A law from the European Union, the Cyber Resilience Act (CRA), will force strict cybersecurity rules on connected products sold there. It starts in 2027.
The law applies to connected devices: smart products, factory machines, and programs. It aims for security baked into the original design and kept up with patches over time. Any business that manufactures, imports, or modifies these products for the EU market must comply. This holds true for companies operating outside Europe as well.
Find out more about who it affects and what developers need to do next.
What the CRA Scope Covers at a Glance
Before looking deeper, here’s the short version of what the Cyber Resilience Act (CRA) actually covers.
- The Cyber Resilience Act applies to almost all hardware and software with digital connectivity sold in the EU market.
- Compliance affects manufacturers, software vendors, importers, and distributors worldwide, not only EU-based companies.
- High-risk digital products face stricter conformity assessments and third-party audits before entering the EU market.
Scope of the EU Cyber Resilience Act
The EU Cyber Resilience Act, or CRA, covers most hardware and software products that connect to a network and are sold in the EU. It’s a central part of Europe’s cybersecurity rules.
The European Commission designed the CRA as a broad law, not one aimed at a single industry. Under their digital strategy, products must meet security requirements before they can legally be sold in Europe.
As highlighted by DLA Piper
“The reach of the proposed CRA is broad, covering all [products with digital elements] whose intended and reasonably foreseeable use includes a direct or indirect logical or physical data connection to a device or network.” – DLA Piper
Most things with any kind of connectivity are included. This means consumer electronics, business networking gear, and industrial control systems.
Even products sold globally are affected. If your company sells a connected product in Europe, you have to follow this regulation.
Products within the scope include:
- IoT devices like smart home hubs, cameras, and wearables.
- Networking infrastructure such as routers, firewalls, and VPN appliances.
- Industrial systems, including PLCs, SCADA interfaces, and edge gateways.
- Cloud-connected software and SaaS platforms delivered with digital products.
These categories show that the CRA targets the whole connected ecosystem, from the firmware up to big applications.
Who Must Comply with the Cyber Resilience Act
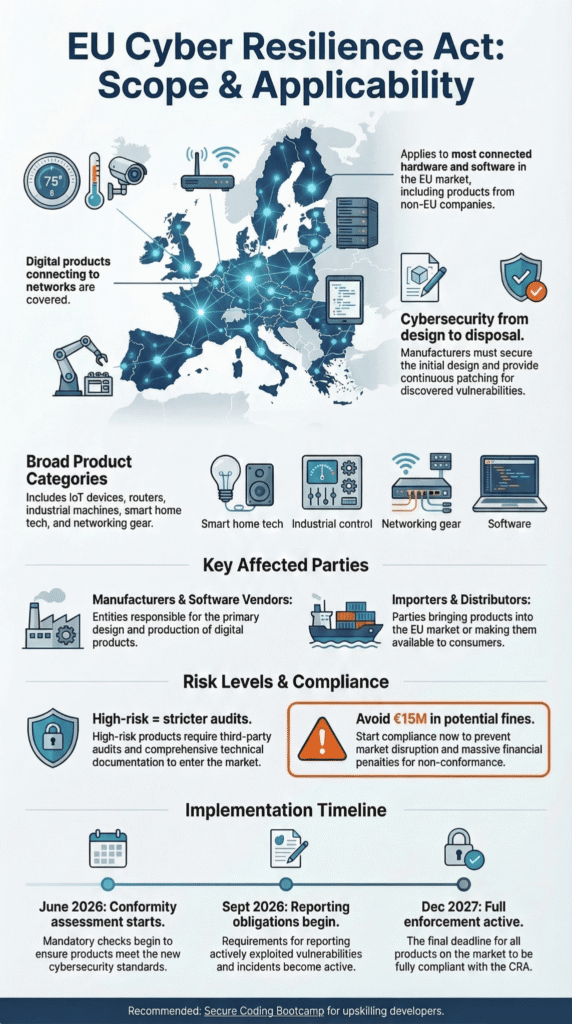
If you put a connected product on the EU market, you must comply with the CRA. This includes manufacturers, importers, distributors, and software vendors responsible for products that comply with the Cyber Resilience Act before entering the EU market.
The regulation clearly defines duties for each type of business operator. The law covers every step of the supply chain.
Manufacturers carry the biggest load. Their job is to build security into products from day one, maintain good documentation, and run a solid process for dealing with vulnerabilities.
Importers and distributors aren’t off the hook. They’re legally required to verify that the product has the proper CE marking and has cleared its conformity assessment.
The main players who must comply are:
- Manufacturers of connected hardware or embedded systems.
- Software vendors for desktop apps, firmware, or cloud platforms.
- Importers bringing foreign digital products into the EU.
- Distributors and resellers, like online marketplaces.
This means non-EU manufacturers have to comply even if they operate outside Europe. Getting into the market depends on meeting the CRA’s rules.
Here’s a simpler table to summarize what each party needs to do.
| Economic Operator | Primary Responsibility | Example |
| Manufacturers | Secure product design, risk assessment, lifecycle security support | IoT device makers |
| Importers | Verify CE marking and compliance documentation | EU importers of foreign routers |
| Distributors | Ensure products sold are compliant and documented | Retailers and resellers |
| Software vendors | Secure development lifecycle and vulnerability handling | SaaS platforms and software products |
This setup makes sure everyone in the supply chain is accountable, from the designers to the sellers.
From our perspective as a training bootcamp, this is a big shift. We teach secure development, and now our students and clients will have a legal framework pushing them toward the practices we’ve always advocated. It makes our curriculum more relevant, frankly.
When the Cyber Resilience Act Applies
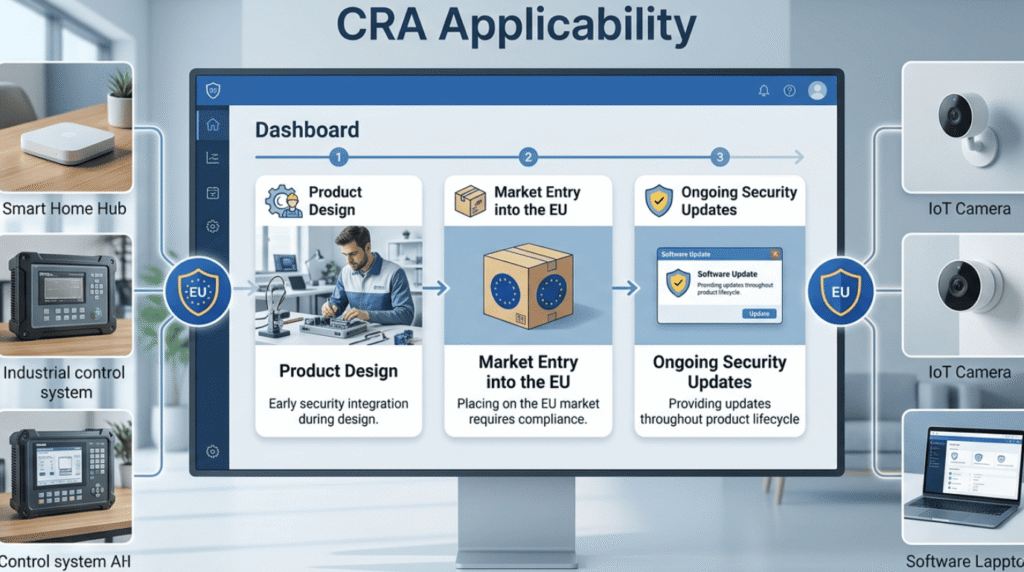
The Cyber Resilience Act applies when a connected digital product is made commercially available in the European Economic Area. This means it’s sold, distributed, or offered there.
The law focuses on “products with digital elements.” That’s any hardware or software that can connect to a network or another device, either directly or indirectly.
It applies to the final gadget you sell and the software inside, the embedded firmware, and the services that deliver updates to it.
In a recent analysis by the International Bar Association
“The CRA follows the so-called ‘marketplace principle’. This means that the regulation applies to any product made available on the EU internal market, whether for payment or free of charge, as long as it is made available in the context of a commercial activity.” – International Bar Association
Common examples include consumer gadgets, industrial machinery, and business software.
Typical products covered are:
- Smart home devices and wearables that connect to the internet.
- Industrial control systems, like SCADA and programmable logic controllers (PLC).
- Networking infrastructure, such as routers, firewalls, and identity management platforms.
- Cloud-connected management software tied to a physical product.
Some products fall under different, specialized rules.
Things like medical devices, cars, and aviation tech have their own EU cybersecurity frameworks. A Harvard Health analysis stresses that strong security is still vital under these overlapping rules.
Companies must check for sectoral regulations overlap to know which cybersecurity regime applies.
Full CRA enforcement begins in 2027, giving businesses time to align their secure development and product lifecycle support practices.
Cyber Resilience Act High-Risk Products
Credits: Codific
The CRA sorts digital products into risk-based categories. Systems deemed “high-risk” face stricter rules.
The law’s high-risk category covers products that run critical network functions or security services. A failure or breach here can lead to serious outages.
ENISA flags technologies with higher risk due to their crucial role.
Products often flagged as high-risk include:
- Routers, firewalls, and VPNs.
- Systems managing logins and keys.
- Industrial controllers like PLCs and SCADA.
- Corporate security policy tools.
For these products, compliance often requires a third-party conformity assessment done by a certified notified body. You can’t just self-declare that you meet the rules.
High-risk classifications also demand more paperwork: extensive technical documentation, threat modeling, and evidence from security testing.
If you’re building these systems, you need to start preparing now. In our training, we see that compliance usually requires mature DevSecOps practices, a solid process for handling vulnerabilities, and evidence that’s ready for an audit. It’s a lot of work, but it’s the new baseline for selling these products in Europe.
Core EU Digital Product Security Rules
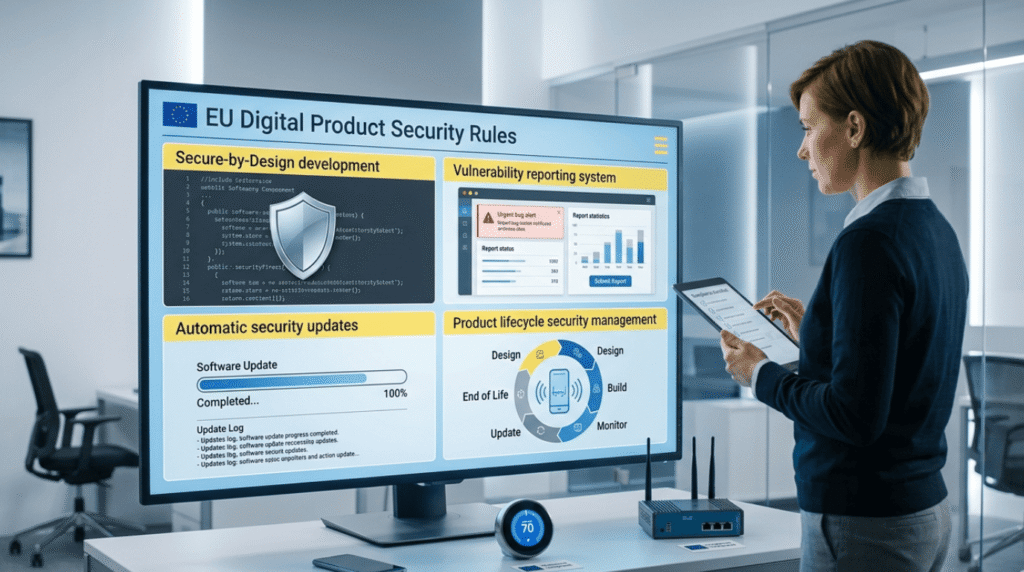
The Cyber Resilience Act lays down mandatory security rules for every covered digital product.
These rules are spelled out in Annex I requirements. They set cybersecurity standards for the entire product lifecycle, from design to disposal.
The law demands secure-by-design development, baking security in from the beginning. It also mandates continuous vulnerability management and monitoring after the sale.
According to the European Union Agency for Cybersecurity (ENISA), the goal is to make security a core part of product design, not something tacked on later.
Before a product can be sold, manufacturers have to do a formal risk assessment.
The key product security requirements include:
- Secure-by-design architecture and secure default configurations.
- Data minimization and encryption standards to protect user information.
- Protection against common vulnerabilities, like injection attacks and buffer overflows.
- Authenticated update mechanisms for automatic security patching.
Products must have reliable vulnerability handling processes.
Manufacturers are required to maintain a software bill of materials (SBOM), which is an inventory tracking every third-party component and open-source library used in the product.
There are more obligations over the product’s life. Companies must report incidents to ENISA within 24 hours, continuously monitor for new vulnerabilities, and provide security updates for the entire declared support period.
They also have to keep technical documentation and cybersecurity evidence for at least 10 years. This lets authorities check compliance long after the product hits the market.
EU Cyber Compliance Basics for Developers
For developers and product teams, the CRA makes modern secure development lifecycle practices a legal requirement.
Software engineers now have to incorporate security from the very beginning. This means doing threat modeling, setting up code review gates, and running automated security tests.
The regulation lines up closely with the DevSecOps practices many big tech companies already use.
Key development practices needed for CRA compliance are:
- Threat modeling and risk assessment during system design.
- Dependency scanning and open-source tracking for supply chain security.
- Static and dynamic testing tools like SAST and DAST.
- Secure update mechanisms with integrity checks and fail-safe deployment.
Teams also need to set up incident response workflows and have a vulnerability disclosure policy ready.
Developers must maintain component inventories and SBOM documentation. This is crucial for quickly identifying when a library you use becomes vulnerable.
Another important step is declaring a support period. You have to state clearly how long the product will receive security updates.
In our training, we see this shift clearly. These requirements change security from a “nice-to-have” best practice into a legal obligation. If you want EU market access, you have to do it. It’s pushing the entire industry toward the standards we teach.
FAQ
What products fall within the scope of the Cyber Resilience Act?
The Cyber Resilience Act applies to many digital elements products sold in the EU. These products include IoT devices, connected hardware, cloud-connected software, and embedded systems.
The EU cybersecurity law also covers routers, firewalls, VPN appliances, and smart home devices. Industrial technologies such as industrial control systems, SCADA systems, and PLCs are included because they perform critical network functions. These digital product rules aim to improve hardware cybersecurity, strengthen software security mandates, and protect systems that connect to digital networks.
Who must comply with CRA requirements when selling digital products in the EU?
Several parties must follow CRA compliance under the EU cyber compliance framework. Manufacturers’ obligations apply first because manufacturers design and produce digital elements products. Importers’ duties require importers to verify that products meet the EU cybersecurity law before entering the EU market.
Distributors’ responsibilities require distributors to check product compliance before sale. Software vendors and non-EU manufacturers must also comply if they place products in the EU market. In addition, online marketplaces liability and resellers obligations may apply when digital products are sold through online platforms.
How does the Cyber Resilience Act classify high-risk digital products?
The Cyber Resilience Act defines high-risk categories based on possible cybersecurity impact. Products such as identity management systems, access control systems, and tools that manage cryptographic keys may fall into this category.
Industrial technologies, including industrial control systems, SCADA systems, and safety-critical systems, may also qualify when they control operations that could cause serious disruption. These products must undergo stricter conformity assessment procedures.
Authorities may require third-party audits and evaluation by notified bodies before the product receives CE marking and enters the EU market.
What security requirements must products meet before entering the EU market?
Products must meet several pre-market obligations under the Cyber Resilience Act. Developers must apply secure-by-design practices during the secure development lifecycle. Security work includes risk assessment, threat modeling, and the use of DevSecOps practices during development.
Products must follow technical protections such as encryption standards, buffer overflow protection, and injection prevention. Companies must also prepare technical documentation and demonstrate compliance with Annex I requirements during the conformity assessment process.
What penalties apply if companies fail to meet Cyber Resilience Act requirements?
Companies that ignore the EU cybersecurity law may face serious CRA penalties. Regulators can impose cybersecurity fines of up to 2.5 percent turnover for major violations. Authorities may also require corrective actions through post-market surveillance and mandatory incident reporting.
Companies must perform proper vulnerability handling, deliver timely security updates, and maintain strong patch management. If a serious incident occurs, organizations may need to complete an ENISA notification as part of the enforcement process.
Why the CRA Scope Matters for Developers and Product Teams
By 2027, security will not be a choice. Every device and app must be built to stay safe. The Cyber Resilience Act makes that clear. But this is not just about rules. It is about people. The router in a home. A sensor in a hospital. A system in a factory. Each one holds real trust. So the question is simple: will your product protect the people who use it?
The teams that start now will lead tomorrow. Waiting is risky. Skills matter more than promises. If you want your developers to build safer code from day one, join the Secure Coding Practices Bootcamp and learn how to make security part of every release.
References
- https://privacymatters.dlapiper.com/2024/11/eu-cyber-resilience-act-published-in-eu-official-journal/
- https://www.ibanet.org/raising-the-bar-on-cybersecurity-European-Cyber-Resilience-Act

