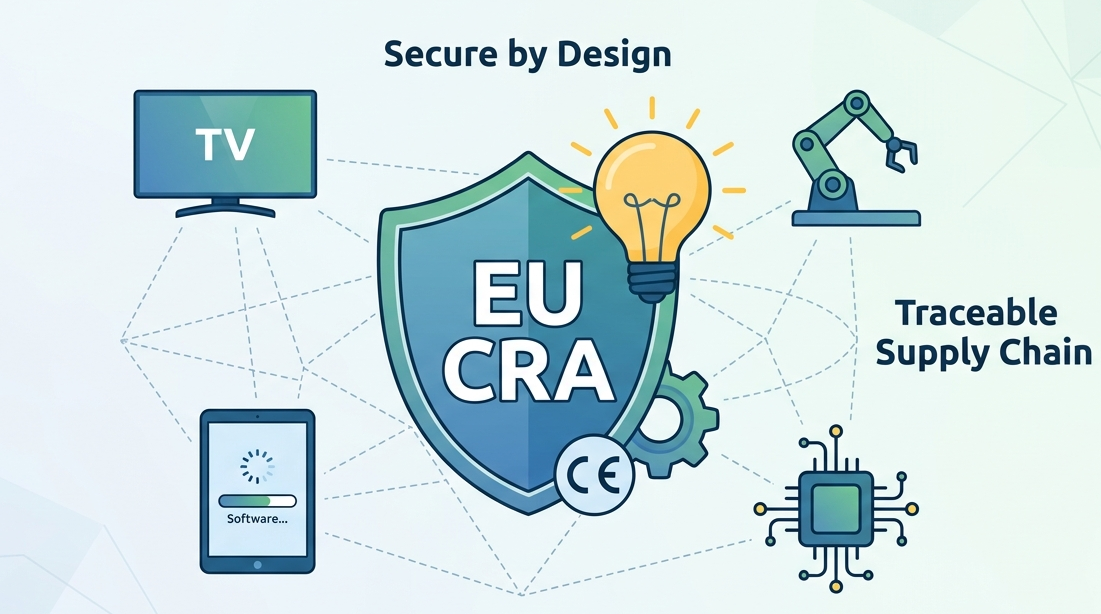
If your business sells digital products in the EU, cybersecurity can no longer be optional. The EU digital product security rules, led by the Cyber Resilience Act (CRA), require that every product with digital elements, from smart appliances to industrial control systems, is secure by design, maintained throughout its lifecycle, and transparent across the supply chain.
We’ve experienced firsthand how integrating security early, including Secure Coding Practices, helps prevent vulnerabilities and keeps products compliant while building customer trust.
Key Insights on EU Digital Product Security Rules
Here’s a concise overview of the main obligations, practical actions, and timelines to help your products stay secure, compliant, and ready for the European market.
- The CRA makes security-by-design and default mandatory for all products with digital elements.
- Manufacturers must provide security updates and structured incident reporting, starting in September 2026.
- Non-compliance risks include fines, recalls, and CE mark revocation.
Products Covered by the CRA
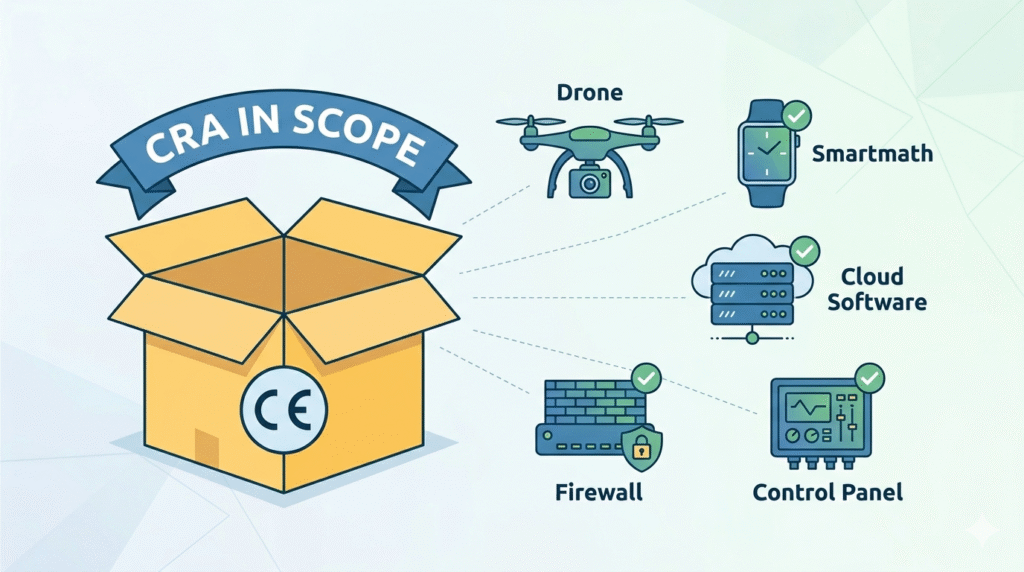
The CRA applies broadly, and understanding the scope applicability is essential for any hardware or software developer. Specifically:
- Consumer IoT devices: smart TVs, wearables, cameras
- Industrial systems: robotics, sensors, medical-device software
- Software and cloud services with embedded code
- Components: microprocessors, firewalls
We prioritize Secure Coding Practices early in the design phase to minimize vulnerabilities and ensure lifecycle resilience.
| Product Type | CRA Requirements | Practical Action |
| Consumer IoT | Security-by-design, updates, incident reporting | Internal testing, self-assessment |
| Industrial Systems | Security-by-design + criticality assessment | Third-party conformity assessment for critical products |
| Software/Cloud Services | Secure lifecycle, privacy protection | Secure coding, automated scans, SBOM |
Security-by-Design and Default
The CRA requires that security shapes the product from concept to delivery. Key obligations:
- Security risk assessment: Identify threats and vulnerabilities.
- Secure Coding Practices: We integrate these from day one.
- Secure defaults: Disable open ports and default passwords.
- Data minimization: Collect only necessary data.
“Two major problems adding costs for users and society should be addressed: a low level of cybersecurity of products with digital elements, reflected by widespread vulnerabilities and the insufficient and inconsistent provision of security updates to address them, and an insufficient understanding and access to information by users, preventing them from choosing products with adequate cybersecurity properties or using them in a secure manner.” – European Commission
This ensures products are secure when unboxed and maintain integrity throughout their lifecycle.
Updates, Vulnerability Handling, and Incident Reporting
Credits: Hogan Lovells
Security doesn’t end at delivery:
- Automatic security updates for the product lifetime.
- Vulnerability handling: Receive reports, validate, remediate quickly.
- Incident reporting: Starting 11 September 2026, severe incidents must be reported:
- 24h: Early warning
- 72h: Full incident report
- 14d / 1 month: Root cause and remediation
Secure Coding Practices reduce the likelihood of incidents and support fast remediation.
Supply Chain Responsibilities
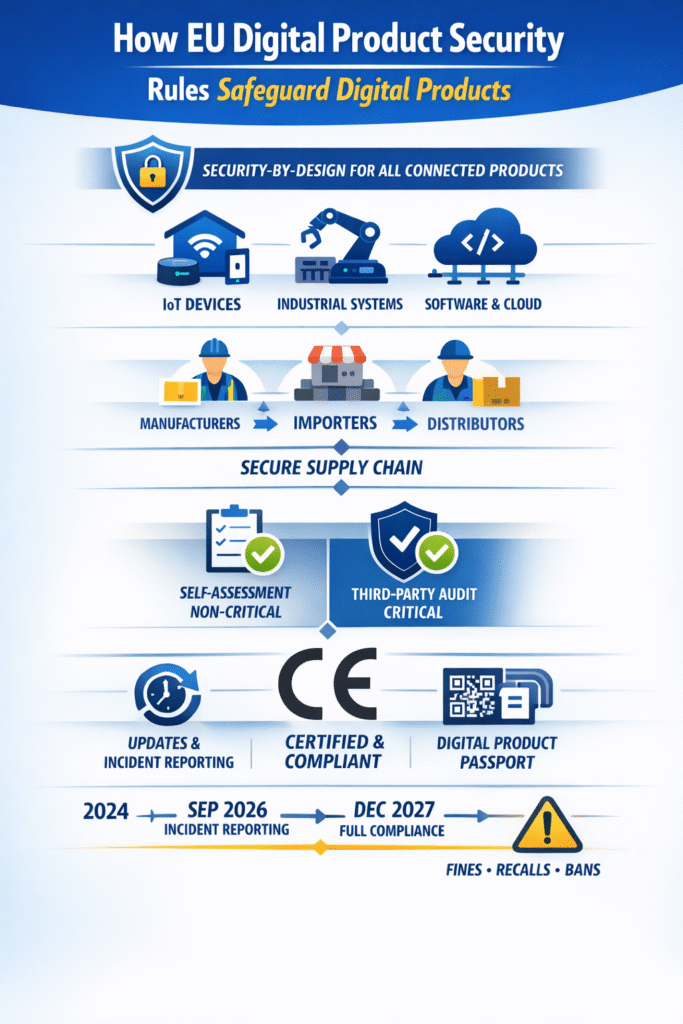
The CRA spreads responsibility across the supply chain, making it vital to determine who must comply with specific obligations:
- Manufacturers: Ensure compliance, technical documentation, CE marking.
- Importers: Verify compliance before market entry.
- Distributors: Avoid supplying obviously non-compliant products.
Transparency in material composition, software versions, and end-of-life instructions ensures resilience across Tier-1 suppliers and deep supply networks.
Certification and Critical Product Classification
Not all products are equal:
- Non-critical: Self-assessment with internal documentation.
- Critical: Products affecting safety or infrastructure require third-party conformity assessment.
“The vulnerability handling obligations set out in this Regulation, which manufacturers have to comply with when placing a product with digital elements on the market and for the support period, apply to products with digital elements in their entirety, including to all integrated components.” – ENISA
CE marking signals compliance and security readiness to consumers and partners.
Integration with Digital Product Passport
Digital Product Passports (DPPs) enhance security and transparency:
- Track material origin, software versions, carbon footprint, and repairability
- Accessible via QR codes or RFID/NFC tags
- Combine with Secure Coding Practices to unify cybersecurity and sustainability compliance
Timelines and Non-Compliance Risks
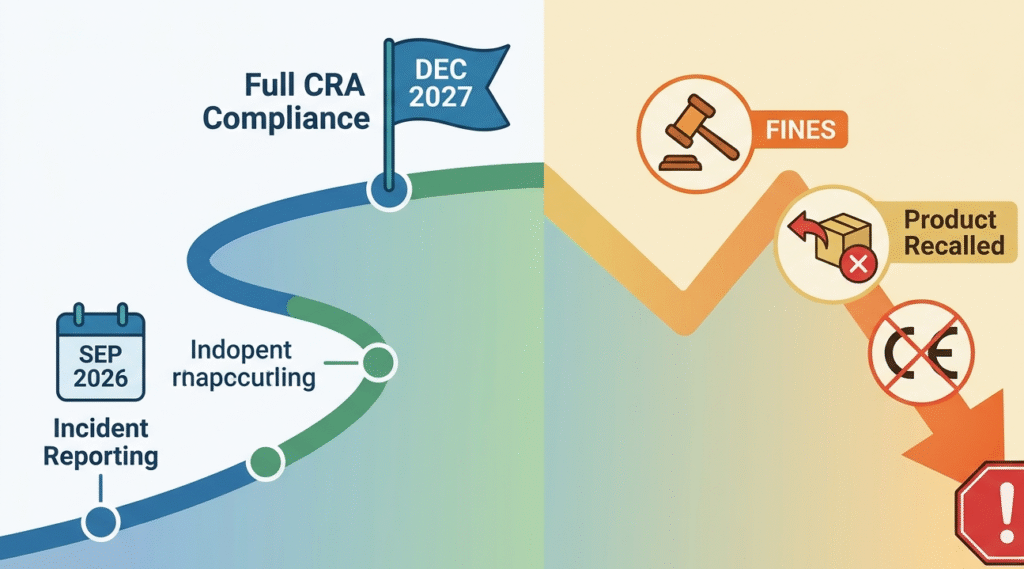
- 11 September 2026: Incident reporting starts
- 11 December 2027: Full CRA compliance mandatory. Organizations must be prepared for when cyber resilience act applies to their specific product lifecycle. Failure to comply risks fines, market bans, and reputational harm. Treating security as a strategic, built-in process is critical.
Failure to comply risks fines, market bans, and reputational harm. Treating security as a strategic, built-in process is critical.
FAQ
How can businesses ensure supply chain transparency for digital products under EU regulations?
Businesses must maintain accurate supplier data and trace Tier-1 suppliers and deep supply networks. Using Digital Product Passports (DPP) with QR codes or RFID tags helps track material composition, product data, and end-of-life instructions.
This ensures compliance with the Cyber Resilience Act and supports product lifecycle monitoring while improving product transparency and regulatory reporting across the European Union.
What role does a Digital Product Passport play in managing product lifecycle data?
A Digital Product Passport centralizes product content management, material origin, carbon footprint, and sustainability credentials.
It allows economic operators to share supplier and process information across the supply chain, supports Circular Economy Action Plan goals, and ensures CE marking compliance. Accessible via QR codes or RFID + NFC, it helps businesses track lifecycle events, from production to end-of-life instructions, efficiently.
How should companies manage security updates for connected electronic and digital devices?
Under the Cyber Resilience Act, companies must implement continuous security updates for all electronic and connected devices. Tracking cyber threats and integrating a security solution ensures safe operation during the product lifecycle.
Proper regulatory reporting and documentation allow compliance with EU Cybersecurity Strategy and prevent financial penalties or market access denial, protecting both the business and users.
What information should be included in supplier and product data for compliance?
Supplier and process information, including raw materials, material composition, chemical compositions, and country of manufacturing, should be documented. Recording product identifier, carbon emissions data, and end-of-life instructions ensures product transparency and aids in corporate sustainability reporting.
Structured master data management allows supply chain actors to meet regulatory requirements under European Commission directives and supports Circular Economy initiatives.
Preparing Your Product Portfolio
Start now: map your products against CRA requirements, conduct risk assessments, and verify suppliers’ secure development practices. Integrating Secure Coding Practices and traceable updates ensures products are robust, compliant, and ready for a connected European market.
To strengthen your team’s skills, consider the Secure Coding Practices Bootcamp, a hands-on 2-day course covering OWASP Top 10, secure authentication, encryption, and practical coding labs, equipping developers to build safer, compliant software from day one.
References
- https://digital-strategy.ec.europa.eu/en/policies/cyber-resilience-act
- https://www.enisa.europa.eu/topics/product-security-and-certification

